"CyberHoot lets us access expert cybersecurity guidance without hiring a full-time specialist."

Image Source Tokenization is a way for credit card information (also called the Primary Account Number or...
Read more
Image Source Continuity of Operations Plan (COOP) is a document that sets forth procedures for the...
Read more
Image Source A White Team is a group responsible for refereeing an engagement between a Red Team...
Read more
Network Segmentation is creating sub-networks within a corporate, enterprise, or another large network....
Read more
Ransomware is a type of malicious software designed to block access to a computer system, and more...
Read more
Access Control Access control is a security technique that regulates who or what can view or use...
Read more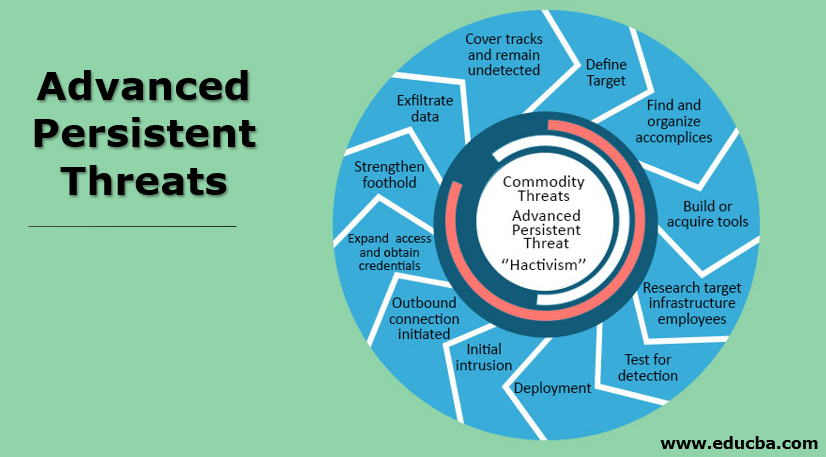
An Advanced Persistent Threat (APT) is an adversary that possesses sophisticated levels of expertise and...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
