Scareware is a type of malware tactic used to manipulate victims into downloading or buying malware-infested software. Scareware attacks are used by hackers and cybercriminals to trick users into thinking they must buy malware masked as real cybersecurity software.
Your company employees must be aware of these potential threats when at work and at home. It’s best to train and educate your users on common attacks, the best cybersecurity practices available, and on the tools and techniques you can use to protect yourself. The following minimum essential recommendations will help your company and its users become more aware and more secure if adopted.
The following recommendations will help you and your business stay secure with the various threats you may face on a day-to-day basis. All of the suggestions listed below can be gained by hiring CyberHoot’s vCISO Program development services.
Each of these recommendations, except cyber-insurance, is built into CyberHoot’s product and virtual Chief Information Security Officer services. With CyberHoot you can govern, train, assess, and test your employees. Visit CyberHoot.com and sign up for our services today. At the very least continue to learn by enrolling in our monthly Cybersecurity newsletters to stay on top of current cybersecurity updates.
Sources:
Additional Reading:
Don’t Get Scammed by Scareware: 3 Easy Tips to Stay Safe
Related Terms:
CyberHoot does have some other resources available for your use. Below are links to all of our resources, feel free to check them out whenever you like:
Note: If you’d like to subscribe to our newsletter, visit any link above (besides infographics) and enter your email address on the right-hand side of the page, and click ‘Send Me Newsletters’.
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

If a Chrome extension promises to remove security pop-ups and generate MFA codes, that should make you...
Read more
Cyberattacks usually start with phishing emails or weak passwords. This one did not. Security researchers...
Read more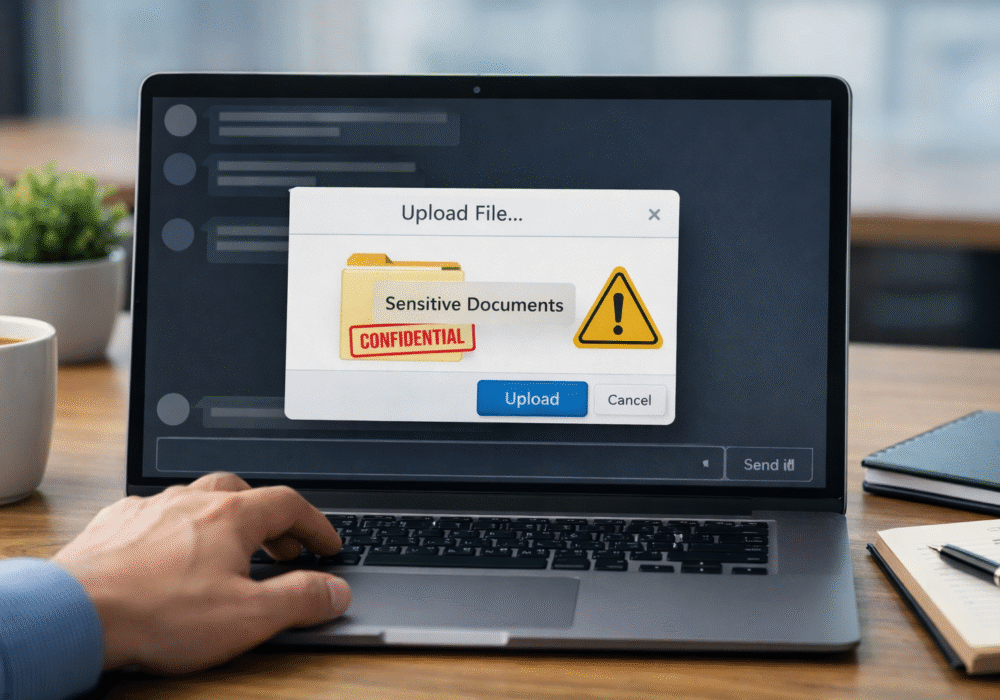
Not surprising when Trouble Ensues Last summer, the interim head of a major U.S. cybersecurity agency uploaded...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
