China has landed in the middle of one of the largest data breaches of all time after a government developer wrote a blog post on a popular forum that included the credentials to a Shanghai police database. This isn’t all too surprising, as 82% of breaches last year were in part due to human error. This includes things such as phishing, use of stolen credentials, misconfiguration, and simple mistakes.
Threat actors were able to get their hands on the data and have posted the 23 terabytes of data for sale on the Dark Web. In total, the leak includes the personal information of roughly one billion Chinese citizens.
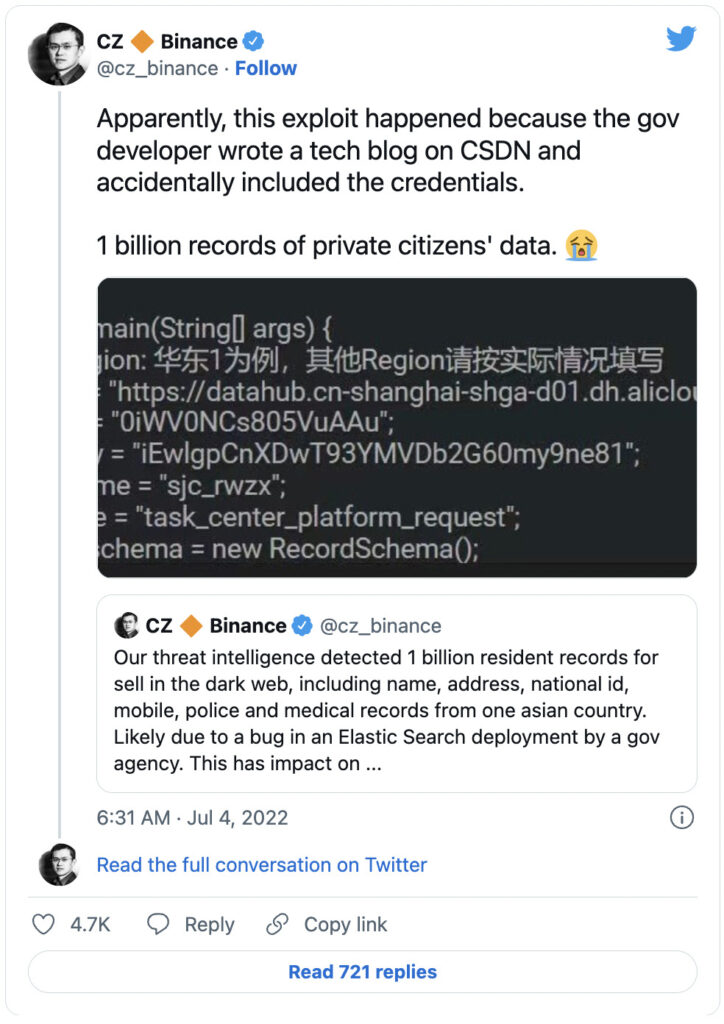
Chinese billionaire and Binance CEO Zhao Changpeng said earlier this week that Binance’s threat intelligence team detected one billion records for sale on the Dark Web. He later shared that a government developer’s blog post on the China Software Development Network (CSDN) accidentally included the credentials to a Shanghai police database:
The information in the data leak includes a significant amount of Non-Public Personal Information (NPII) that could compromise up to a billion Chinese citizens. The data leaked included names, addresses, birthplaces, national IDs, phone numbers, health records, and criminal records of Chinese citizens. This is yet another example of why companies must get serious about cybersecurity training with their employees.
The data was posted to Breach Forums, a popular site for hackers to buy and sell information. The personal data was posted by an anonymous hacker by the name of ‘ChinaDan’, according to Threatpost. In the post, ‘ChinaDan’ claimed to have downloaded the data from a cloud storage server hosted by Alibaba. The hacker was asking for 10 Bitcoin, which comes out to roughly $200,000, for the entire set of data.
Craig Lurey, CTO, and co-founder of Keeper Security spoke with shared his reaction to the data leak:
“This is the end result of a catastrophic failure to implement basic password management and secrets management. Secrets such as database credentials should never be hard-coded into source code, which is what caused the breach.”
It’s important to note that many password managers allow organizations to establish strict, deliberate role-based access control (RBAC), along with privileged access to infrastructure, to protect sensitive data and secrets.
This data leak shows that even government employees with security clearances can make mistakes that have catastrophic results. Obviously, someone with that level of clearance has access to databases like these, whereas the average employee at an average company only has access to their company and customer information. This doesn’t mean that the average employee doesn’t pose a risk, it means that anyone can make mistakes and put your company at risk. It’s important to ensure that your staff is being educated on proper password hygiene, how to handle critical information and other aspects of their workday that could put company or customer data at risk.
Continue reading to learn more about the minimum essential cybersecurity measures all companies must build into their cybersecurity programs.
The following recommendations will help you and your business stay secure with the various threats you may face on a day-to-day basis. All of the suggestions listed below can be gained by hiring CyberHoot’s vCISO Program development services.
Each of these recommendations, except cyber-insurance, is built into CyberHoot’s product and virtual Chief Information Security Officer services. With CyberHoot you can govern, train, assess, and test your employees. Visit CyberHoot.com and sign up for our services today. At the very least continue to learn by enrolling in our monthly Cybersecurity newsletters to stay on top of current cybersecurity updates.
Source:
Additional Readings:
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

DocuSign has become one of the most trusted tools in modern business. Contracts, HR paperwork, NDAs, vendor...
Read more
And yes, Google's Gemini AI had no idea it was working for the bad guys. Malware has always followed a script....
Read more
Ransomware groups are not breaking in organizations the same way they did five years ago. The entry methods have...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
