"CyberHoot has been a game-changer for us - simple to deploy, highly effective in raising awareness, and a great fit for MSPs looking to strengthen client security postures without adding complexity."
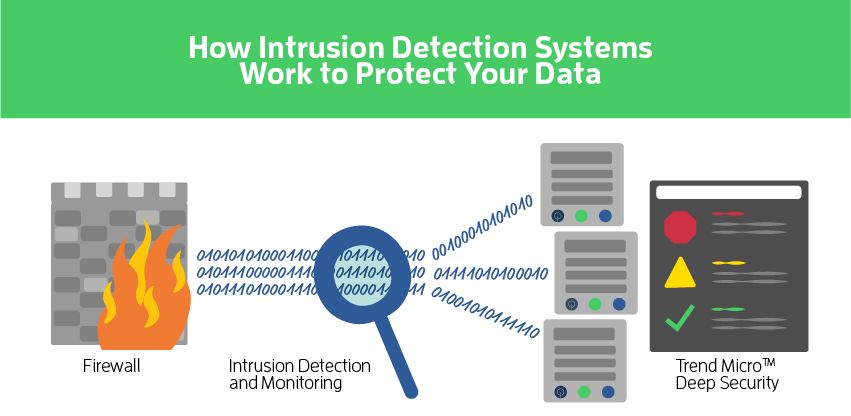
Network-based Intrusion Prevention Services (aka NIPS) is a preemptive approach to network security used to...
Read more
Image Source Intrusion Detection is the process and methods for analyzing information from...
Read more
Image Source Information Technology (IT) is any equipment or interconnected system or subsystem of equipment...
Read more
Image Source Information and Communication(s) Technology (ICT) is any information technology,...
Read more
Image Source Machine Learning and Evolution is a field concerned with designing and developing artificial...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now An Electronic Signature, also known as an...
Read more
Image Source Authenticity is a property achieved through cryptographic methods of being genuine and being...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Malicious Code is harmful computer code or...
Read more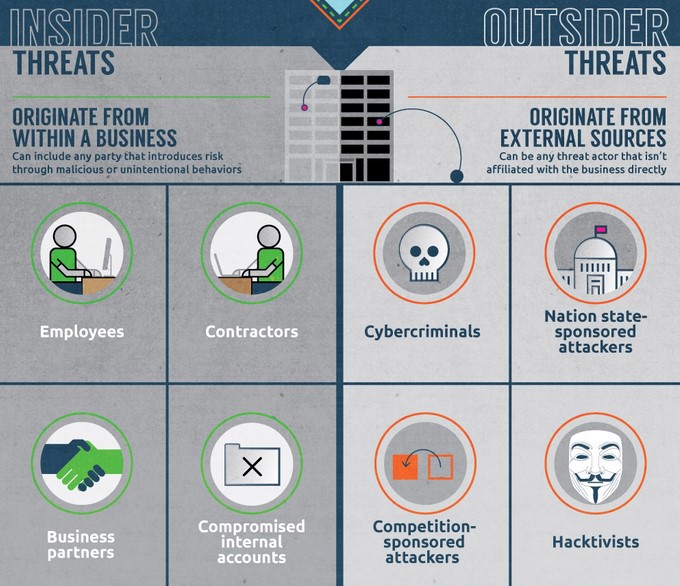
An Insider Threat is a person or group of persons within an organization who pose a potential risk of...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
