"CyberHoot is an excellent cybersecurity training platform that educates teams on security practices through training content, phishing simulations, and actionable analytics."
Click Image To View Larger Version CyberHoot’s Press Releases are published on a monthly basis. To...
Read more
Since Coronavirus (COVID-19) gained pandemic status in early March 2020, hackers have been attacking...
Read more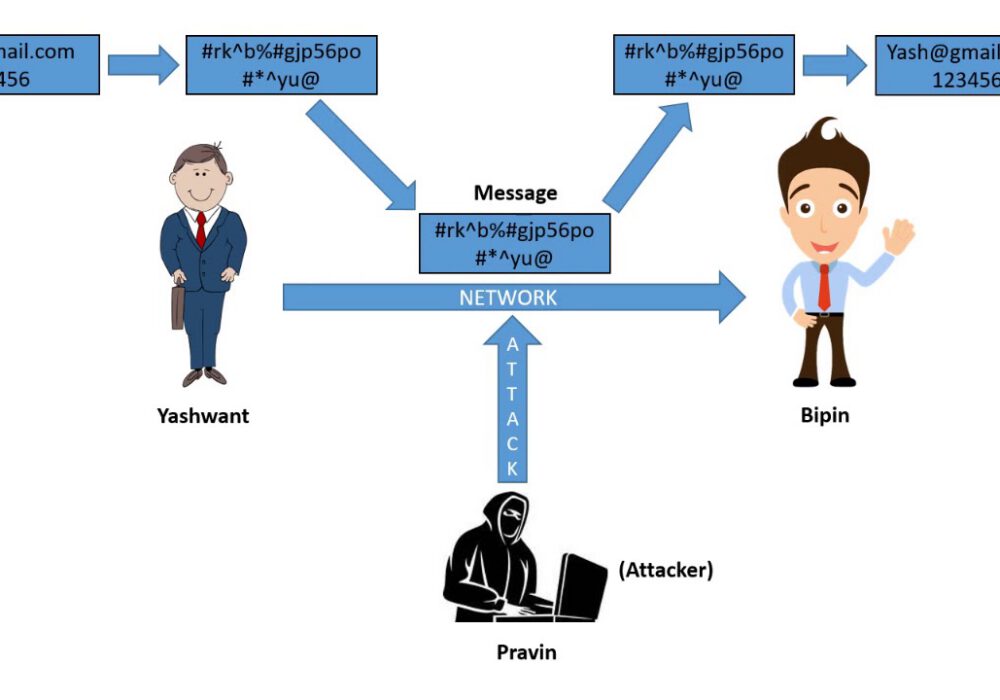
Cryptanalysis is the decryption and analysis of codes, ciphers or encrypted text. Cryptanalysis uses...
Read more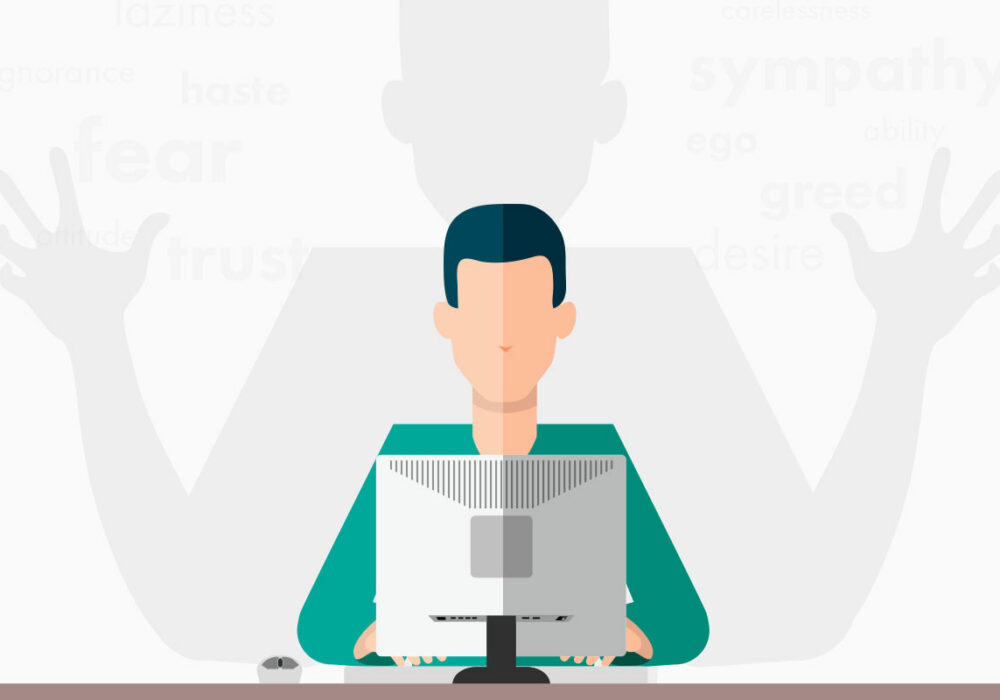
Piggybacking is a form of cyber attack where a hacker(s) gain access to an unauthorized network,...
Read more
The Mac Myth Apple's Mac Operating Systems (OS) is impenetrable to malware. Myth. Recent malware...
Read more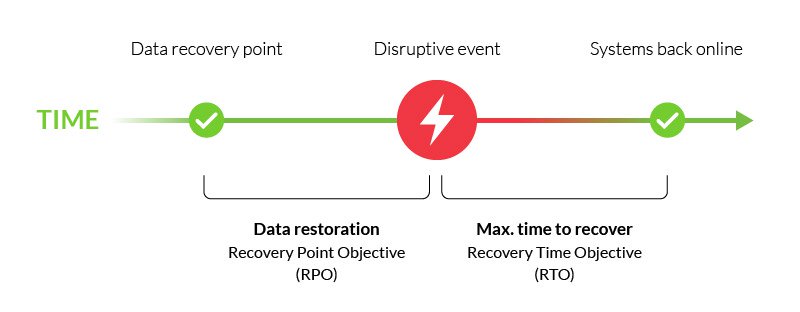
A Recovery Point Objective (RPO) is the maximum amount of data that your company is willing to...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
