"Craig and the CyberHoot team are great business partners! They are always open to enhancing their product, and ready to help my team with any deployment questions they may have. I am also an end user of the CyberHoot security..."
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.
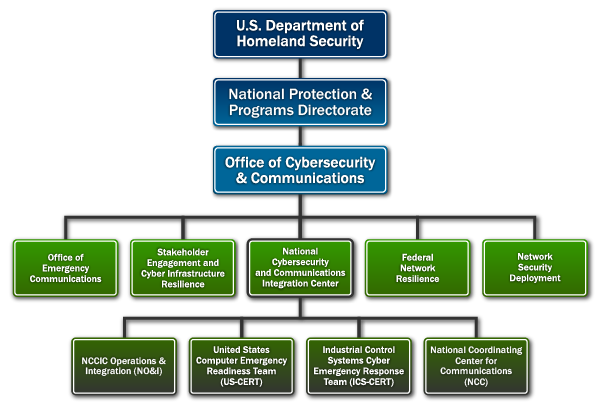
A Computer Emergency Response Team (CERT) is a group of security experts who respond to cybersecurity...
Read more
Root Cause Analysis (or RCA) is a vital tool for all businesses to use when evaluating...
Read more
A Business Continuity and Disaster Recovery (BCDR) Plan is a set of techniques and processes...
Read more
Containment refers to the limiting and preventing of further damage to a computer system or...
Read more
Security Event and Incident Management (SEIM) refers to cyber security products and services...
Read more
An Incident Response Plan is a set of predetermined and documented procedures to detect and respond to a...
Read more
Image Source Incident Response is the activities that address the short-term, direct effects of an incident...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
