"While it is well known that there are many cyber security threats, sorting out how to protect yourself without accidentally exposing yourself can be a daunting task. For a small organization like ours, this type expertise and time to research..."
Secure your business with CyberHoot Today!!! Sign Up Now Endpoint Detection and Response (EDR), also...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now The Health Insurance Portability and...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Controlled Unclassified Information (CUI) is...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now The Cybersecurity Maturity Model...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now A Purple Team is a group of cybersecurity...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Network Access Control (NAC) is the act of...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now AES Encryption, also known as Advanced...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Wiper Malware is malicious software that...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Fingerprints used in cryptography are short...
Read more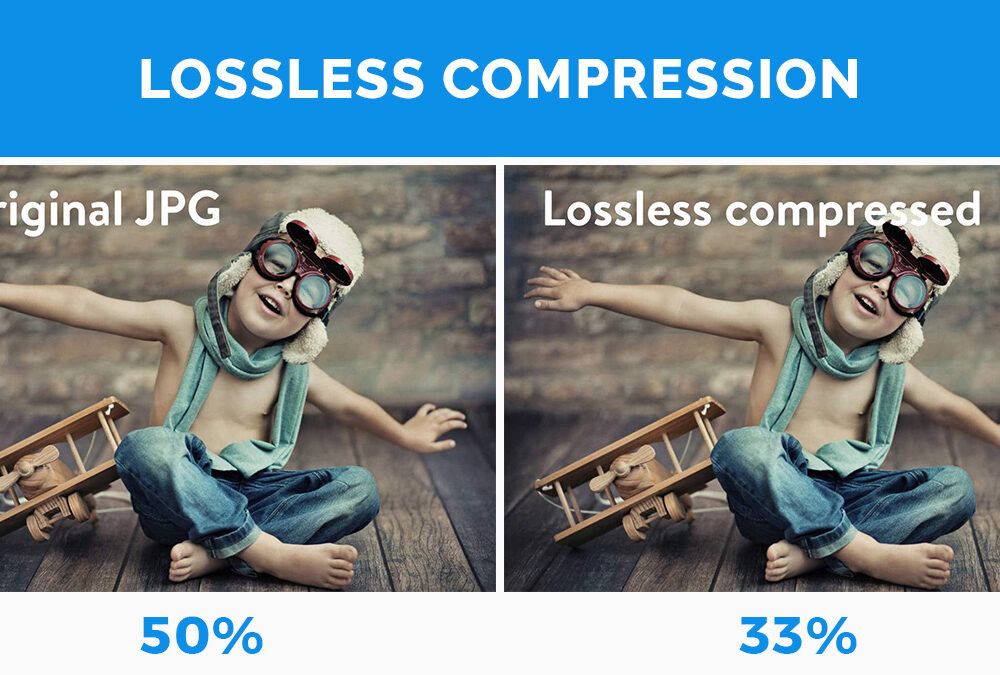
Secure your business with CyberHoot Today!!! Sign Up Now Lossless Compression is when file size is...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Lossy Compression is when data is lost or...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
