"While it is well known that there are many cyber security threats, sorting out how to protect yourself without accidentally exposing yourself can be a daunting task. For a small organization like ours, this type expertise and time to research..."
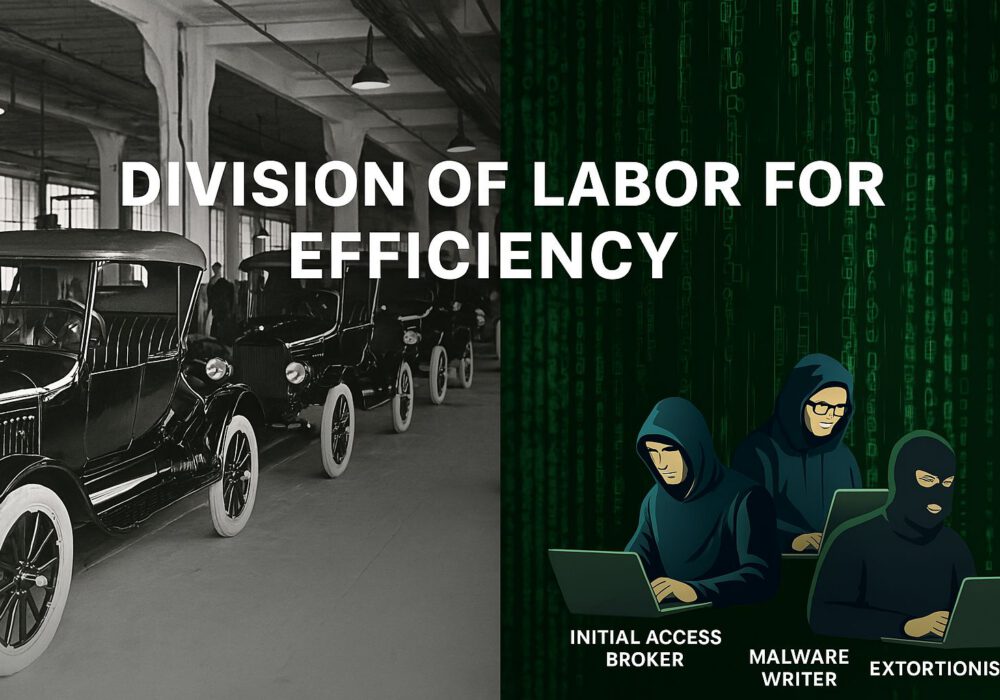
Henry Ford revolutionized automobile manufacturing a century ago by dividing complex assembly tasks into...
Read more
As the April 15 U.S. Tax Day approaches, cybercriminals are intensifying their efforts to...
Read more
In 2025, hackers continue to exploit office files, making them a top attack vector for cybercrime....
Read more
As ransomware threats go, the Medusa ransomware group has a lengthy and notorious history of successfully...
Read more
But please don't panic. This was only a test. Before landing here, you clicked on a phishing email sent by...
Read more
In a recent revelation, cybersecurity researchers from sqrx.com have uncovered a sophisticated attack method...
Read more
Dark Web Hacking Groups Mirror Real-World SaaS Companies In today's hyper connected world, the distinction...
Read more
This video was created specifically for MSPs with Super Admin access to CyberHoot's Power Platform and its...
Read more
The Entra ID sync is not functioning because the provided client secret has expired. To resolve this, you will...
Read more
Overview A Checkpoint security researcher has discovered a critical vulnerability in Microsoft Outlook that poses...
Read more
In today’s ever evolving cyber threat landscape, attackers are finding innovative ways to bypass traditional...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
