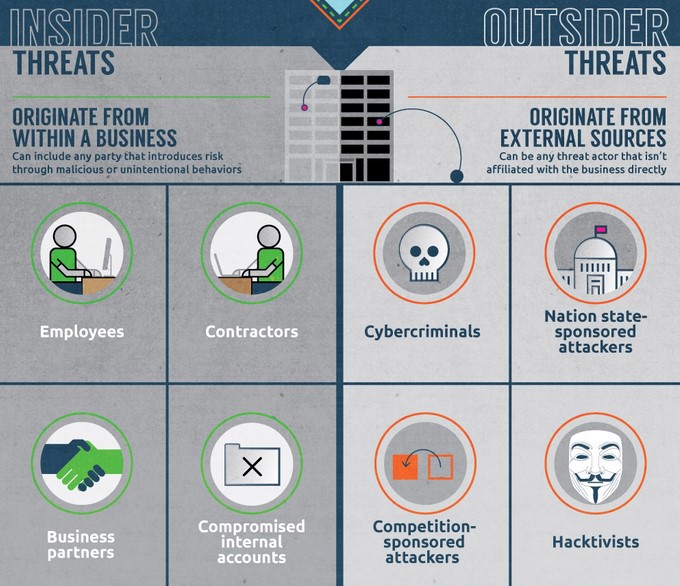
 An Insider Threat is a person or group of persons within an organization who pose a potential risk of harm to a company. That harm can be in the form of a security breach, the theft of intellectual property, or even damage to a company’s brand through accidental exposure of sensitive information. These threats can originate from employees, contractors, business partners, or even internal accounts that have been breached.
Insider threats are realized when an Internal threat actor(s) exploits their inside knowledge of or access to an entity’s security program, computer systems, services, products, facilities, or critical data and use that knowledge or access to cause harm.
It is important to remember that not all insider threats are malicious. Some compromises occur due to insider accidents such as publishing a Website without appropriate content controls or permission restrictions leading to data being exposed accidentally to the Internet.
An Insider Threat is a person or group of persons within an organization who pose a potential risk of harm to a company. That harm can be in the form of a security breach, the theft of intellectual property, or even damage to a company’s brand through accidental exposure of sensitive information. These threats can originate from employees, contractors, business partners, or even internal accounts that have been breached.
Insider threats are realized when an Internal threat actor(s) exploits their inside knowledge of or access to an entity’s security program, computer systems, services, products, facilities, or critical data and use that knowledge or access to cause harm.
It is important to remember that not all insider threats are malicious. Some compromises occur due to insider accidents such as publishing a Website without appropriate content controls or permission restrictions leading to data being exposed accidentally to the Internet.
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

As smart homes get smarter, so do their habits of watching, sensing, and reporting. Enter WiFi Motion Detection, a...
Read more
Spoiler alert: If you’re still using “password123” or “iloveyou” for your login… it’s time for an...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
