There are a few truisms floating around security professionals’ minds. One is this: give me physical access to your device and I can break into it. Another is this: allow me to run a program on your computer and I can hack you and steal your data. Now, even if these truisms are only true 20%, 40%, or maybe even 50% of the time, is that a chance you want to take? Not really, right!
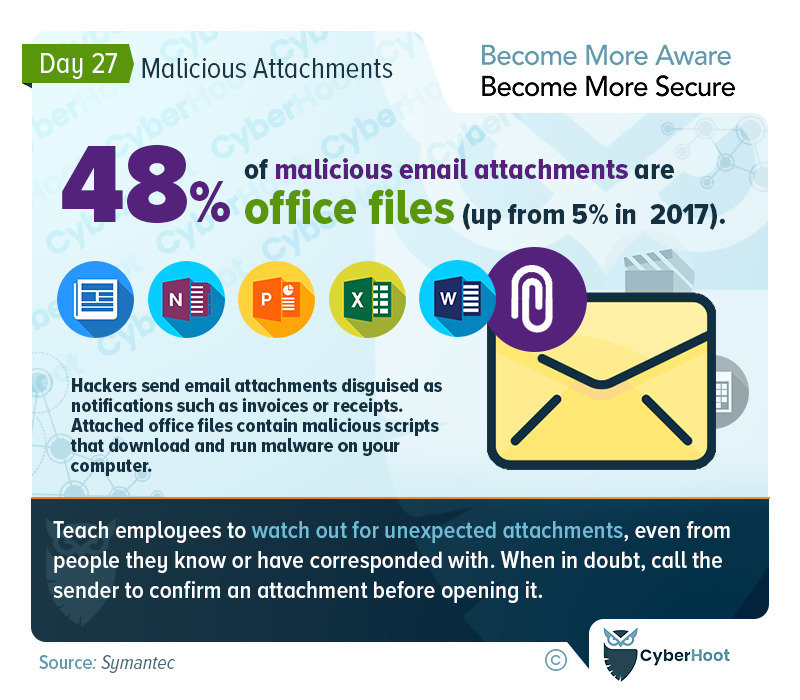
Never leave your device unattended, and never, ever, run something you do not trust on your computer, including and especially, files received as attachments to an email. No matter how likely they were to be sent to you, always check with the sender to confirm they are meant to be sent to you. Oh, and don’t check by emailing back the sender of the file, a hacker may intercept and will always say, “Yes, that file is just for you, Pal!”
Also, are you running your workstation with administrative or root credentials? When and if you make a mistake the consequences are much worse as the file runs with the credentials necessary to install more software, in quiet mode, unattended by nuisance prompts of “are you sure” etc. Operate your computer with a non-privileged account. Yes it is more painful on the rare occasion you need to install a printer driver, but honestly how often is that?
Also consider signing up with CyberHoot to learn about, and implement, the best practices listed below.
CyberHoot believes that for many small to medium sized businesses and MSPs, you can greatly improve your defenses and chances of not becoming another victim of cyberattack if you follow the advice above.
We hope you’re enjoying Cybersecurity Awareness Month (CAM). Visit or subscribe to CyberHoot’s Facebook, LinkedIn, or Twitter pages to get daily updates throughout the month.
Malware Statistics and Facts in 2022
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

A Practical Brief for vCISOs THE WARNING WE IGNORED OR COULD NOT UNDERSTAND For years, the most credible...
Read more
A guide to spotting senior executive impersonation scams before the fake CEO gets a real wire transfer. It...
Read more
Artificial Intelligence (or AI) is making phishing emails smarter, malware sneakier, and credential theft easier...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
