"CyberHoot is a great option for Cybersecurity for our schools. The videos and other training are very user-friendly. Their support is fantastic as well."
Quickly access our step-by-step guides and answers to help you make the most of CyberHoot.
Updated: May 12th, 2026 This article is a reference to CyberHoot's mail relay IP Addresses and Domain names. The...
Read more
Google Workspace "Report Phish" Integration 🔹 Overview Gmail's built-in "Report Phishing" button...
Read more
If your mail filter and spam settings are already configured, this guide covers the one remaining step:...
Read more
Microsoft 365 Built-in “Report Phish” Integration 🔹Overview Microsoft 365 supports a...
Read more
PowerShell Script for Safe Links Configuration in Microsoft 365 Overview This PowerShell script configures...
Read more
CyberHoot – Perception Point Allowlisting Instructions Organizations using Perception Point for...
Read more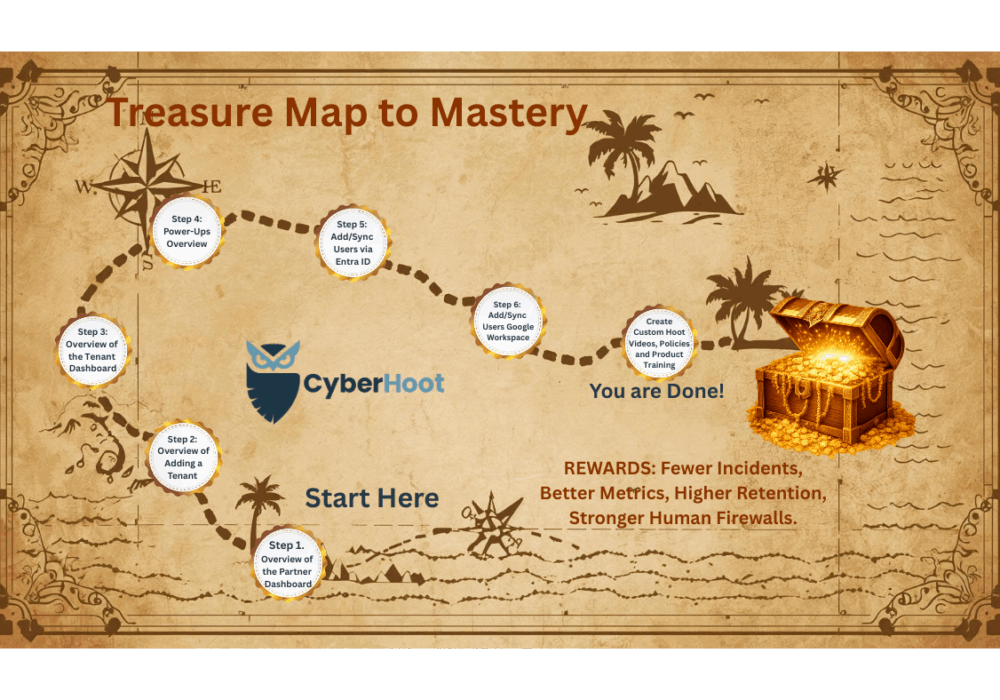
Welcome to Your CyberHoot Mastery Guide! You made it! This is your visual treasure map to CyberHoot success....
Read more
This article explains how Autopilot’s CustomHoots PowerUp works and provides guidance on creating your own...
Read more
This document outlines how report delivery and recipient configuration work across Partner and Tenant levels,...
Read more
Why Does My AttackPhish Report Show Users Opening and Clicking Emails They Never Saw? Overview If...
Read more
This guide walks you through setting up and managing the CyberHoot–SyncroMSP integration using the CyberHoot...
Read more
This guide walks you through setting up and managing the CyberHoot–SyncroMSP integration using the CyberHoot...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
