"Cybersecurity training is complicated, partnering with CyberHoot keeps it simple. Our users are engaged with little administrative overhead."

Linkjacking is a practice used to redirect one website's links to another. Usually, this is...
Read more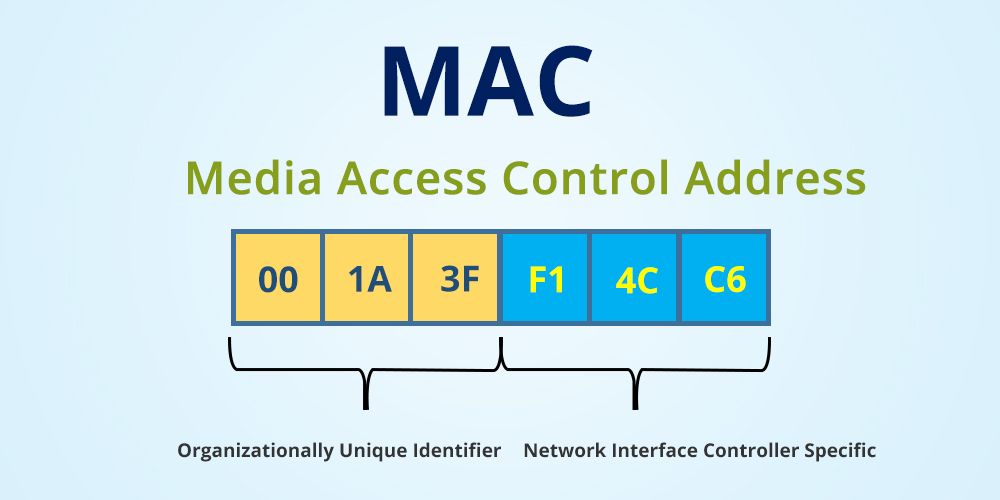
A Media Access Control (MAC) Address is a hardware identification number that is uniquely assigned to...
Read more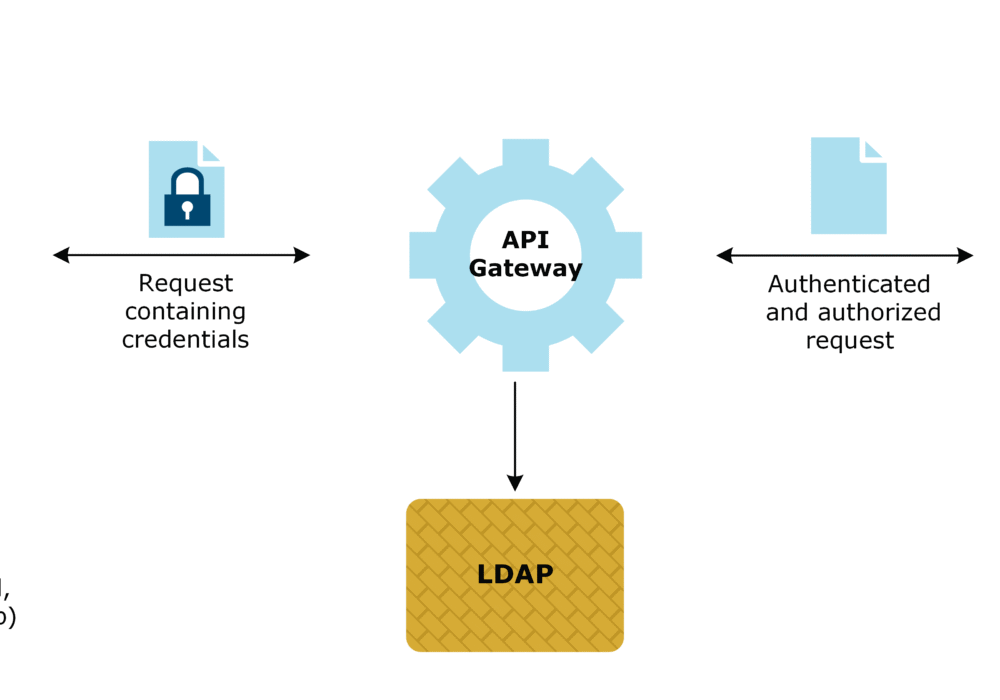
A Lightweight Directory Access Protocol (LDAP) is an open, vendor-neutral, industry standard...
Read more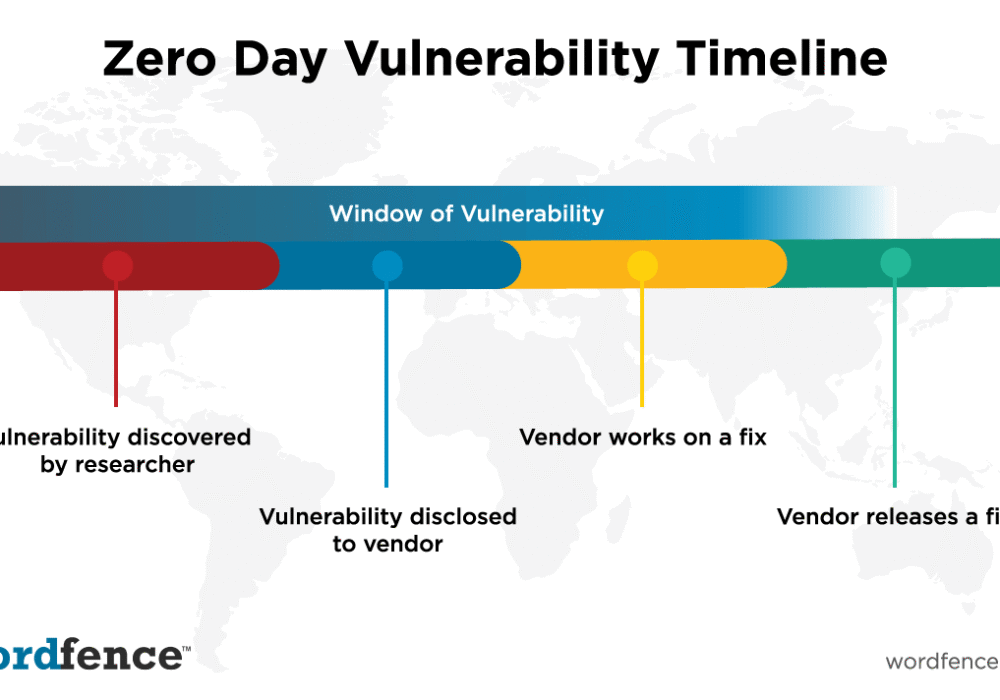
A Zero Day Vulnerability is a security flaw that is unknown to the software vendor or the...
Read more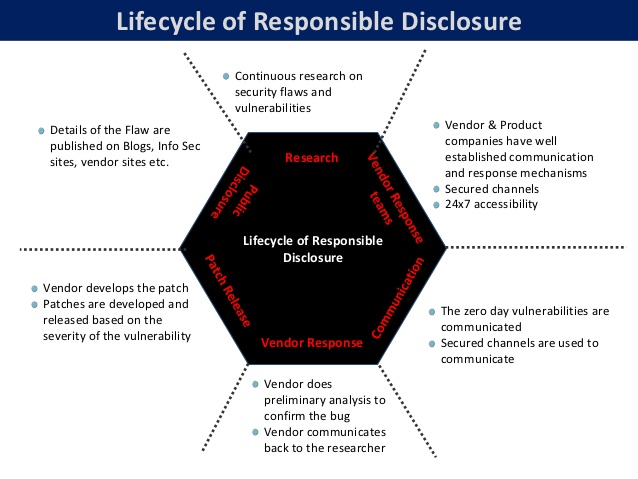
Responsible Disclosure refers to the best practice followed by most security researchers of not...
Read more
Revenge Porn is sexually explicit images or videos of a person posted online without that person's...
Read more
A Privileged User is a user of a computer who is authorized to bypass normal access control mechanisms,...
Read more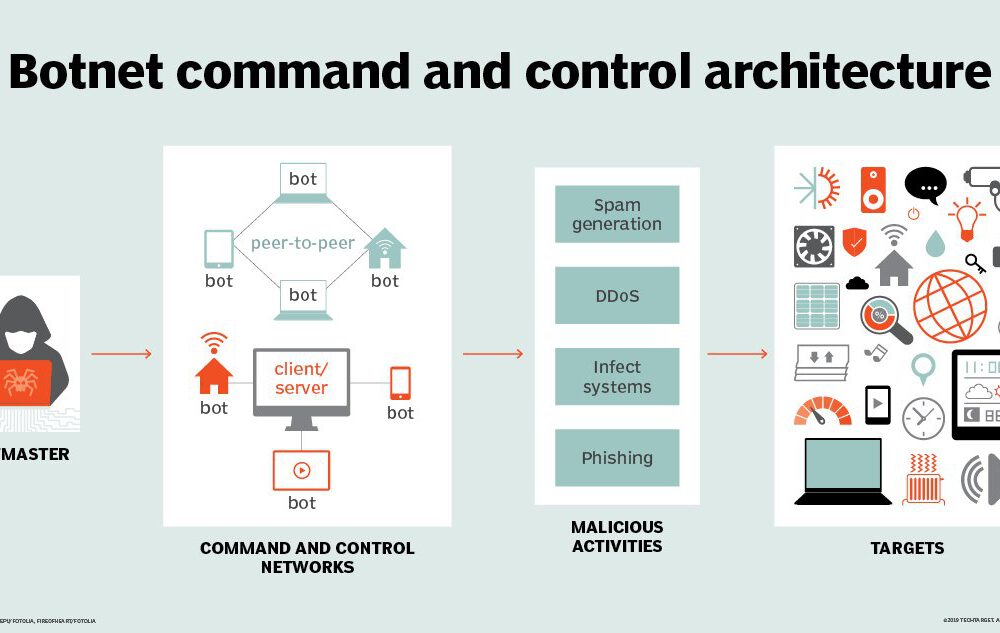
A Command and Control (C&C) Server is a computer being controlled remotely by a cyber criminal that...
Read more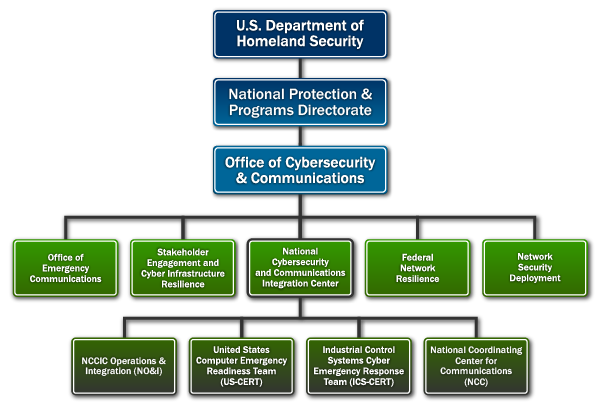
A Computer Emergency Response Team (CERT) is a group of security experts who respond to cybersecurity...
Read more
File Transfer Protocol (FTP) is a communications protocol used for transferring or exchanging files...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
