"Cybersecurity training is complicated, partnering with CyberHoot keeps it simple. Our users are engaged with little administrative overhead."
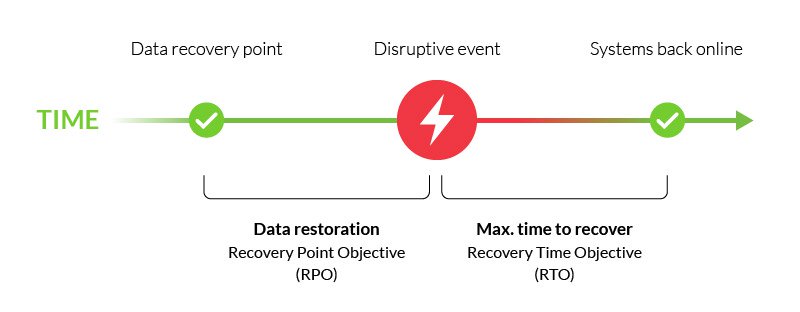
A Recovery Point Objective (RPO) is the maximum amount of data that your company is willing to...
Read more
A Recovery Time Objective (RTO) is a metric used to measure how fast you can recover your IT...
Read more
The term Restore, also known as Recovery, is the process of retrieving production data from a backup...
Read more
During the coronavirus pandemic, Contact Tracing is being used to slow the spread of the virus. Contact...
Read more
Eavesdropping in the cybersecurity world refers to the interception of communication between two...
Read more
A POS Intrusion is an attack that happens at the Point-of-Sale device. The POS device in retail stores...
Read more
Cyber Espionage is a cyber attack that leads to stolen classified, sensitive, or critical data often in...
Read more
Data Mining refers to the mathematical techniques used to exam large data sets including but not limited to...
Read more
A Cybersecurity Ecosystem is just like natural ecosystems. It is made up of a variety of...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
