"Cybersecurity training is complicated, partnering with CyberHoot keeps it simple. Our users are engaged with little administrative overhead."
CyberHoot Vulnerability Alert Management Process Rating (VAMP): Critical/Red May 25th, 2022:...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now According to a joint advisory from the U.S....
Read more
CyberHoot Vulnerability Alert Management Process Rating (VAMP): Critical/Red May 19th, 2022:...
Read more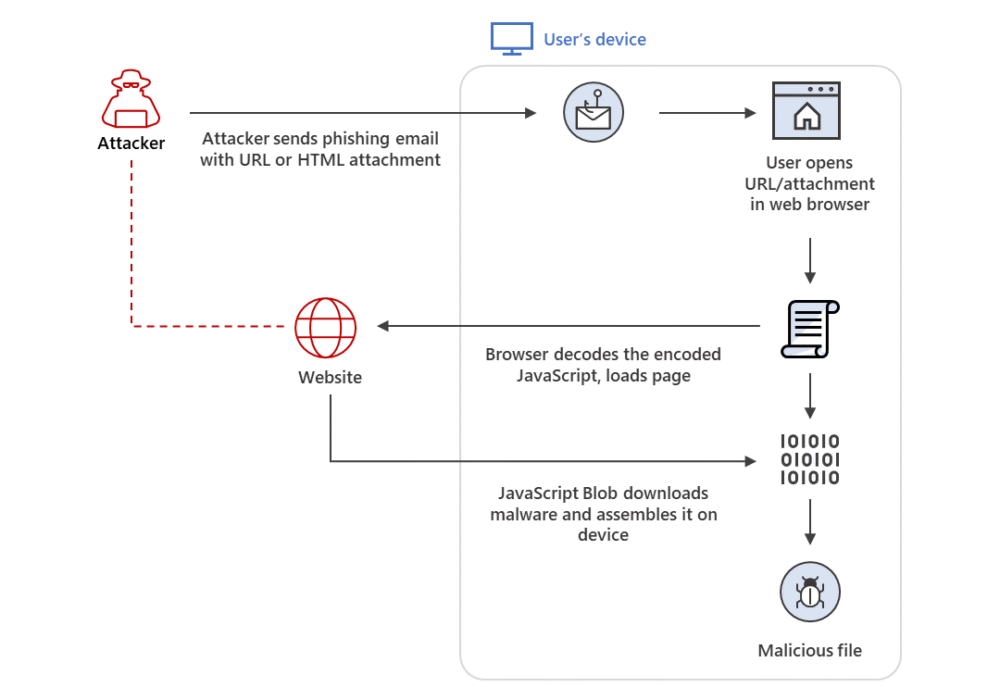
Secure your business with CyberHoot Today!!! Sign Up Now HTML Smuggling is an evasive malware...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now The HP Wolf Security threat research team...
Read more
May 16th, 2022: CyberHoot has investigated a SonicWall advisory warning of a trio of security flaws in...
Read more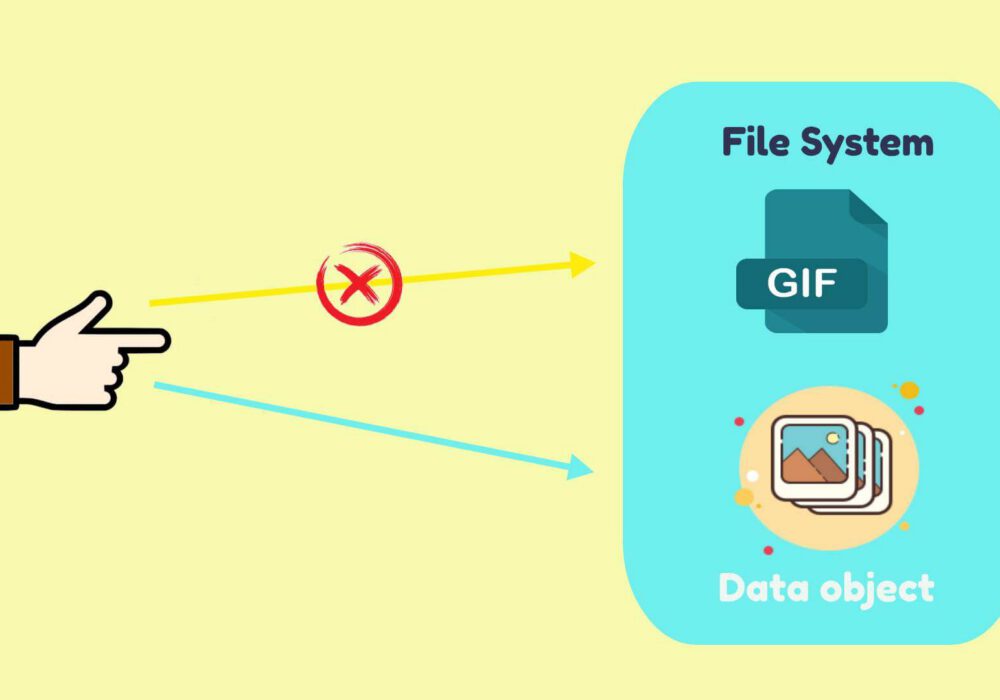
Secure your business with CyberHoot Today!!! Sign Up Now An Object Identifier (OID) is a specific,...
Read more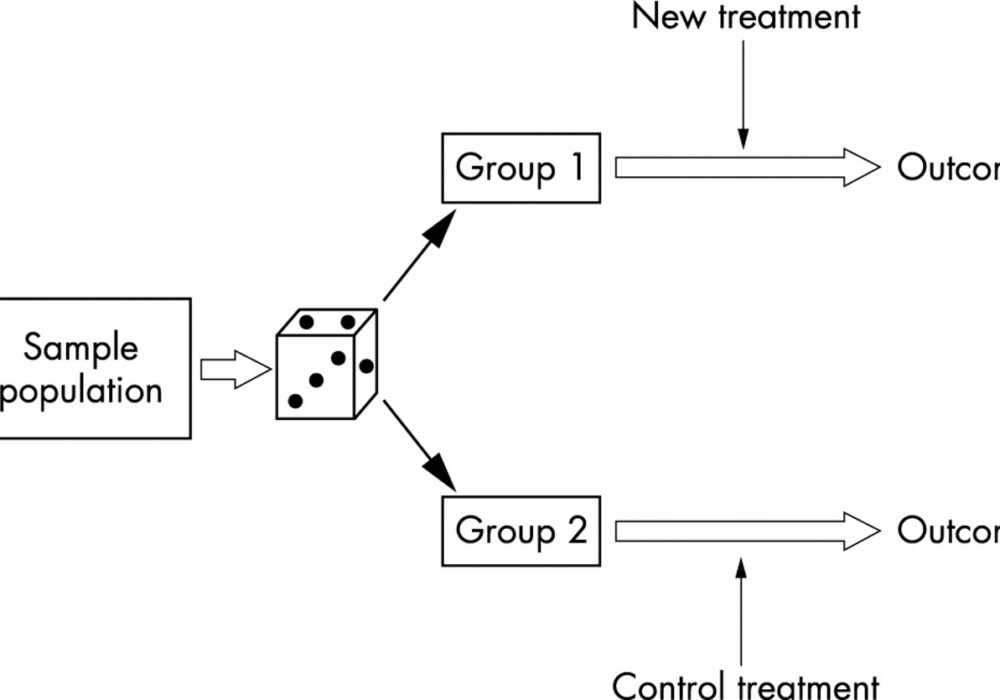
Secure your business with CyberHoot Today!!! Sign Up Now A Randomization Function is an algorithm or...
Read more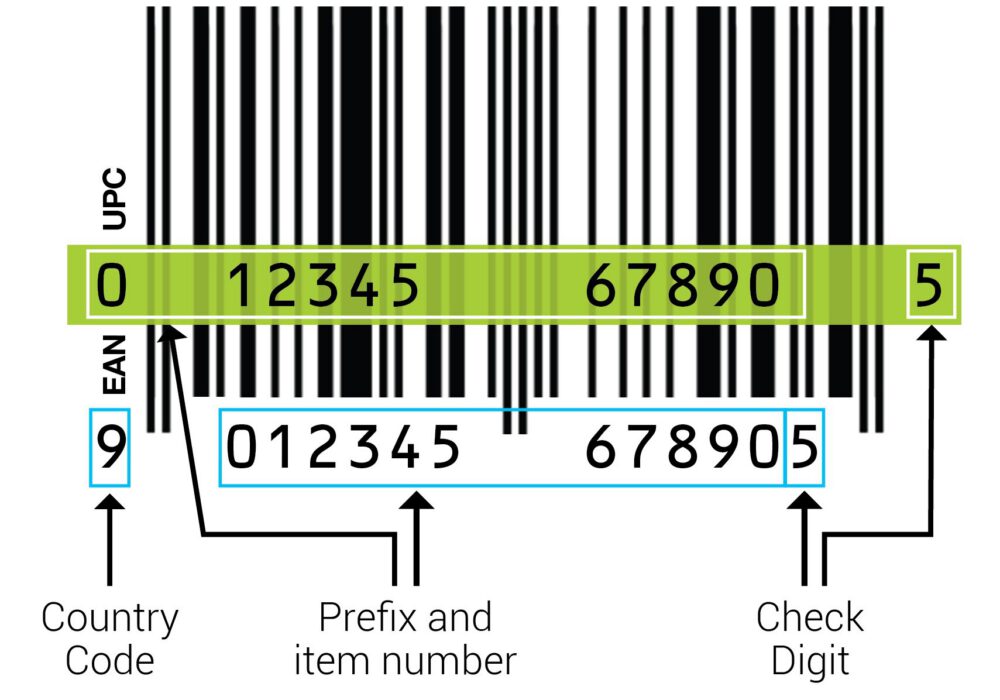
Secure your business with CyberHoot Today!!! Sign Up Now A Check Digit is a digit added to a string...
Read more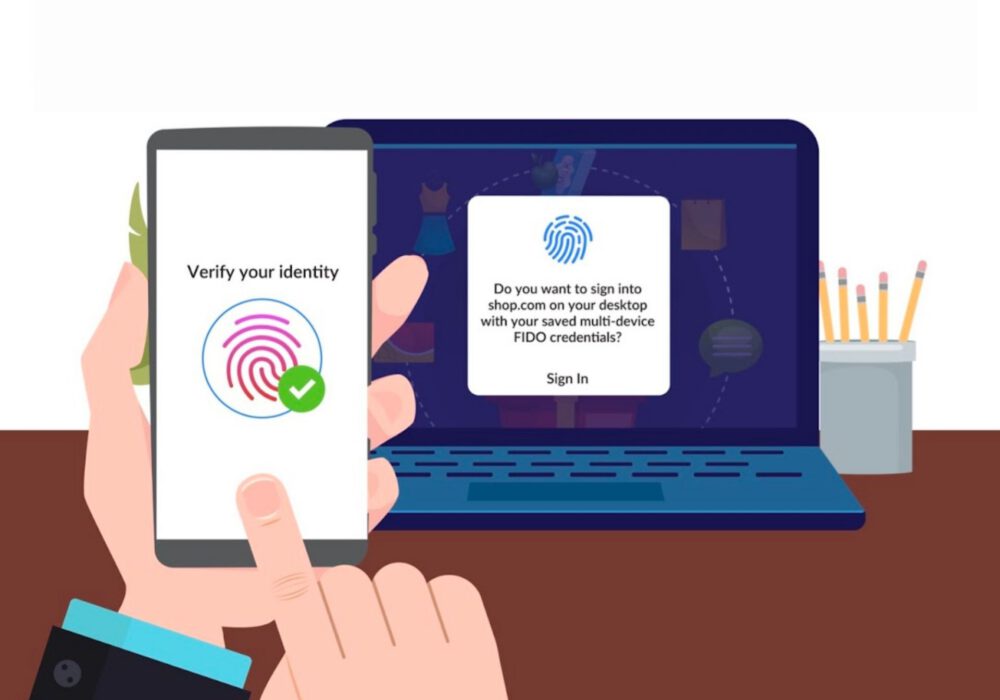
Secure your business with CyberHoot Today!!! Sign Up Now In early May 2022, Google, Apple, and...
Read more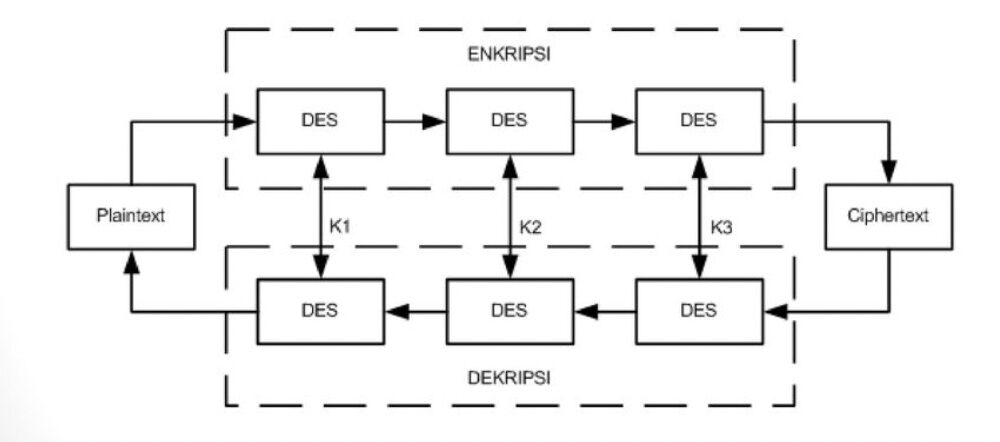
Secure your business with CyberHoot Today!!! Sign Up Now 3DES Encryption, also known as Triple Data...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
