"CyberHoot's cyber awareness training is a game-changer for businesses looking to build a strong security culture."
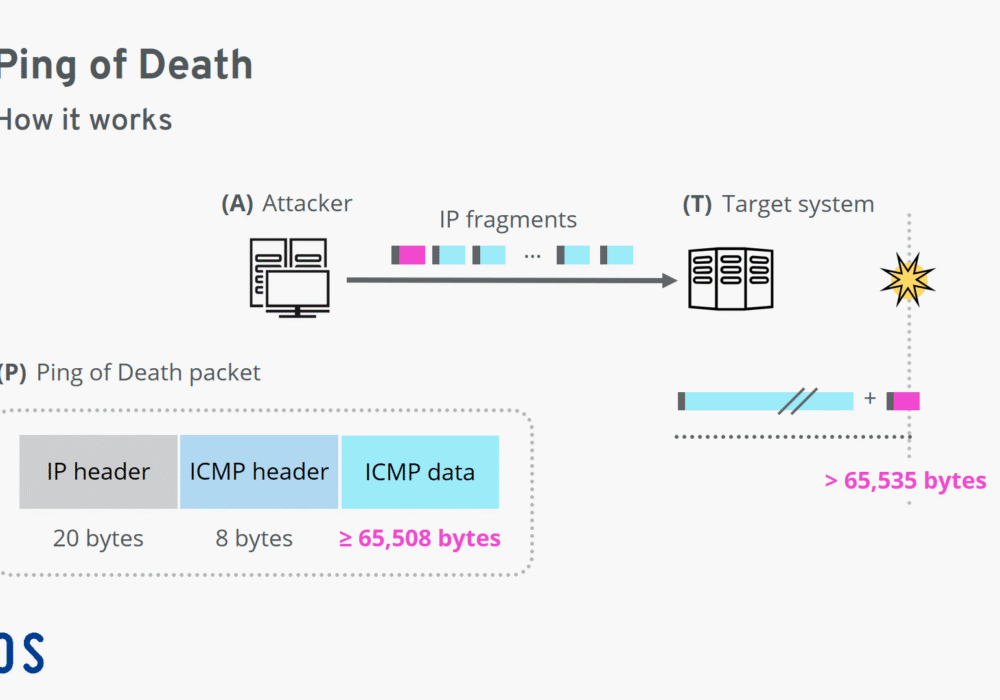
A Ping of Death (PoD) is a type of Denial of Service (DoS) attack that deliberately sends IP packets...
Read more
Common Vulnerabilities and Exposures (CVE) is a list of computer security flaws ranked on critical...
Read more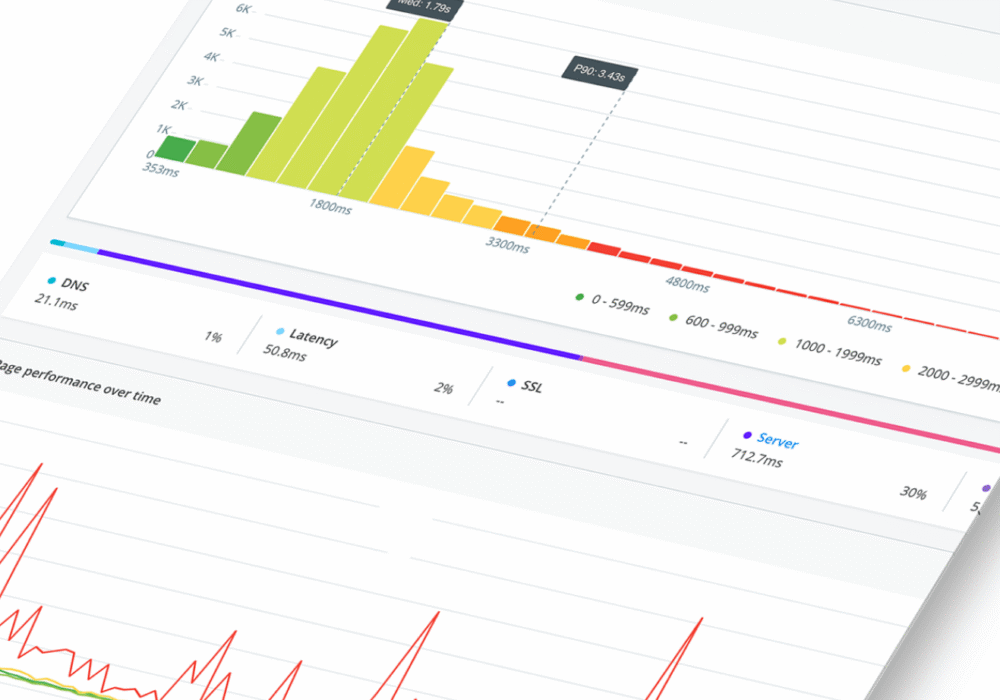
Real User Monitoring (RUM) is a form of performance monitoring that captures and analyzes user activity...
Read more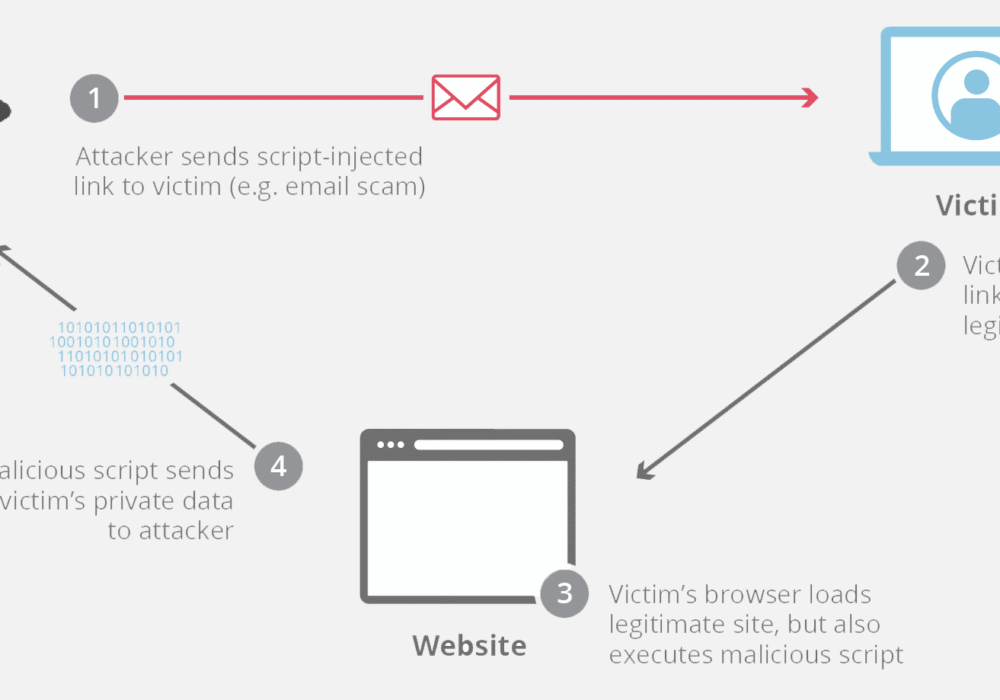
Cross-Site Scripting (XSS) is an attack vector where hackers inject malicious code into a vulnerable...
Read more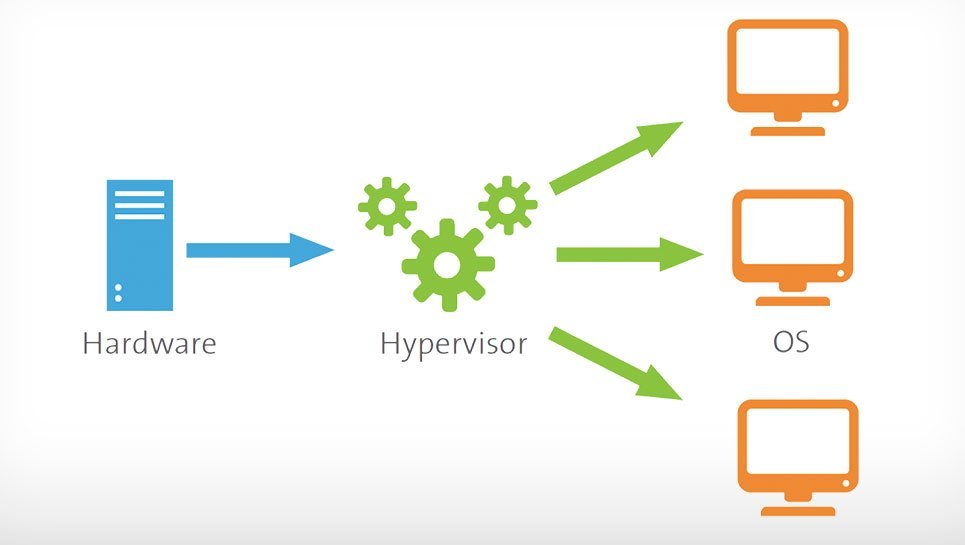
A Hypervisor, also known as a Virtual Machine Monitor or VMM, is software that creates and manages...
Read more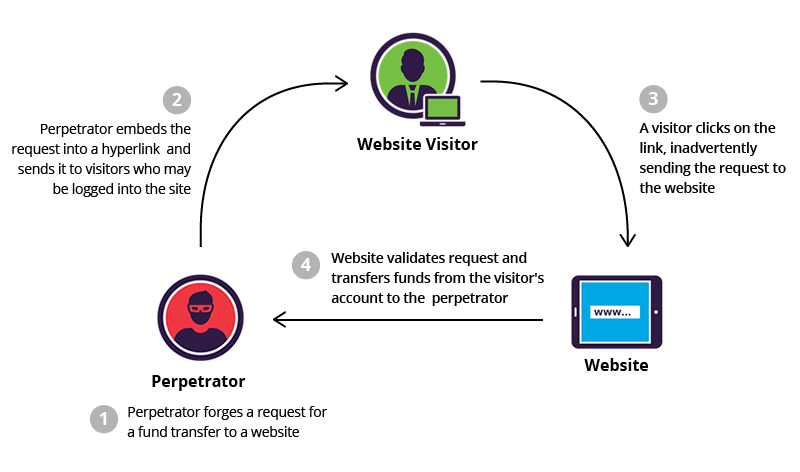
Cross-Site Request Forgery (CSRF), also known as XSRF, is an attack method that fools a web browser...
Read more
The IETF (Internet Engineering Task Force) is the organization that defines standard Internet operating...
Read more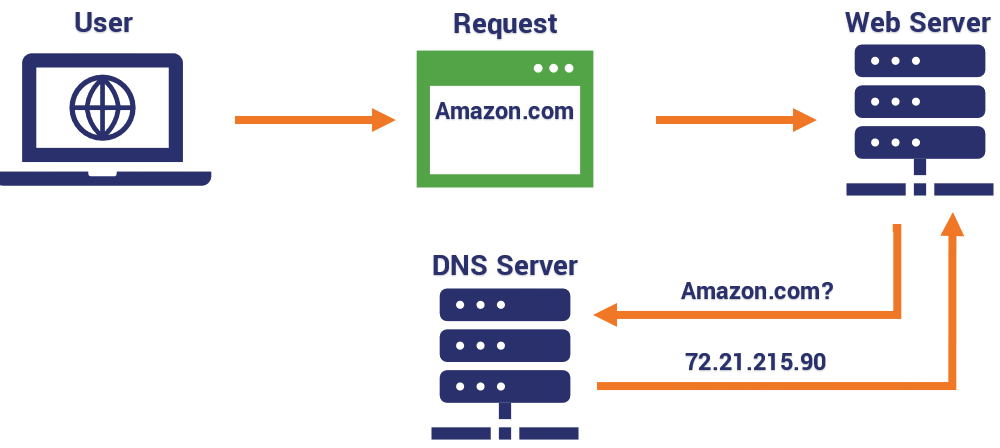
A Domain Name System (DNS) is essentially the 'phonebook' of the Internet. DNS is an elaborate,...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
