"While it is well known that there are many cyber security threats, sorting out how to protect yourself without accidentally exposing yourself can be a daunting task. For a small organization like ours, this type expertise and time to research..."
Secure your business with CyberHoot Today!!! Sign Up Now Assembly Language is the most basic...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now In late April 2022, Google announced they've...
Read more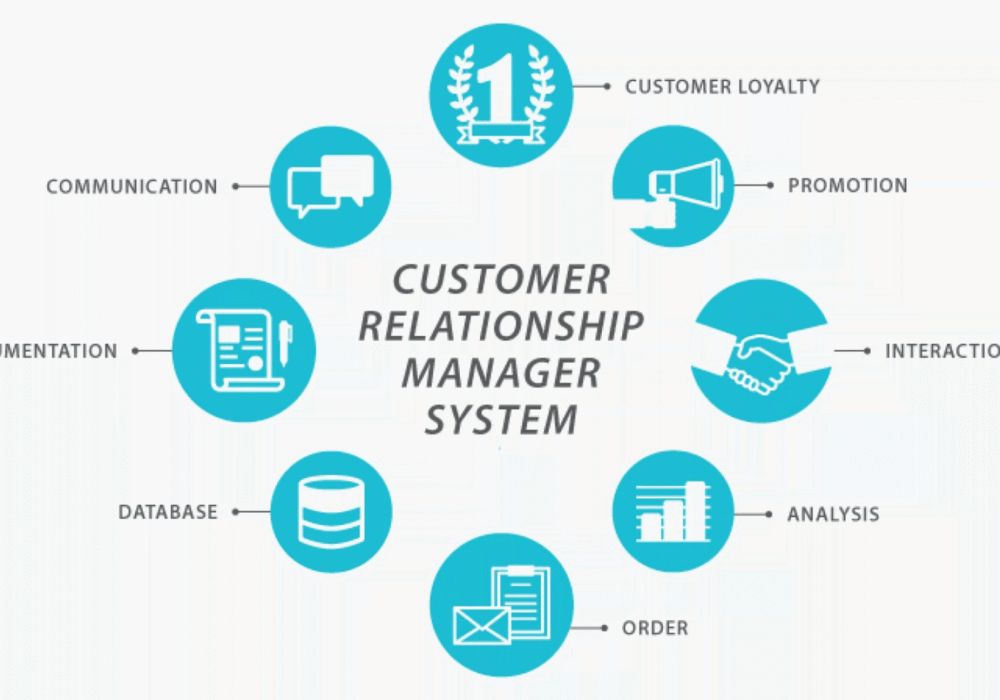
Secure your business with CyberHoot Today!!! Sign Up Now Customer Relationship Management (CRM) is a...
Read more
April 22nd, 2022: CyberHoot has investigated a Java Product vulnerability tracked as CVE-2022-21449 that...
Read more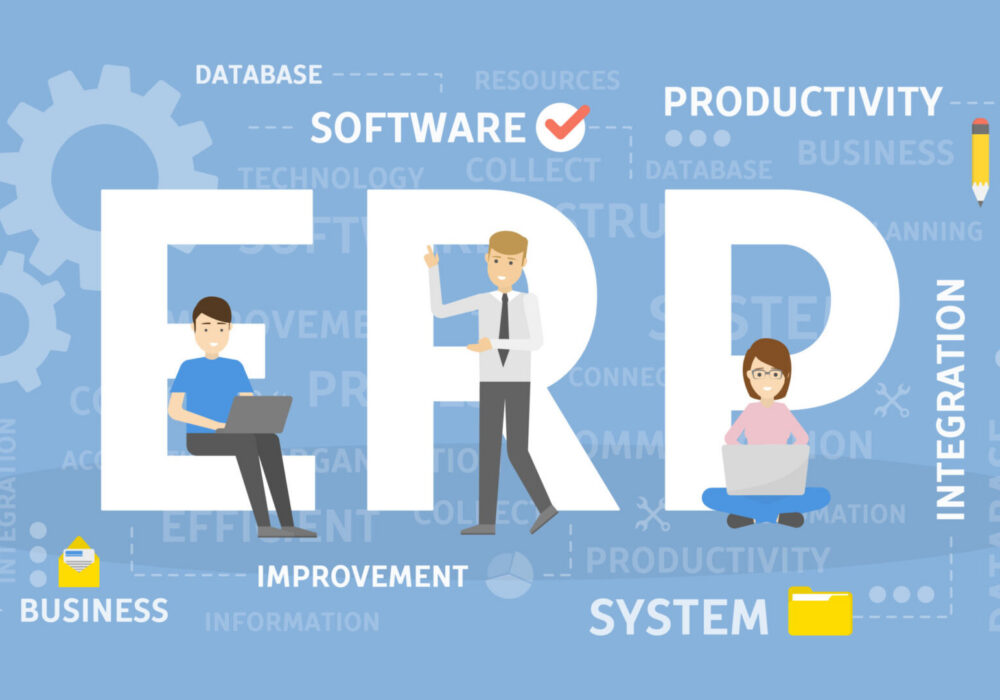
Secure your business with CyberHoot Today!!! Sign Up Now Enterprise Resource Planning (ERP) is a...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Cybersecurity remains a top concern for businesses...
Read more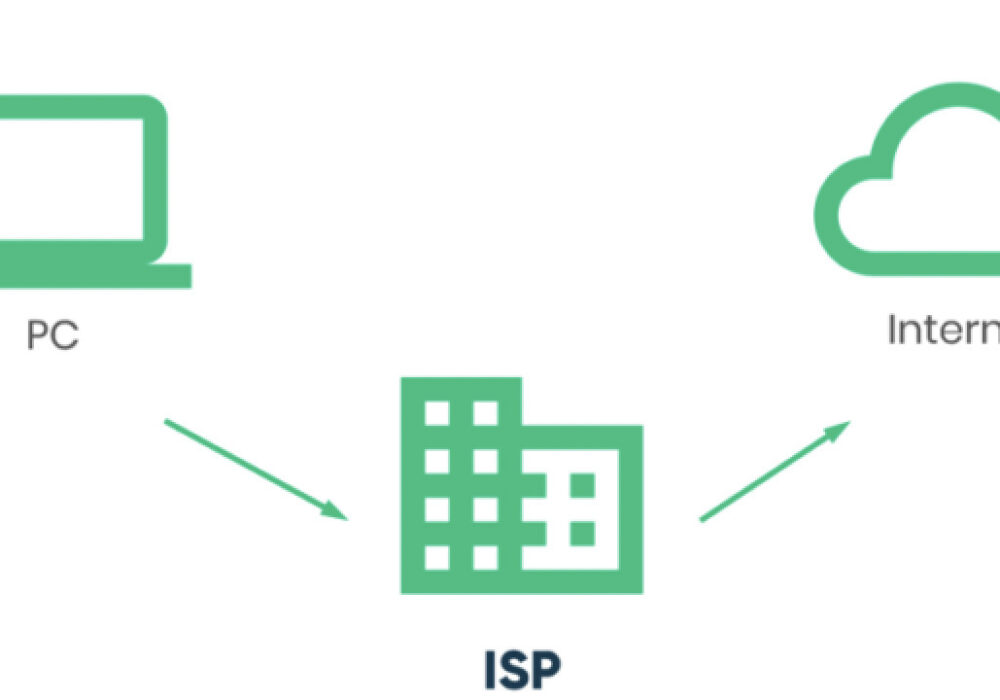
Secure your business with CyberHoot Today!!! Sign Up Now An Internet...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now An Emergency Data Request (EDR) is a...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
