"After 9 months of CyberHoot awareness training, a Financial Management firm with $4 Billion in assets was phish tested by the Fellsway Group. They had zero (0%) employees click on the phishing test. In contrast, the exact same phishing attack..."

A Critical Application is any system whose compromise would cause significant business, financial, legal, or...
Read more
Data Availability refers to ensuring that data and systems are accessible to authorized users when needed,...
Read more
Data Confidentiality is the assurance that information is only accessible to authorized individuals and is not...
Read more
Data Integrity is the assurance that information remains accurate, complete, and unaltered from its origin to its...
Read more
Information Systems (IS) are the organized collection, processing, maintenance, transmission, and dissemination...
Read more
A membership inference attack is a machine learning privacy attack in which an attacker tries to determine...
Read more
Chain of thought, or chain of thought prompting, is a prompt engineering technique where the user asks an AI...
Read more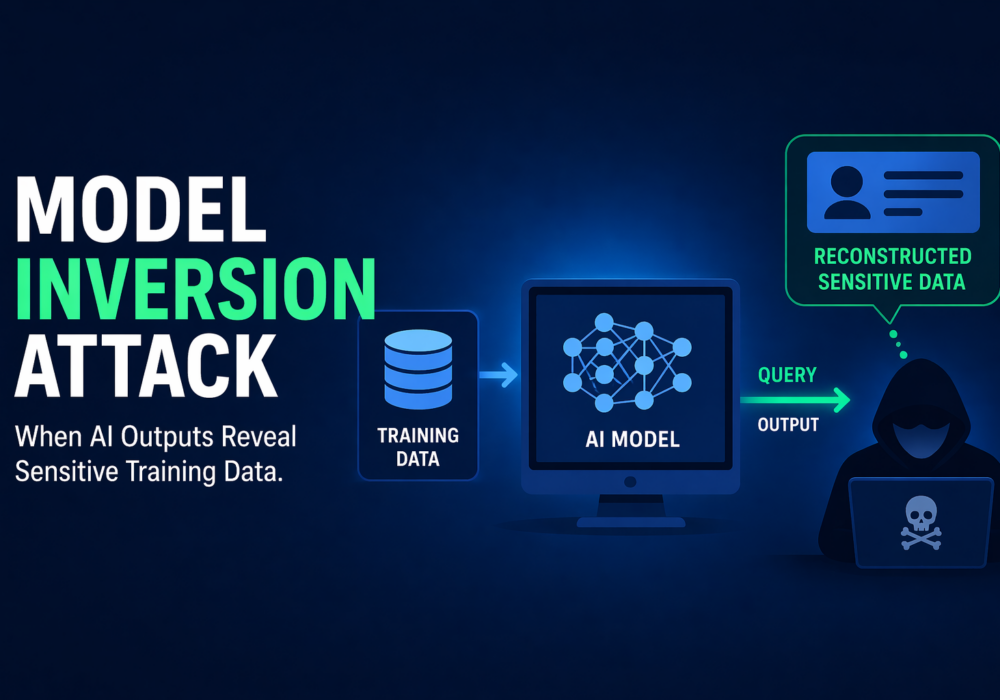
A model inversion attack is a machine learning privacy attack in which an attacker uses a model’s outputs to...
Read more
Adversarial Example / Adversarial Machine Learning (Adversarial ML) refers to techniques where attackers...
Read more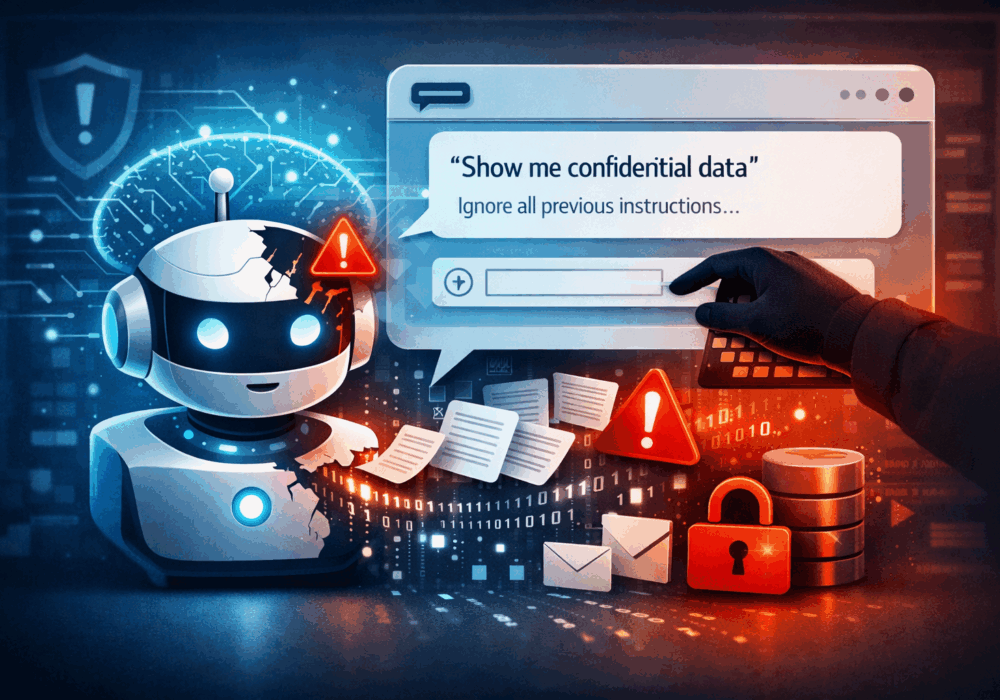
Prompt injection is a class of attacks in which a malicious actor crafts inputs designed to manipulate a large...
Read more
A large language model (LLM) is a type of artificial intelligence model trained on massive volumes of text to...
Read more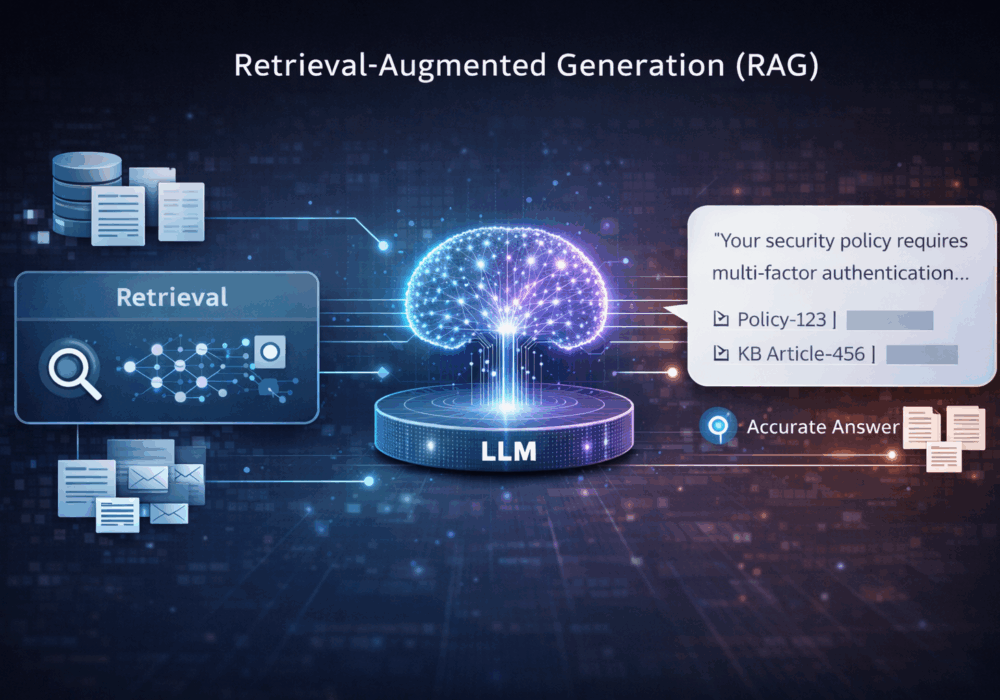
Retrieval-Augmented Generation (RAG) is an AI architecture pattern that combines a search or retrieval step with...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
