“Using CyberHoot was one of the best decisions we made regarding SAT. Fully automated, training is interesting, and staff participation is high compared to other vendors.”

Secure your business with CyberHoot Today!!! Sign Up Now Customers from over 300 restaurants' had...
Read more
CyberHoot Vulnerability Alert Management Process (VAMP) Rating: Critical/Red July 19th, 2022:...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now China has landed in the middle of one of the...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Time-To-Live (TTL) is a value for the period...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Call Admission Control (CAC) is the method...
Read more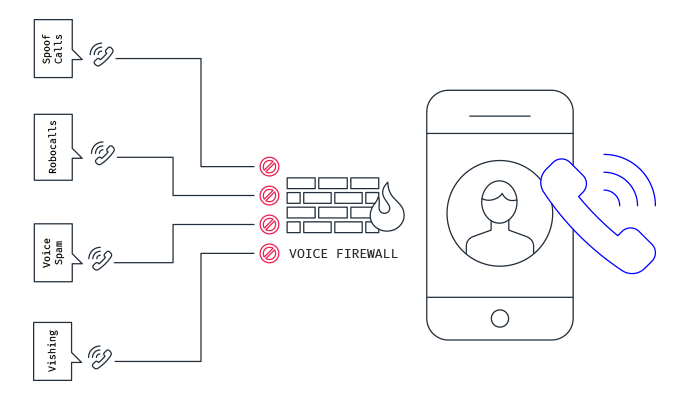
Source: Mobileum Secure your business with CyberHoot Today!!! Sign Up Now A Voice Firewall...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Traceroute is a network diagnostic tool used...
Read more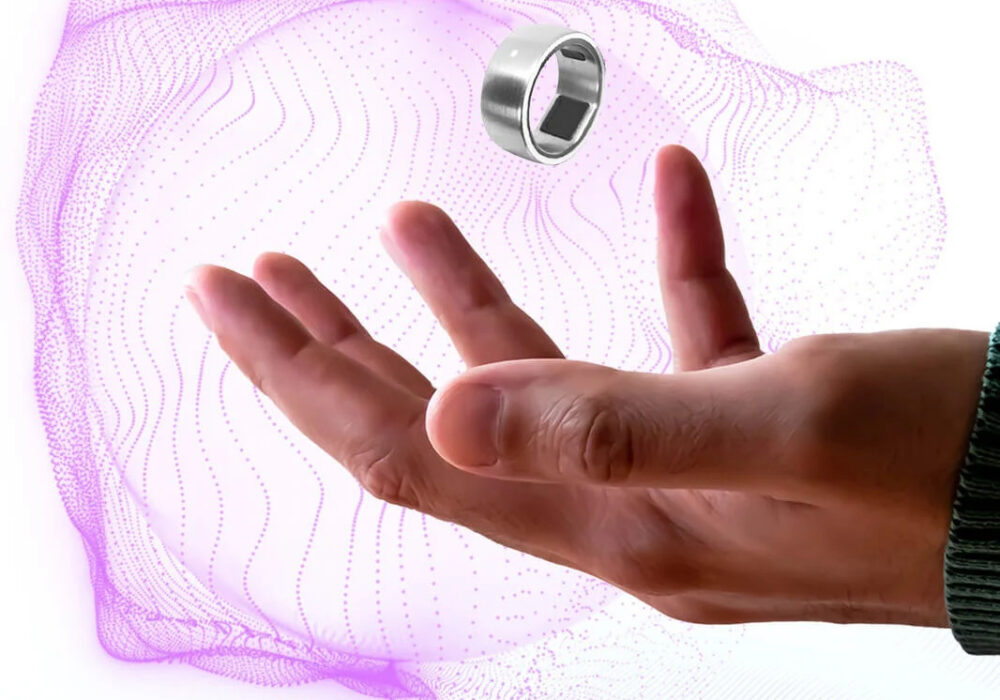
Secure your business with CyberHoot Today!!! Sign Up Now Token Ring the new company (not the old...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now A HoneyMonkey is a system created by...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
