"After 9 months of CyberHoot awareness training, a Financial Management firm with $4 Billion in assets was phish tested by the Fellsway Group. They had zero (0%) employees click on the phishing test. In contrast, the exact same phishing attack..."
Monthly Recurring Revenue (MRR) is the most important topic for Managed Service Providers (MSPs). MRR...
Read more
Cybersecurity threats are evolving everyday, requiring businesses to update their security postures...
Read more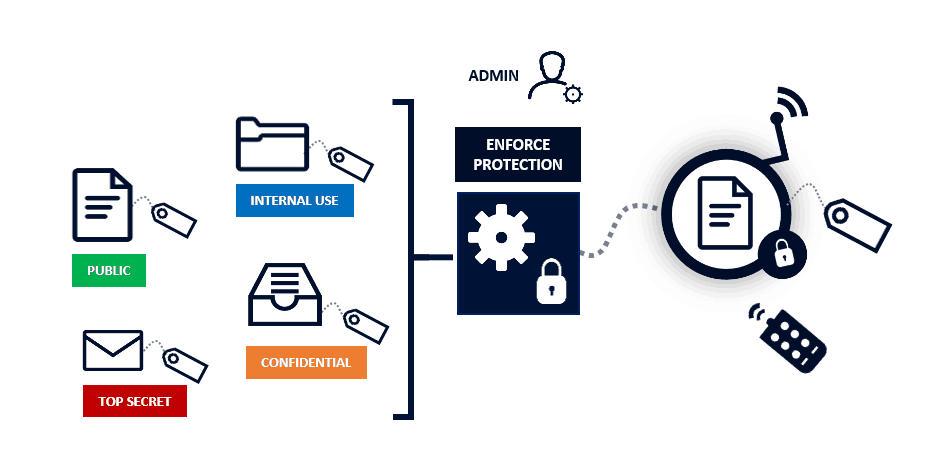
Data Classification is about categorizing data into buckets to make it easier to retrieve,...
Read more
Dear Valued Customer, As Eric shared last week, our commitment to strengthening and improving Zoom is our...
Read more
Contact Tracing is a medical term which describes a process used to identify, trace, and contact people...
Read more
In 2020, the number of daily smartphone users in the world totals 3.5 Billion or 45% of the...
Read more
With the issues we are facing today with the coronavirus, many technology companies are looking for...
Read more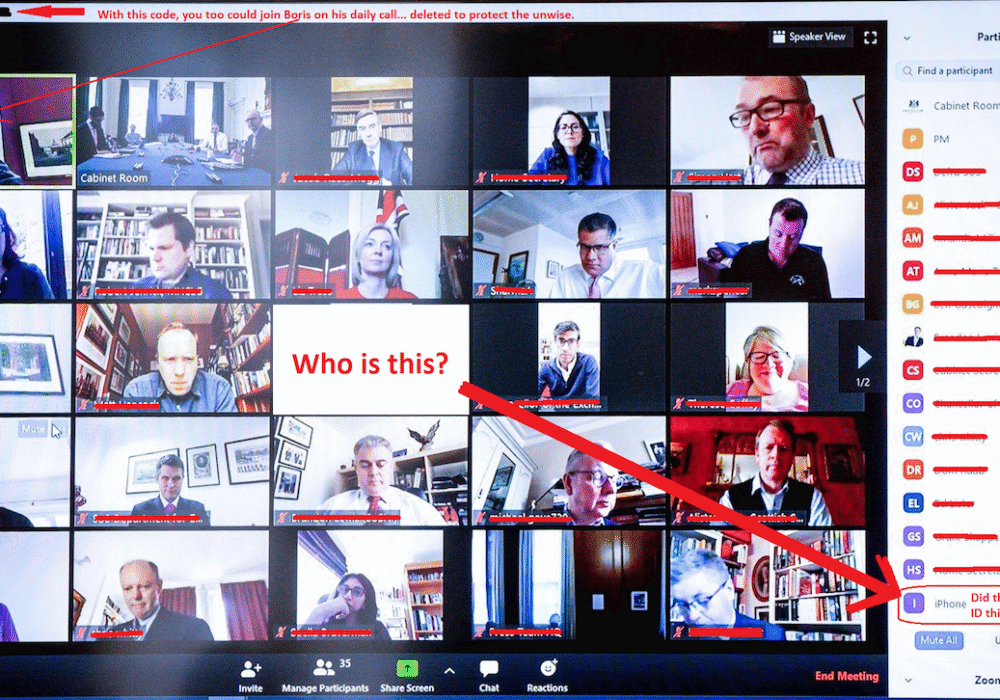
Zoom Bombing is where an unauthorized person enters your Zoom video conference to cause disruptions or to gain...
Read more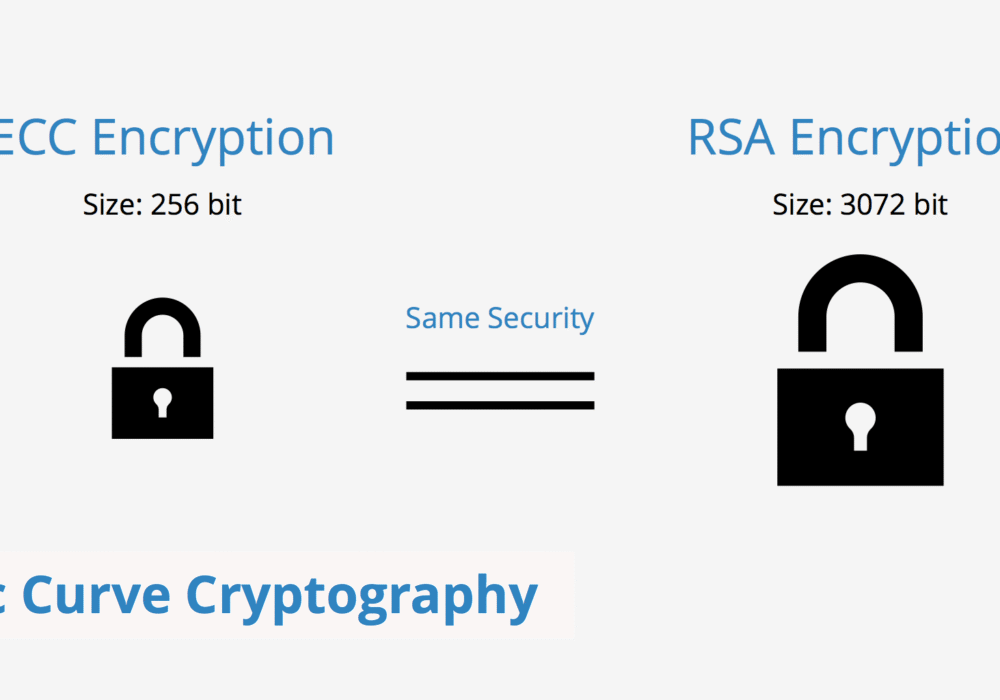
Elliptic Curve Cryptography (ECC) is a public key encryption method that is based on elliptic curve...
Read more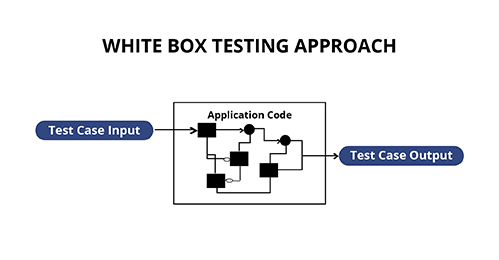
White Box Testing is a form of penetration testing which tests internal structures of an...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
