"Craig and the CyberHoot team are great business partners! They are always open to enhancing their product, and ready to help my team with any deployment questions they may have. I am also an end user of the CyberHoot security..."

March 22nd, 2022: CyberHoot is investigating a potential breach at Okta, developers of a cloud-based...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Co-Authored by Craig Taylor, CEO...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Endpoint Detection and Response (EDR), also...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now The Health Insurance Portability and...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Controlled Unclassified Information (CUI) is...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Korean security analysts have spotted a...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now The Cybersecurity Maturity Model...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now A Purple Team is a group of cybersecurity...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Network Access Control (NAC) is the act of...
Read more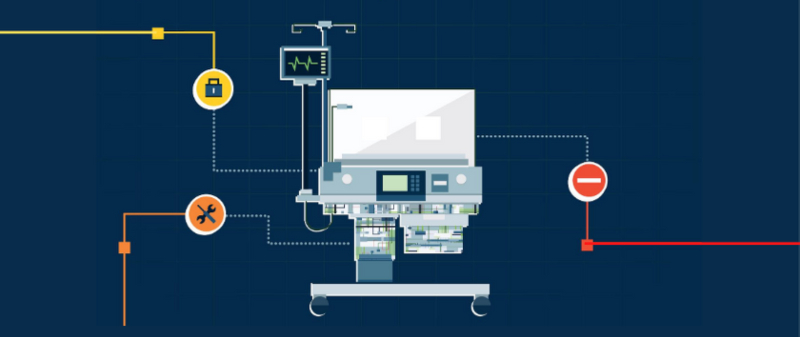
Secure your business with CyberHoot Today!!! Sign Up Now An analysis of data from more than 200,000...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now AES Encryption, also known as Advanced...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Wiper Malware is malicious software that...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
