"The ease of setup and use for both administrators and users was immediately apparent. The automated training and phishing awareness features are major time savers for HR and IT teams”

CyberHoot delivers tremendous value to businesses and Managed Service Providers (MSPs) through a steady stream of...
Read more
How to Allow-list in AppRiverIf you're using AppRiver's SpamLab spam filtering, you can add CyberHoot to your...
Read more
Detailed Instructions From...
Read more
The "My Assignments" section helps you stay on top of your training. You can: See which assignments are still...
Read more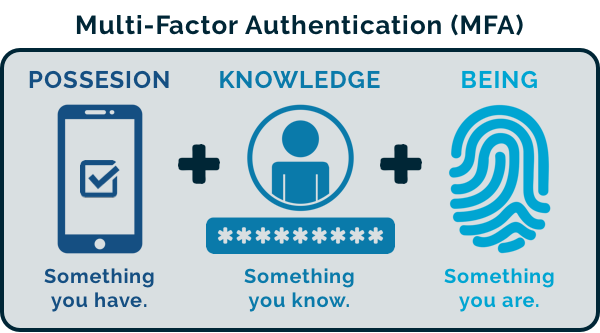
The Importance of Multi-Factor Authentication (MFA) into Cloud/SaaS Applications: CyberHoot recommends clients...
Read more
New CyberHoot businesses need to allow our training and phishing emails to reach their user's inboxes directly....
Read more
When Phish testing environments where Sophos EDR is present, you will need to enable allow listing and add the...
Read more
Adding users to CyberHoot's Power Platform via Azure AD/ Entra ID Sync (using Graph API) If your company uses...
Read more
The Entra ID sync is not functioning because the provided client secret has expired. To resolve this, you will...
Read more
Allow-Listing X-Headers is necessary in order for CyberHoot to send simulated phishing emails to bypass your...
Read more
High-Level Instructions: This HowTo video walks you through allow-listing CyberHoot’s Mail-Relay by either...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
