A Voice Firewall logs, monitors, and controls all inbound and outbound voice network activity on a per-call basis through user-defined Call Access Control (CAC) policies. These detailed security and usage policies alert or prevent malicious use of your company voice resources by internal or external callers.
Voice Firewalls help prevent data network exploits over modems, attacks on voice systems and other key infrastructure, unauthorized Internet sessions on phone lines, data leakage, harassing/threatening calls, long-distance abuse, calls to/from restricted parties, and other forms of phone line disruption, misuse, and abuse.
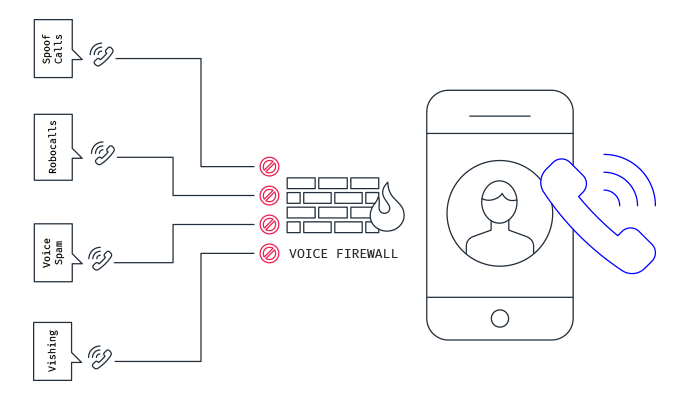
In short, Voice Firewalls can block some inbound calls to your organization that are malicious, like robocalls, spam, and vishing attacks.
Voice Firewalls are a fairly new technology, but could be beneficial for companies that have problems with malicious phone calls. For most companies, it’s likely not something that will be needed in their security stack. This is particularly true for companies with employees working remotely.
The single best thing that can be done to prevent security issues from malicious phone calls is to train users on avoiding Vishing and Social Engineering attacks so they know what to do if they encounter them. Additionally, following the actions below will help improve your cybersecurity posture significantly.
The following recommendations will help you and your business stay secure with the various threats you may face on a day-to-day basis. All of the suggestions listed below can be gained by hiring CyberHoot’s vCISO Program development services.
Each of these recommendations, except cyber-insurance, is built into CyberHoot’s product and virtual Chief Information Security Officer services. With CyberHoot you can govern, train, assess, and test your employees. Visit CyberHoot.com and sign up for our services today. At the very least continue to learn by enrolling in our monthly Cybersecurity newsletters to stay on top of current cybersecurity updates.
Sources:
Related Readings:
Vishing, A Threat You Haven’t Thought About
Related Terms:
CyberHoot does have some other resources available for your use. Below are links to all of our resources, feel free to check them out whenever you like:
Note: If you’d like to subscribe to our newsletter, visit any link above (besides infographics) and enter your email address on the right-hand side of the page, and click ‘Send Me Newsletters’.
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

A Practical Brief for vCISOs THE WARNING WE IGNORED OR COULD NOT UNDERSTAND For years, the most credible...
Read more
A guide to spotting senior executive impersonation scams before the fake CEO gets a real wire transfer. It...
Read more
Artificial Intelligence (or AI) is making phishing emails smarter, malware sneakier, and credential theft easier...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
