"While it is well known that there are many cyber security threats, sorting out how to protect yourself without accidentally exposing yourself can be a daunting task. For a small organization like ours, this type expertise and time to research..."
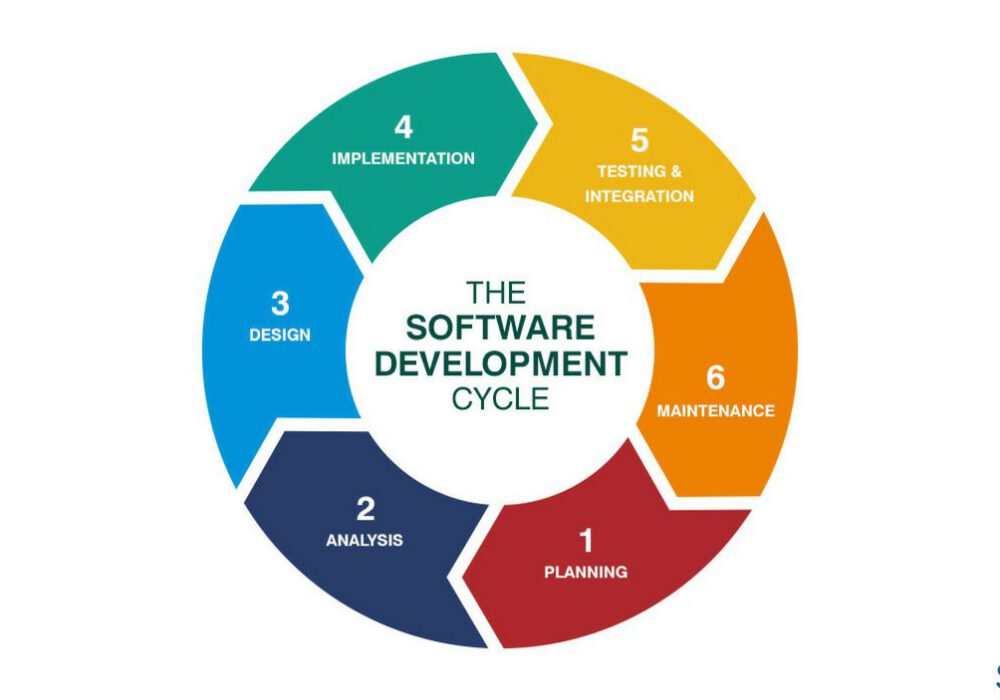
Software Development Life Cycle (SDLC) is the process companies follow to produces quality software in an...
Read more
OWASP stands for the Open Web Application Security Project. The OWASP Top 10 application security risks...
Read more
Email Impersonation is a form of phishing attack where a hacker impersonates someone else in the hopes it was...
Read more
MAZE Ransomware is a form of ransomware that poses a triple threat to your data security. With MAZE,...
Read more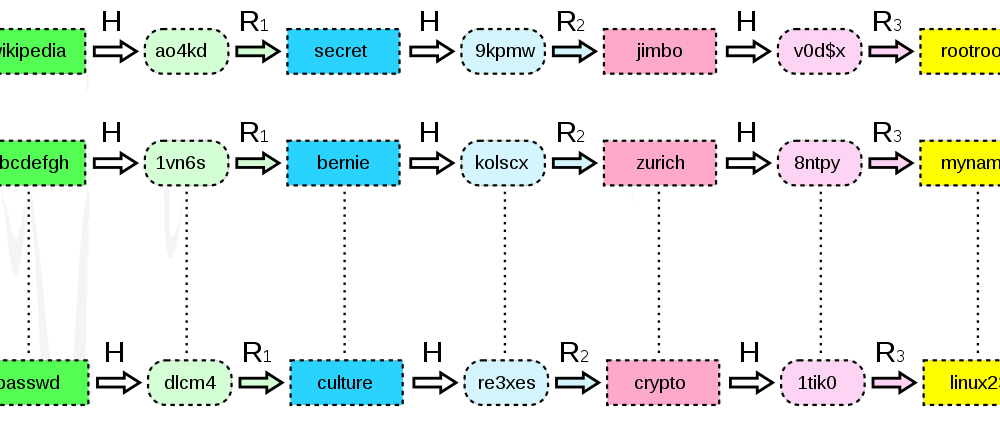
A Rainbow Table was a resource used for hacking the cryptographic hash functions in order to discover...
Read more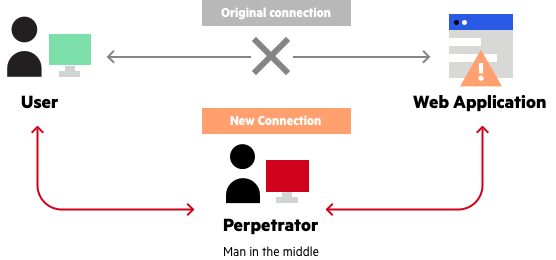
Adversary in the Middle (AITM) Attack (formerly referenced as Man-in-the-Middle) is a technical...
Read more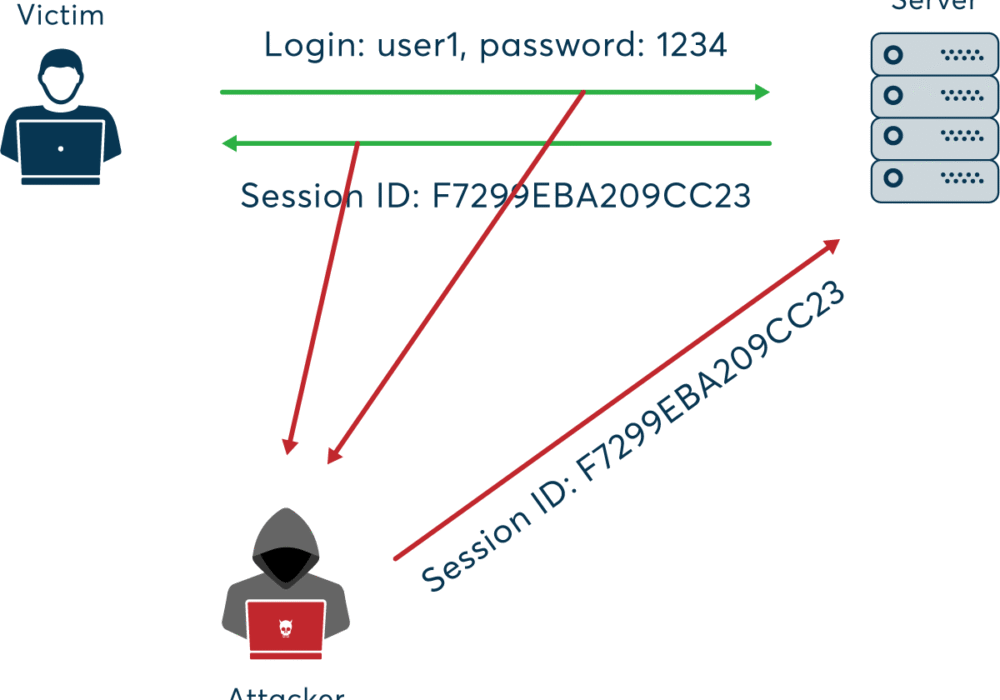
A Session Hijacking Attack occurs when a user session is taken over by an attacker. A normal session...
Read more
A Buffer Overflow Attack happens when a program tries to fill a block of memory (a memory...
Read more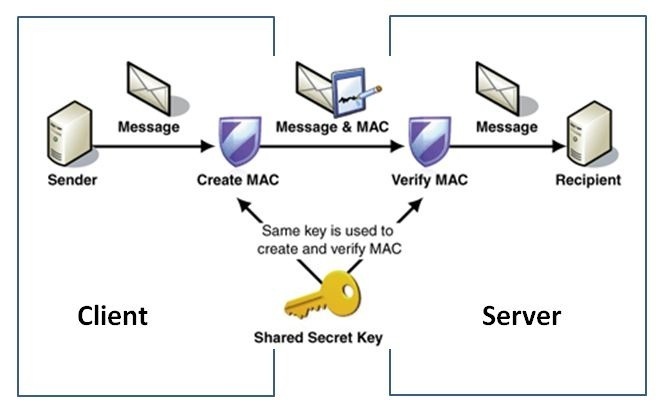
HMAC Authentication is short for Hash-Based Message Authentication Code, a strategy used to...
Read more
The Internet of Things (IoT) is any device or machine that has the ability to transfer data over a...
Read more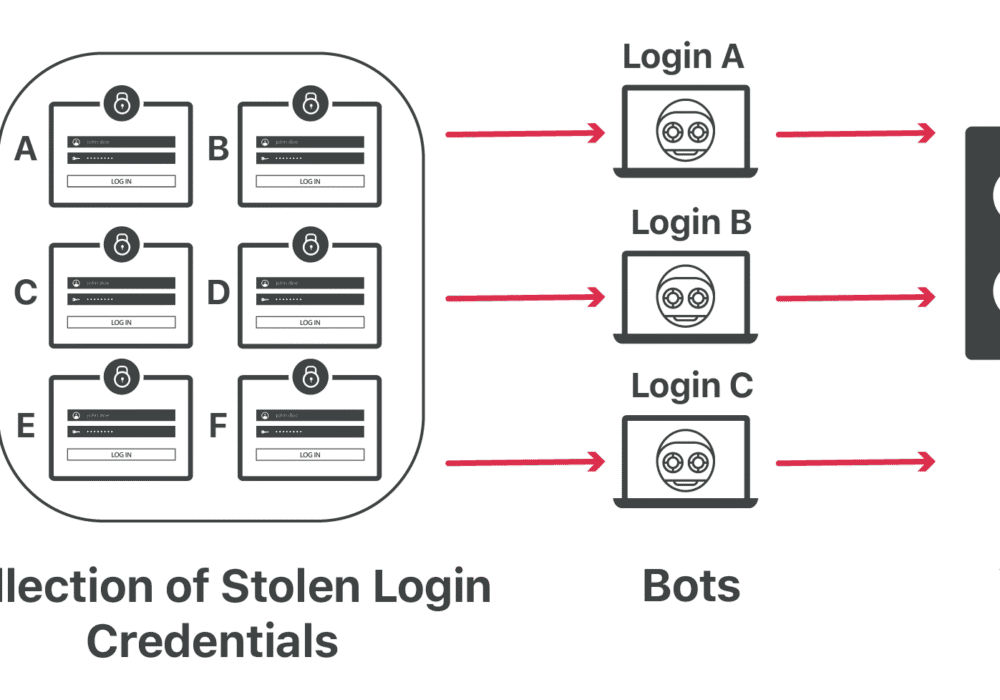
Credential Stuffing is the autonomous injection of stolen username and password credentials in a web...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
