May 16th, 2022: CyberHoot has investigated a SonicWall advisory warning of a trio of security flaws in its Secure Mobile Access (SMA) 1000 appliances, including a high-severity authentication bypass vulnerability. Tom Wyatt of the Mimecast Offensive Security Team has been credited with discovering and reporting the vulnerabilities.
This follows three other critical zero-day vulnerabilities in SonicWalls email security solution (detailed here) discovered by Mandiant, a cybersecurity forensics and consulting firm.
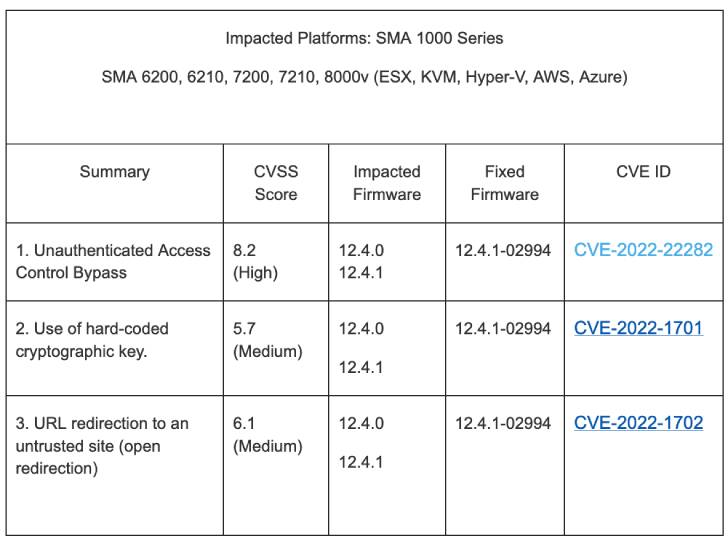
The weaknesses in question impact SMA 6200, 6210, 7200, 7210, and 8000v running firmware versions 12.4.0 and 12.4.1. The vulnerabilities are listed below:
Successful exploitation of these bugs could allow an attacker to unauthorized access to internal resources and even redirect potential victims to malicious websites.
SonicWall noted that the flaws do not affect SMA 1000 series running versions earlier than 12.4.0, SMA 100 series, Central Management Servers (CMS), and remote access clients.
Although there is no evidence that these vulnerabilities are being exploited in the wild yet, it’s recommended that users apply the patches as soon as possible in light of the fact that SonicWall appliances have presented an attractive bullseye in the past for ransomware attacks.
If you’re a subscriber to CyberHoot’s services, you’ll have access to our Policy and Process library which contains the vulnerability alert management process document. This document prescribes how to respond to situations like this and in what time frame. If your company has not yet adopted a VAMP-like process, now is a great time to get started.
Our recommendations below will help your business’ overall security posture, consider taking these actions as well.
The following recommendations will help you and your business stay secure with the various threats you may face on a day-to-day basis. All of the suggestions listed below can be gained by hiring CyberHoot’s vCISO Program development services.
Each of these recommendations, except cyber-insurance, is built into CyberHoot’s product and virtual Chief Information Security Officer services. With CyberHoot you can govern, train, assess, and test your employees. Visit CyberHoot.com and sign up for our services today. At the very least continue to learn by enrolling in our monthly Cybersecurity newsletters to stay on top of current cybersecurity updates.
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

As smart homes get smarter, so do their habits of watching, sensing, and reporting. Enter WiFi Motion Detection, a...
Read more
Spoiler alert: If you’re still using “password123” or “iloveyou” for your login… it’s time for an...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
