“Using CyberHoot was one of the best decisions we made regarding SAT. Fully automated, training is interesting, and staff participation is high compared to other vendors.”

A POS Intrusion is an attack that happens at the Point-of-Sale device. The POS device in retail stores...
Read more
Cyber Espionage is a cyber attack that leads to stolen classified, sensitive, or critical data often in...
Read more
Data Mining refers to the mathematical techniques used to exam large data sets including but not limited to...
Read more
A Cybersecurity Ecosystem is just like natural ecosystems. It is made up of a variety of...
Read more
Account Hijacking is where a hacker compromises a computer account that does not belong to them. ...
Read more
Password Sniffing is a hacking technique that uses a special software application that allows a hacker...
Read more
Closed Source is software that is generally not free, where the source code is safe and encrypted....
Read more
Open source software (OSS), unlike proprietary software, is software that keeps the code open so IT...
Read more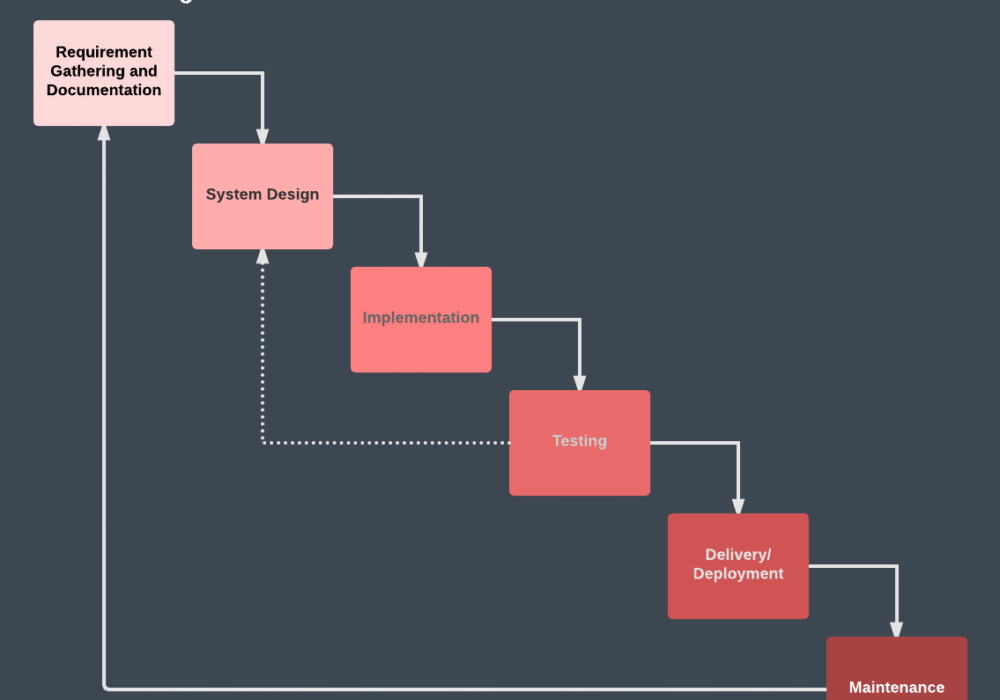
The Waterfall Development Methodology was the first process method used in the Software...
Read more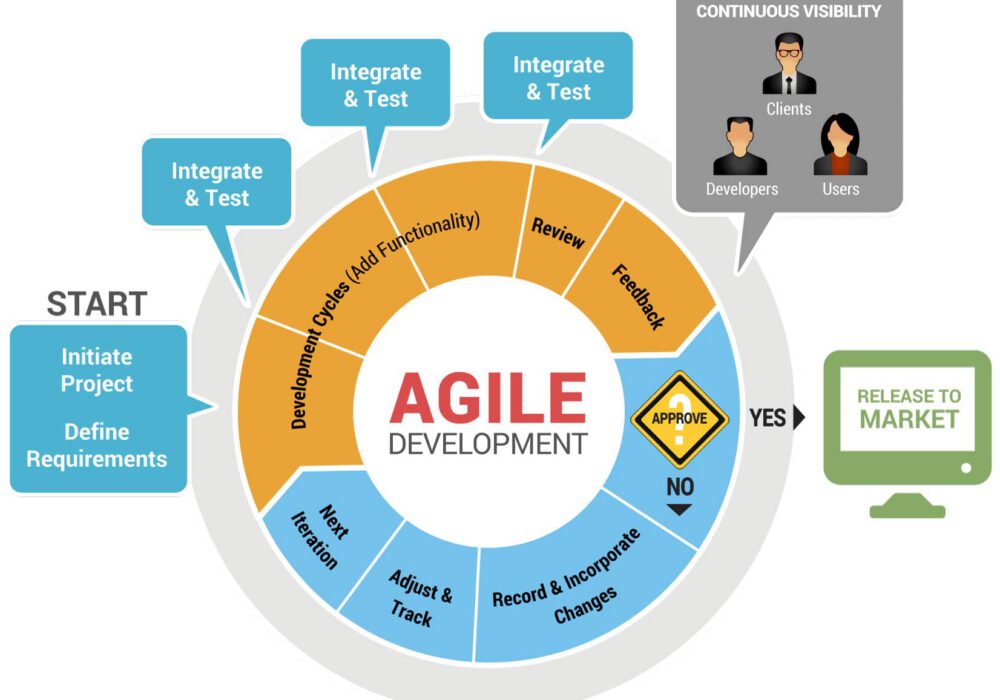
The Agile Development Methodology refers to a practice that uses continuous improvement and testing in...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
