"CyberHoot lets us access expert cybersecurity guidance without hiring a full-time specialist."

Who is most likely to fall victim to Cyber Monday phishing scams? People who don't know about phishing scams,...
Read more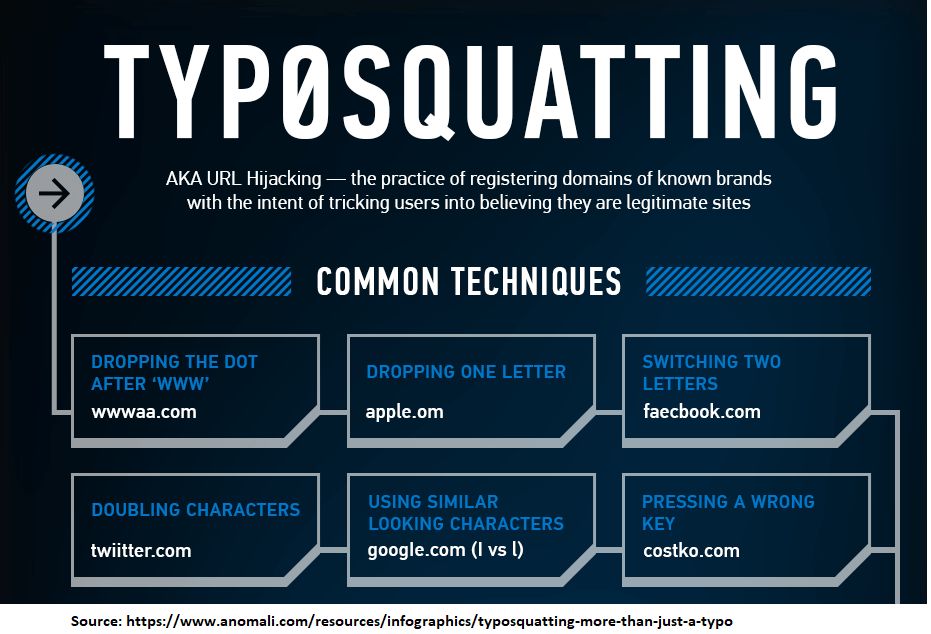
Typosquatting is also called URL hijacking. It is a form of cybersquatting which relies on mistakes such as...
Read more
George Santayana (Sketch artist: Samuel Johnson Woolf) "Those who cannot remember the past are condemned to...
Read more
CyberHoot has learned there is a new Zero-Day vulnerability in Chrome actively being exploited in the Wild. Your...
Read more
The City of Johanessburg (COJ) experienced its second ransomware attack this year. In July a Database, internal...
Read more
October is National CyberSecurity Awareness Month (NCSAM). It is a collaborative effort between government and...
Read more
The FBI issued a stern warning in February 2019. They witnessed multiple Managed Service Providers...
Read more
As part of National Cybersecurity Awareness Month (NCAM), CyberHoot strives to share topics that broaden...
Read more
The picture above is a bag with $25,000 in "redeemed" Apple Store gift cards sent to hackers overseas by a small...
Read more
Employees are the weakest link in Cybersecurity and because of this 80% of businesses will adopt a Cloud-based...
Read more
October is National CyberSecurity Awareness Month (NCSAM). It is a collaborative effort between government and...
Read more
October is National CyberSecurity Awareness Month (NCSAM). It is a collaborative effort between government and...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
