"CyberHoot's cyber awareness training is a game-changer for businesses looking to build a strong security culture."
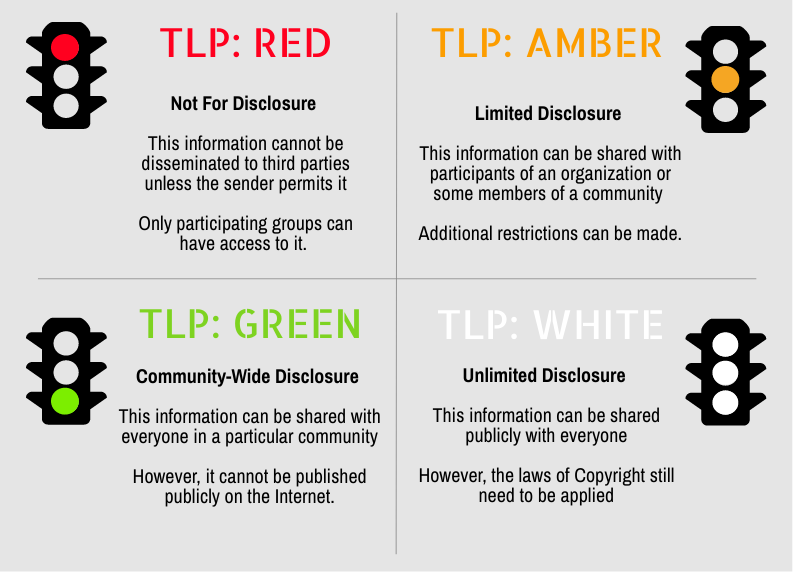
Secure your business with CyberHoot Today!!! Sign Up Now Traffic Light Protocol (TLP) is a set of...
Read more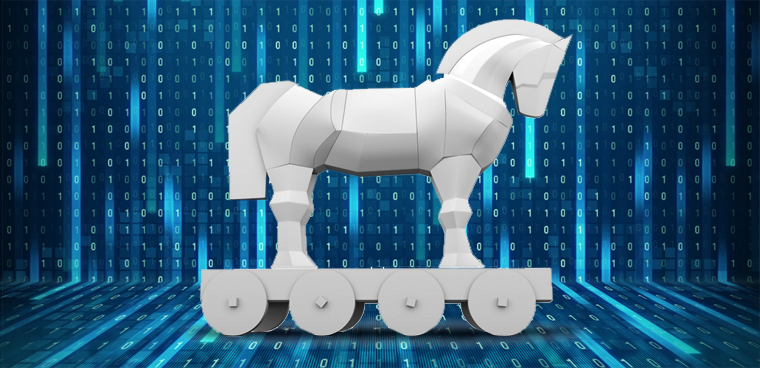
A Trojan Horse is a computer program that appears to have a useful function, but also has a hidden and...
Read more
All credit and debit cards are now being made with "a computer that is 1/4 the size of a postage stamp" this...
Read more
Image Source A vulnerability is a characteristic or specific weakness that renders an organization...
Read more
An Allow list, also known as a Permit List or (deprecated: White List), is a list of...
Read more
Image Source A Work Factor is an estimate of the effort or time needed by a potential adversary, with...
Read more
PCI DSS stands for Payment Card Industry Data Security Standard. This is the standard that all organizations must...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
