"CyberHoot's cyber awareness training is a game-changer for businesses looking to build a strong security culture."
Dynamic Code Analysis is a method used to analyze an application during its execution. This Dynamic...
Read more
Voice over Internet Protocol (VoIP) is essentially a telephone connection over the Internet. The data is...
Read more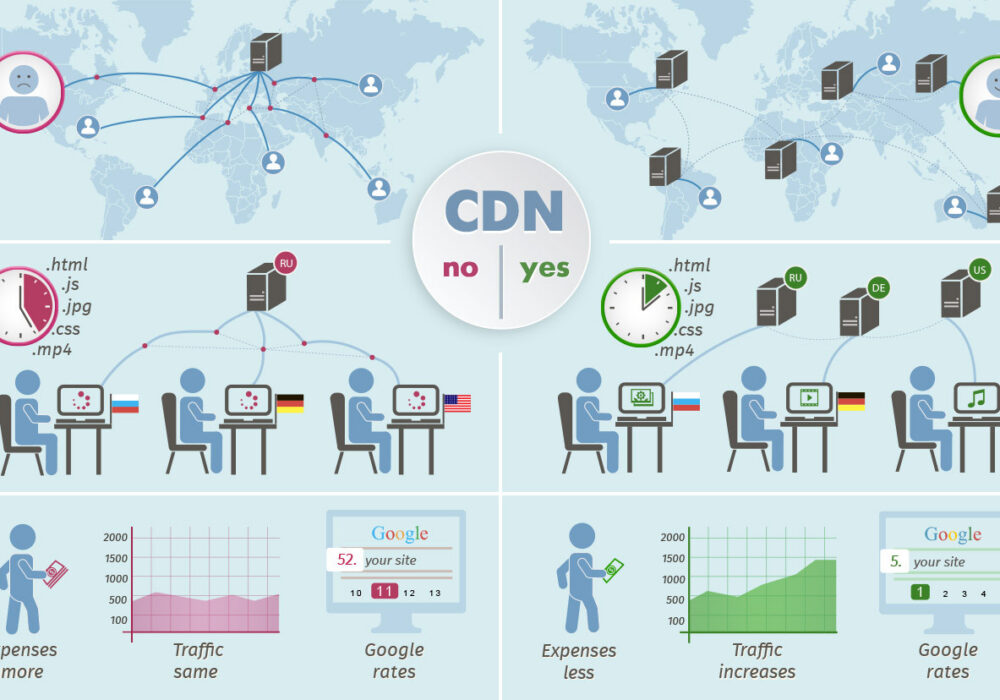
A Content Delivery Network (CDN) is a geographically distributed group of servers that work...
Read more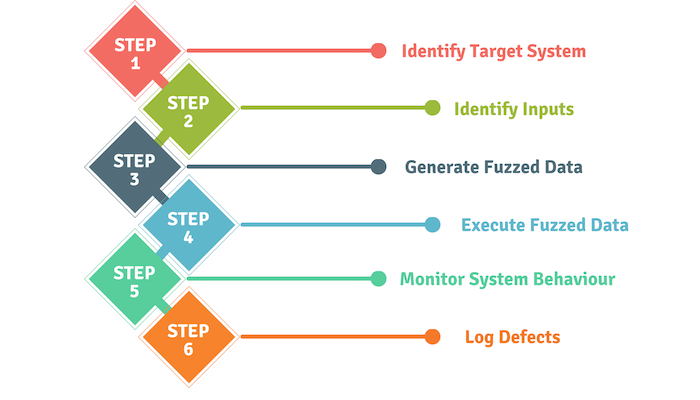
Application Fuzzing, originally developed by Barton Miller at the University of Wisconsin in...
Read more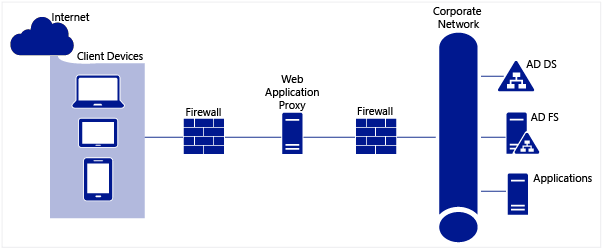
An Application Proxy is one of the most secure firewall types that can be deployed. The...
Read more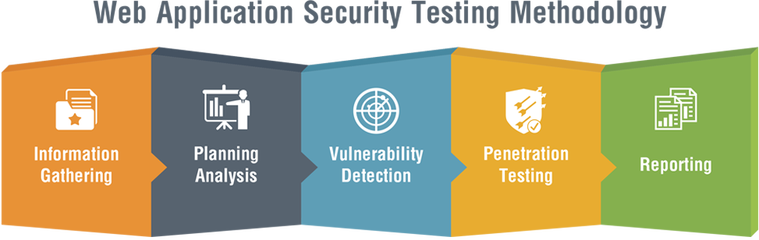
An Application Security Assessment is performed either manually or automatically, generally...
Read more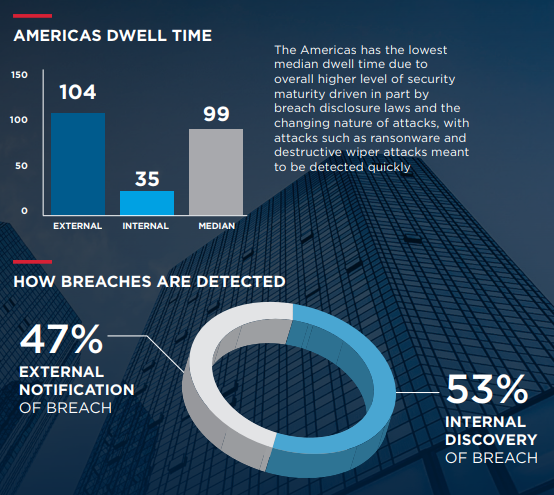
Dwell Time is the amount of time threat actors go undetected in an environment. In other words, when a...
Read more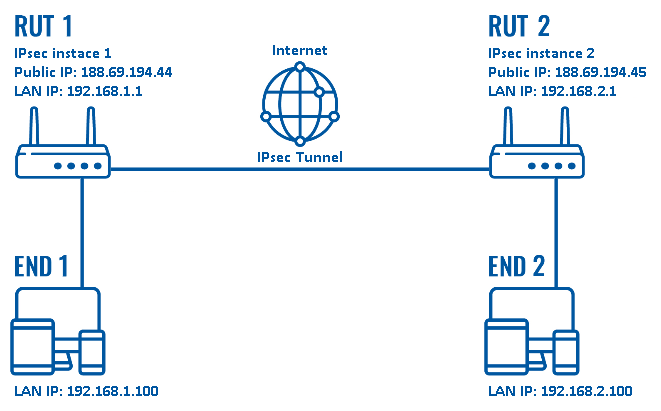
Internet Protocol Security (IPSec) is a set of protocols that provides security for Internet Protocol using...
Read more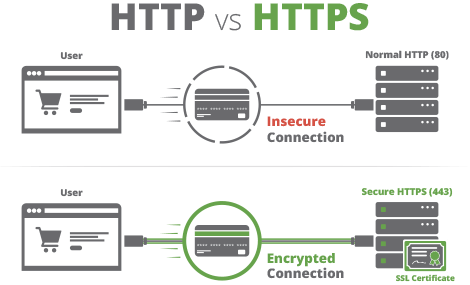
A Secure Socket Layer (SSL) is a security protocol developed by Netscape in the 1990's for sending...
Read more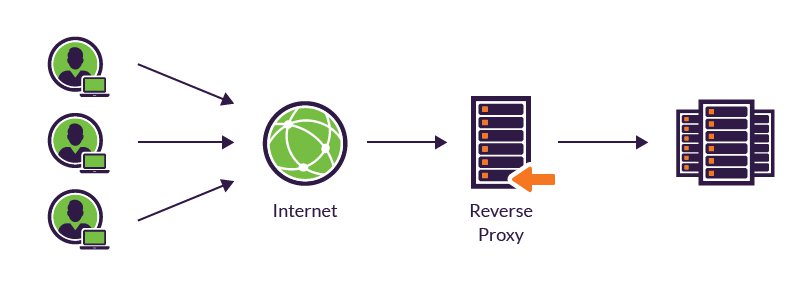
A Reverse Proxy is a server that sits in front of one or more web servers, intercepting requests from...
Read more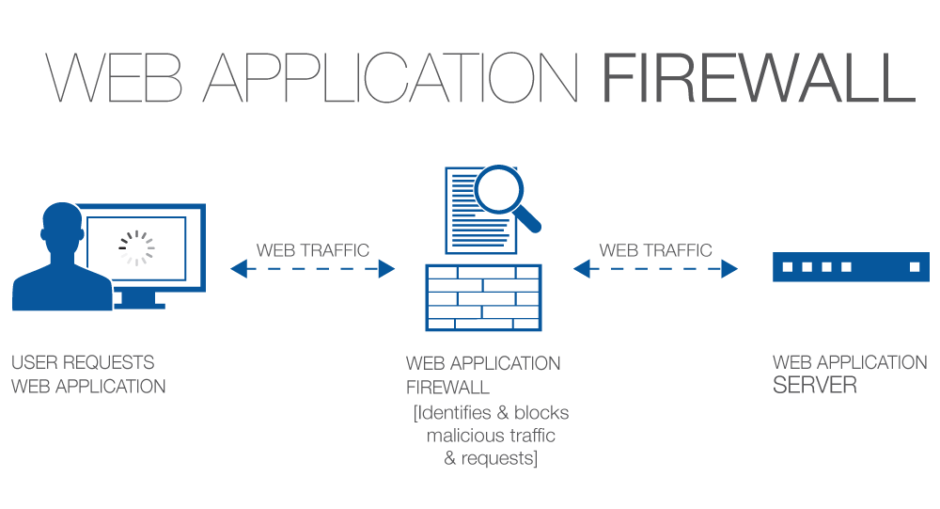
A Web Application Firewall (WAF) is used to protect web applications by filtering and...
Read more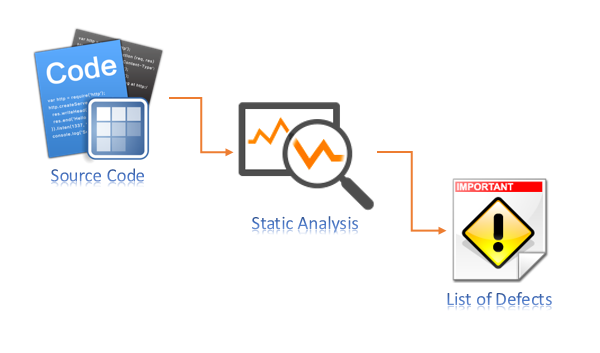
Static Code Analysis is the analysis of software code when the program is not running. The analysis of...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
