"Using CyberHoot was one of the best decisions we made regarding SAT. Fully automated, training is interesting, staff participation is high compared to other vendors."
Monthly Recurring Revenue (MRR) is the most important topic for Managed Service Providers (MSPs). MRR...
Read more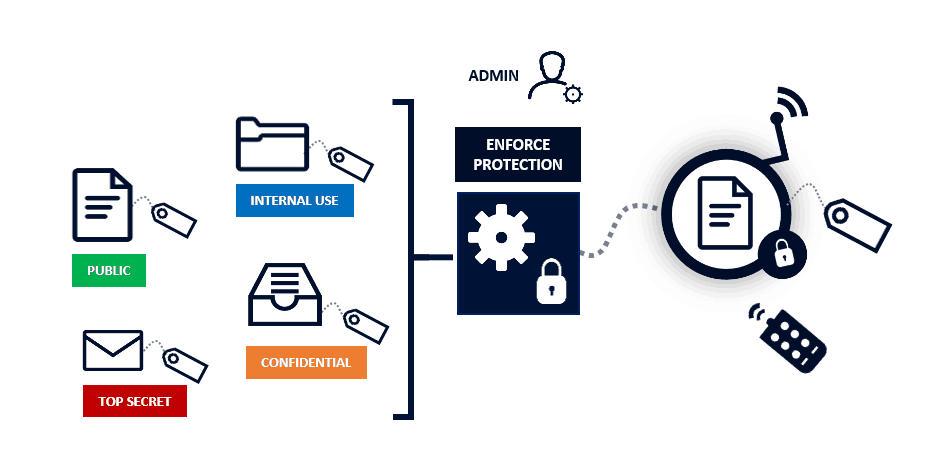
Data Classification is about categorizing data into buckets to make it easier to retrieve,...
Read more
Contact Tracing is a medical term which describes a process used to identify, trace, and contact people...
Read more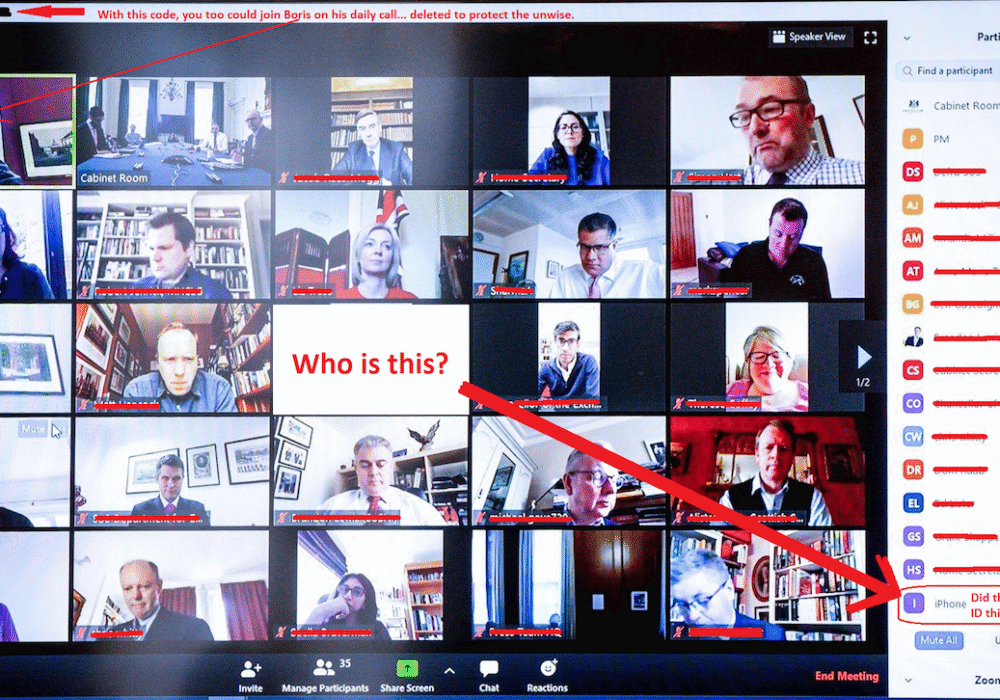
Zoom Bombing is where an unauthorized person enters your Zoom video conference to cause disruptions or to gain...
Read more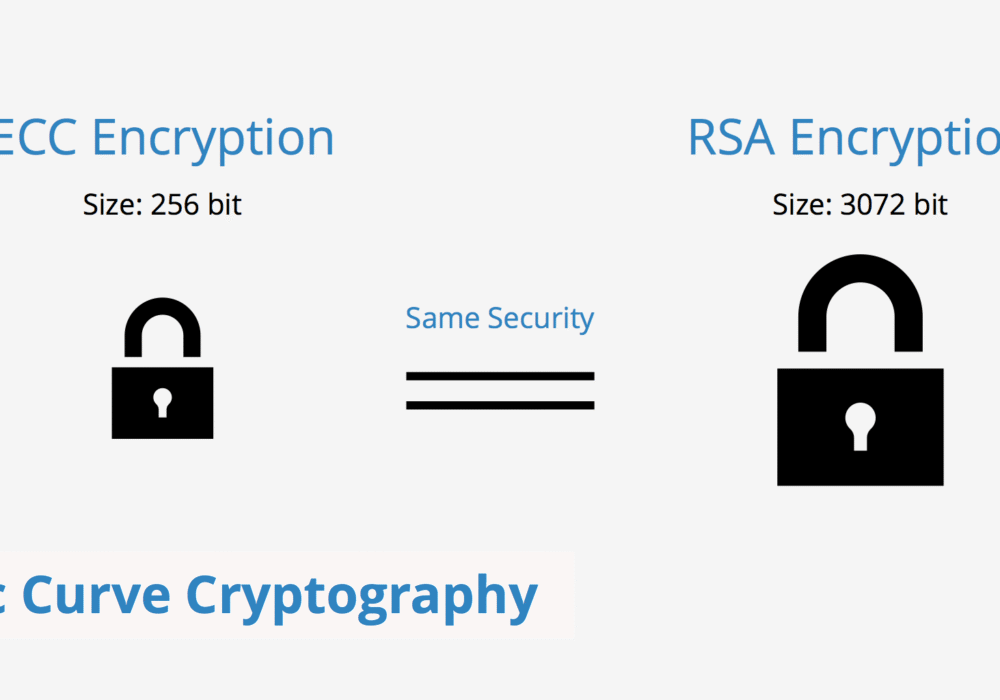
Elliptic Curve Cryptography (ECC) is a public key encryption method that is based on elliptic curve...
Read more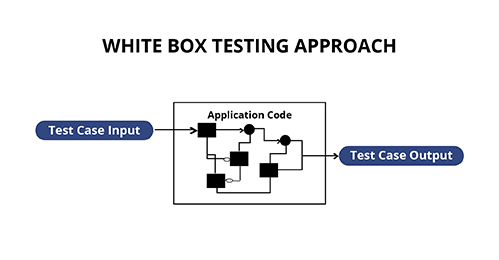
White Box Testing is a form of penetration testing which tests internal structures of an...
Read more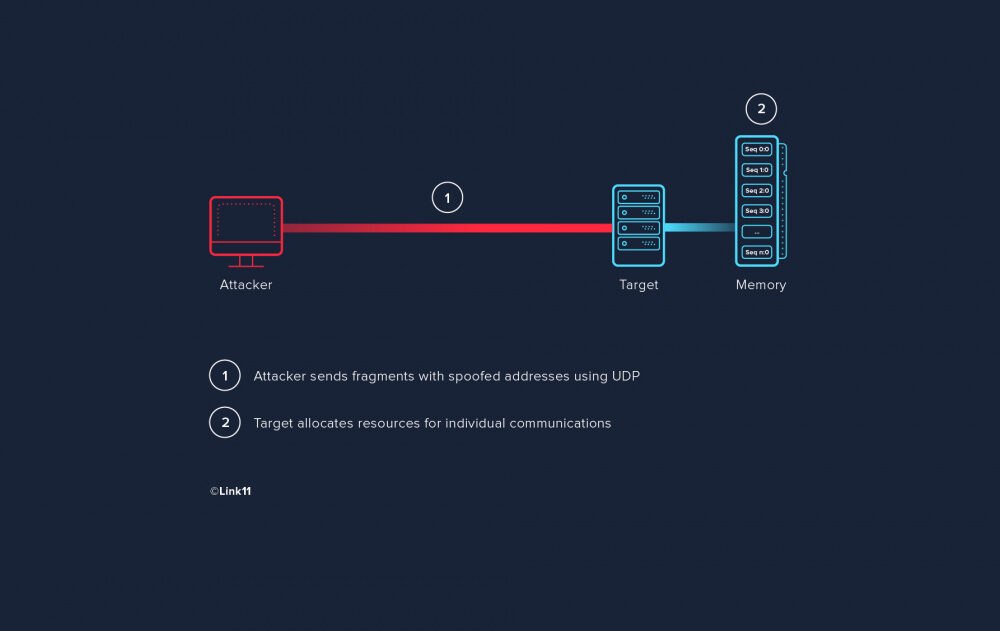
A Fragment Overlap Attack, also known as an IP Fragmentation Attack, is an attack that is based on how...
Read more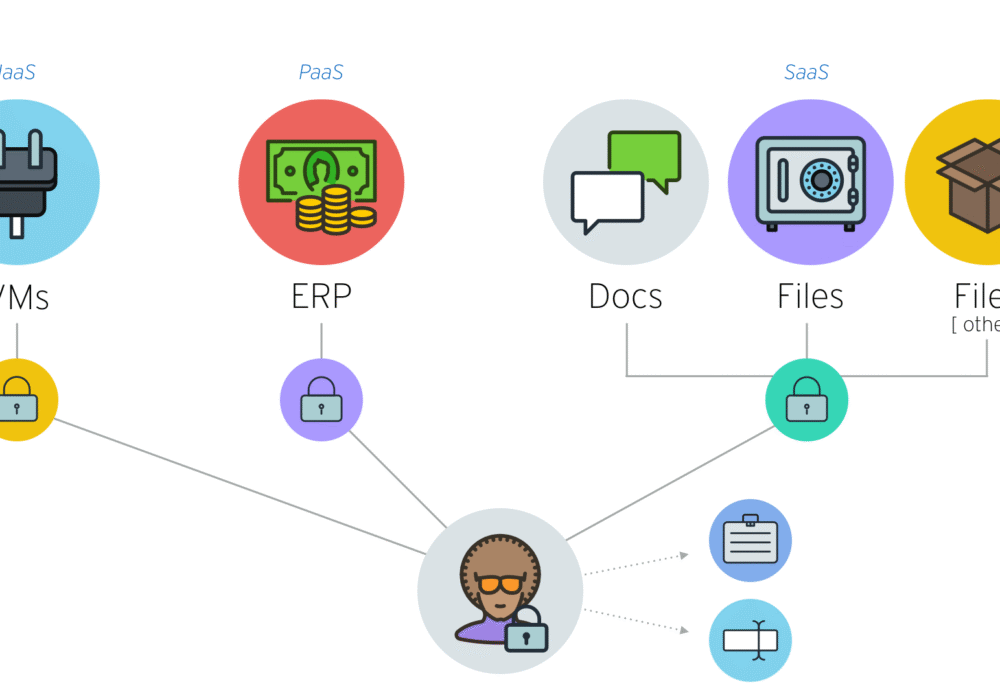
An Infrastructure as a Service (IaaS) is a cloud based service that helps companies build and manage...
Read more
A Platform as a Service (PaaS) is a type of cloud computing, similar to Software as a Service (SaaS),...
Read more
Steganography (pronounced: steh·guh·naa·gruh·fee) is the technique of hiding data secretly within an...
Read more
Software as a Service (SaaS) is a cloud-based service where instead of downloading software to your...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
