"The ease of setup and use for both administrators and users was immediately apparent. The automated training and phishing awareness features are major time savers for HR and IT teams”
Open source software (OSS), unlike proprietary software, is software that keeps the code open so IT...
Read more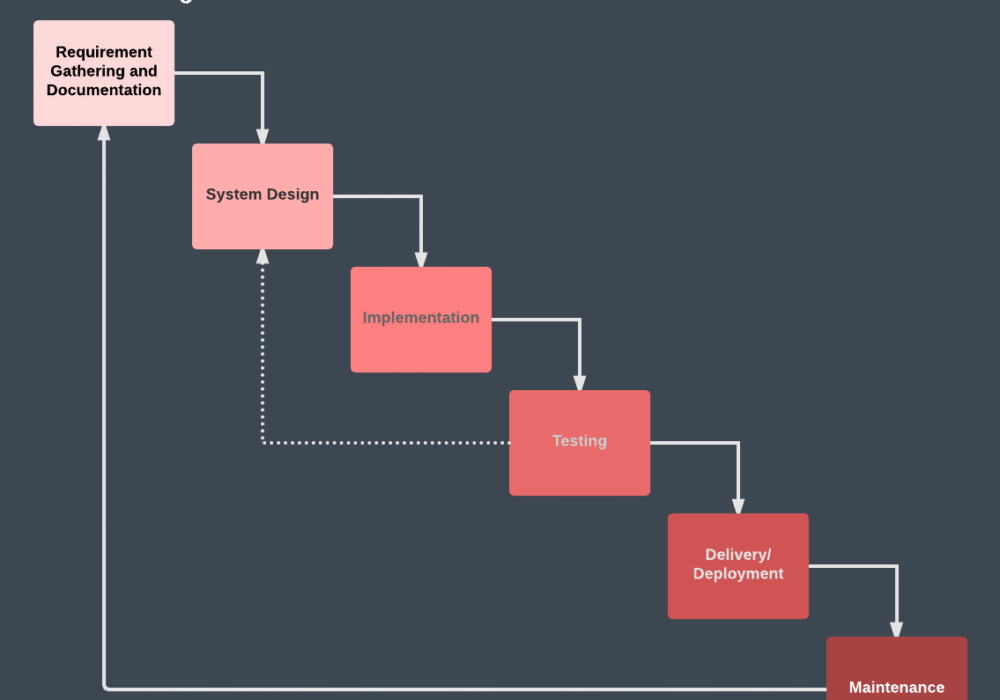
The Waterfall Development Methodology was the first process method used in the Software...
Read more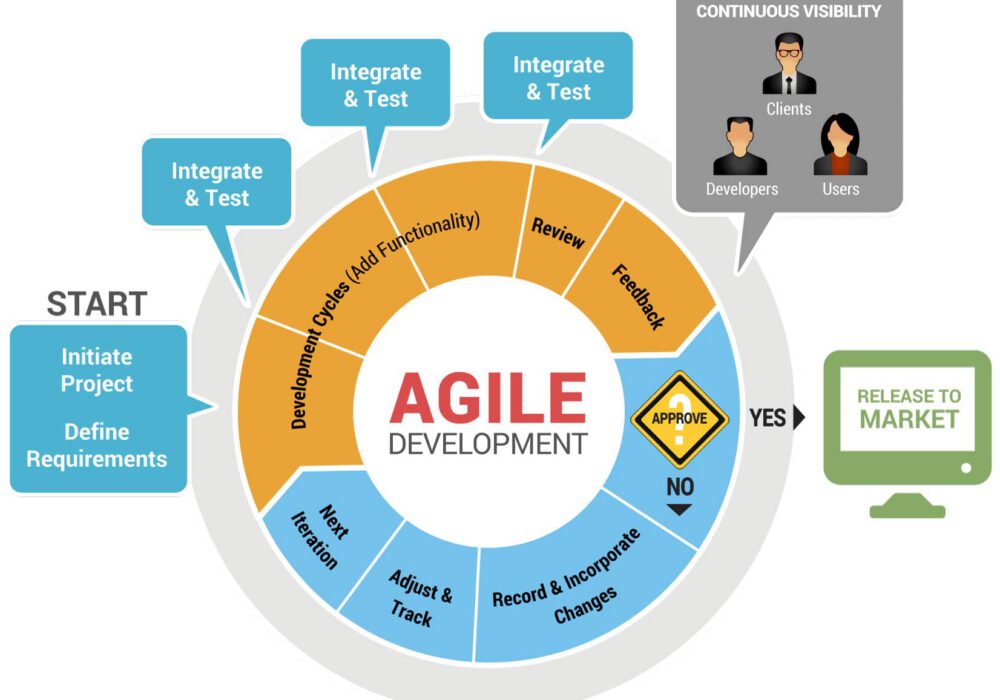
The Agile Development Methodology refers to a practice that uses continuous improvement and testing in...
Read more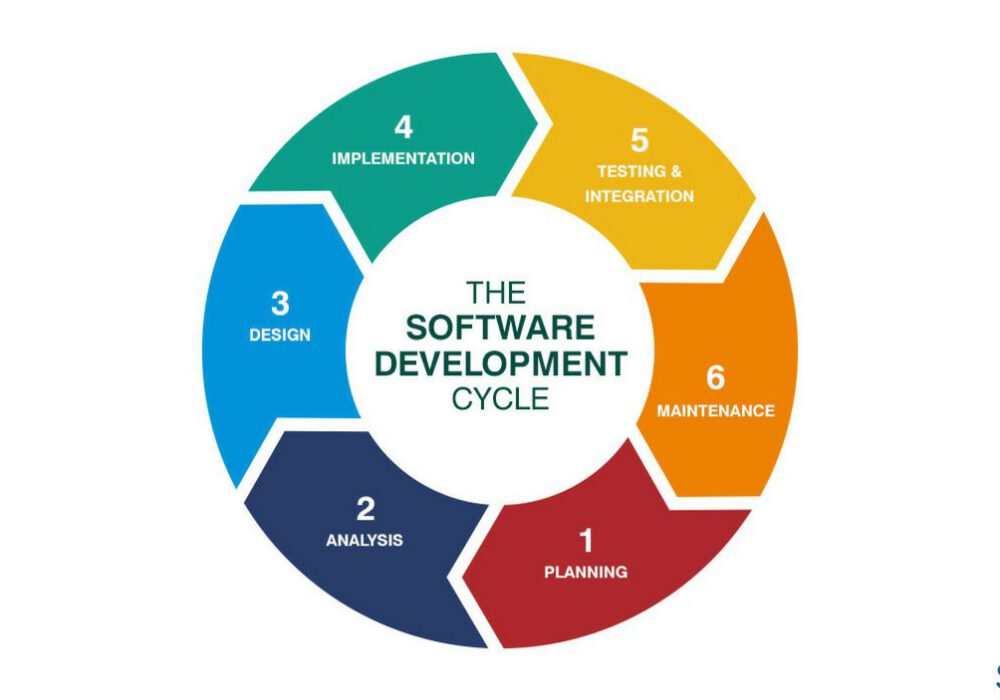
Software Development Life Cycle (SDLC) is the process companies follow to produces quality software in an...
Read more
Email Impersonation is a form of phishing attack where a hacker impersonates someone else in the hopes it was...
Read more
MAZE Ransomware is a form of ransomware that poses a triple threat to your data security. With MAZE,...
Read more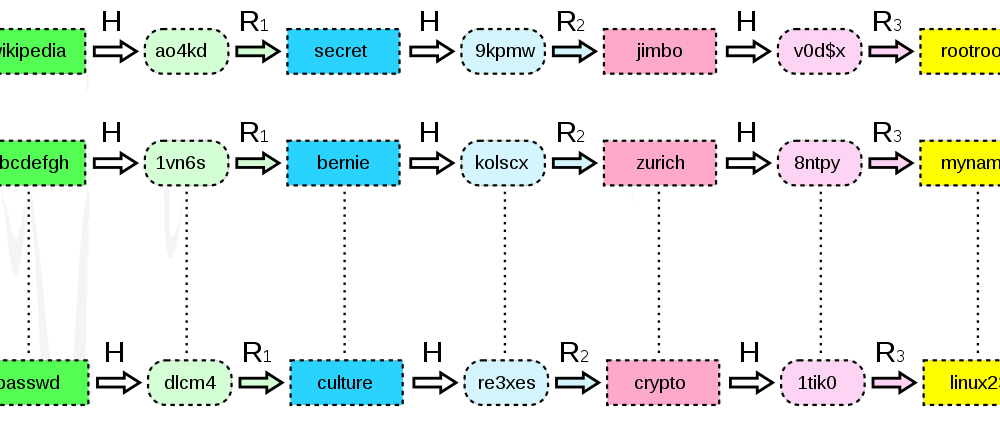
A Rainbow Table was a resource used for hacking the cryptographic hash functions in order to discover...
Read more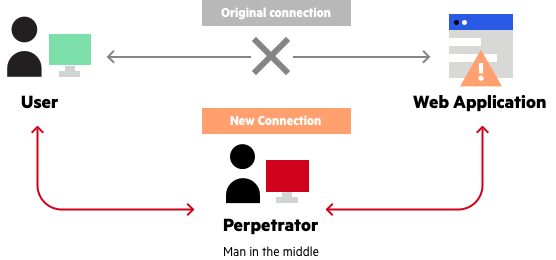
Adversary in the Middle (AITM) Attack (formerly referenced as Man-in-the-Middle) is a technical...
Read more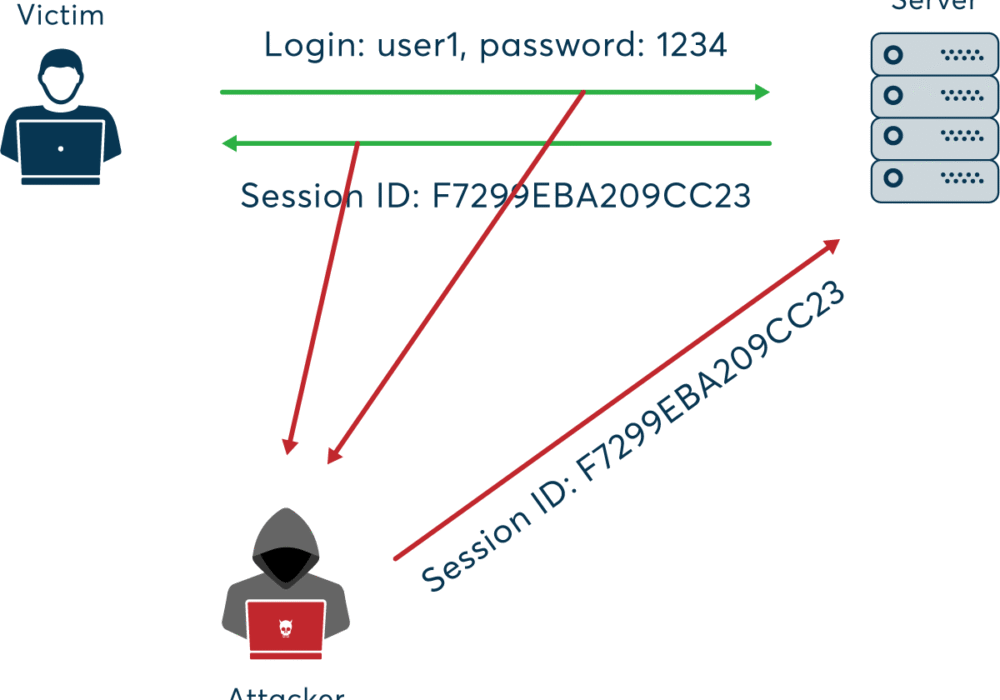
A Session Hijacking Attack occurs when a user session is taken over by an attacker. A normal session...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
