"CyberHoot is an excellent cybersecurity training platform that educates teams on security practices through training content, phishing simulations, and actionable analytics."
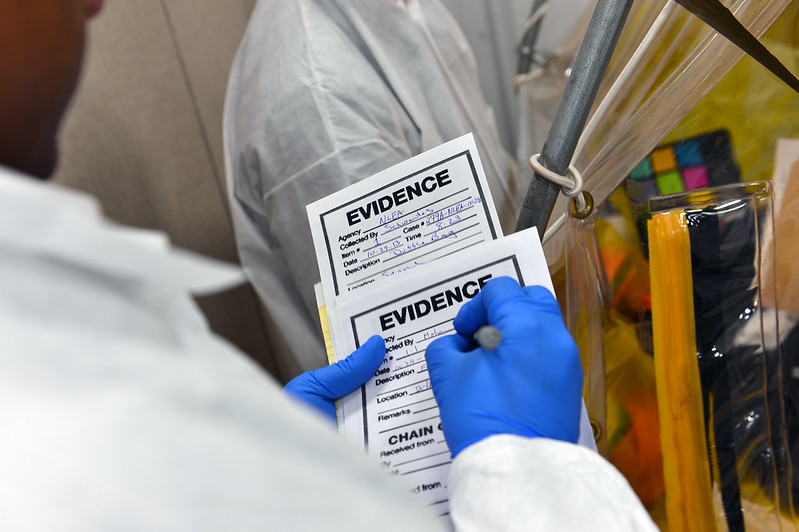
Image Source Digital Forensics is the processes and specialized techniques for gathering, retaining, and...
Read more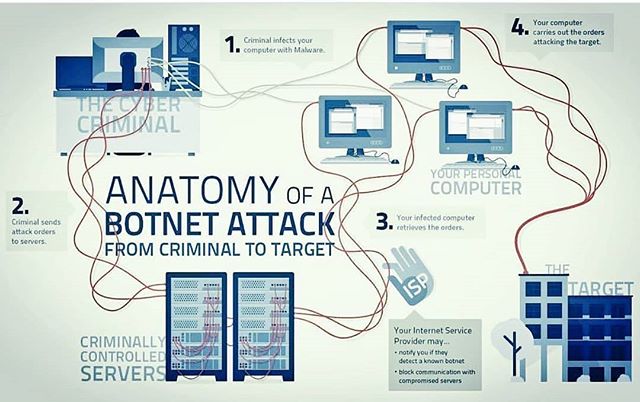
Bot(s) A Bot is a computer connected to the Internet that has been surreptitiously / secretly...
Read more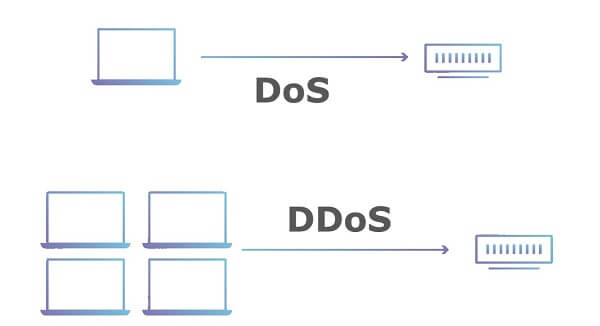
Denial of Service (DoS) is an attack that prevents or impairs the authorized use of information...
Read more
Image Source A Data Breach is the unauthorized movement or disclosure of sensitive information to a party,...
Read more
Image Source Cybersecurity is the activity or process, ability or capability, or state whereby information...
Read more
Image Source Authenticity is a property achieved through cryptographic methods of being genuine and being...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Malicious Code is harmful computer code or...
Read more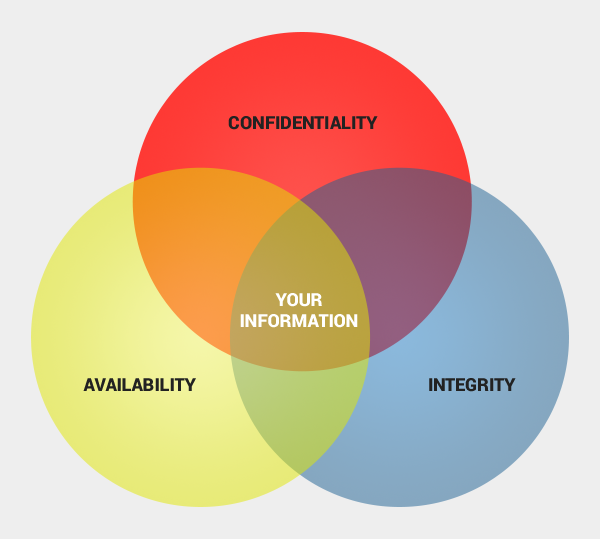
Availability is the property of being accessible and usable upon demand, where in cyber security...
Read more
Confidentiality is one of three critical data protections in cybersecurity. The other two are Integrity...
Read more
Combining public and private keys to electronically sign messages. A Digital Signature is a value computed...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
