"Managed Service Providers (MSP's) are constantly bombarded with new vendors and products that either overlap with a product already in our line cards or is difficult to get client buy in. Cyberhoot brings a new product/service to the MSP space..."
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.
Secure your business with CyberHoot Today!!! Sign Up Now Co-Authored by Craig Taylor In an...
Read more
Containment refers to the limiting and preventing of further damage to a computer system or...
Read more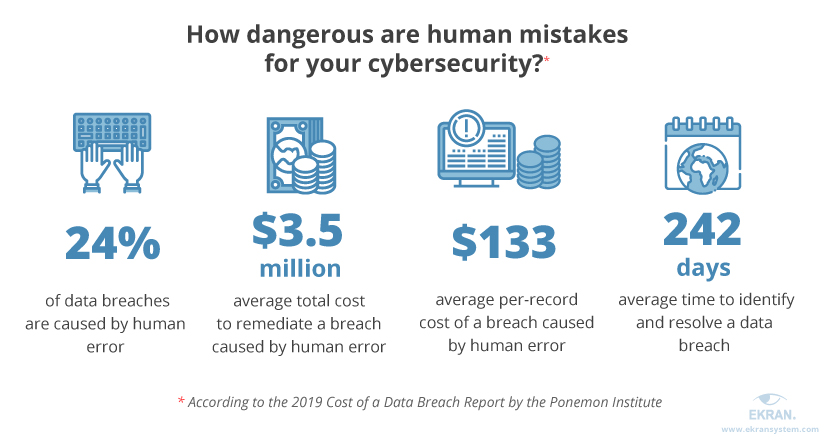
An Accidental Insider Threat occurs when an employees' actions lead to damage to a system or network,...
Read more
Security Event and Incident Management (SEIM) refers to cyber security products and services...
Read more
Phases of an Incident Incident Management is the management and coordination of activities associated with...
Read more
An Incident Response Plan is a set of predetermined and documented procedures to detect and respond to a...
Read more
Image Source Incident Response is the activities that address the short-term, direct effects of an incident...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
