A Ping of Death (PoD) is a type of Denial of Service (DoS) attack that deliberately sends IP packets larger than the 65,536 bytes allowed by the IP protocol. One of the features of TCP/IP is fragmentation; allowing a single packet to be broken down into smaller segments.
This DoS attack started back in the 90’s, where most operating systems didn’t know what to do when they received an oversized packet, so they froze, crashed, or rebooted. Ping of Death attacks are particularly brutal because the identity of the attacker sending the oversized packet could be easily ‘spoofed’ since the attacker doesn’t need to know anything about the victim, except their IP address. By the end of the 90’s, operating systems made patches available for users to avoid the ping of death. Still, many sites block Internet Control Message Protocol (ICMP) ping messages at their firewalls to prevent any future variations of this kind of denial of service attack.
We are not saying it won’t happen, but the cost of protection is so great in many cases, the advice to an SMB is to know what it is, and establish a relationship with a DDoS protection vendor without paying for protection. DDoS protection vendors include Arbor Networks, AT&T, Verizon, and Akamai. Mid-to-Large enterprises should have contracts in place to protect themselves in seconds when hit with a DDOS attack. SMB’s should not.
Sources:
Additional Reading:
How Does a Ping of Death Attack Work?
Windows “Ping of Death” Bug Revealed – 2020
Related Terms:
Distributed Denial of Service (DDoS)
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

Remember 2020? We scanned QR codes for everything. Restaurant menus. Parking meters. That awkward moment at a...
Read more
Phishing emails used to be easy to spot. Bad grammar. Weird links. Obvious scams. Those days are...
Read more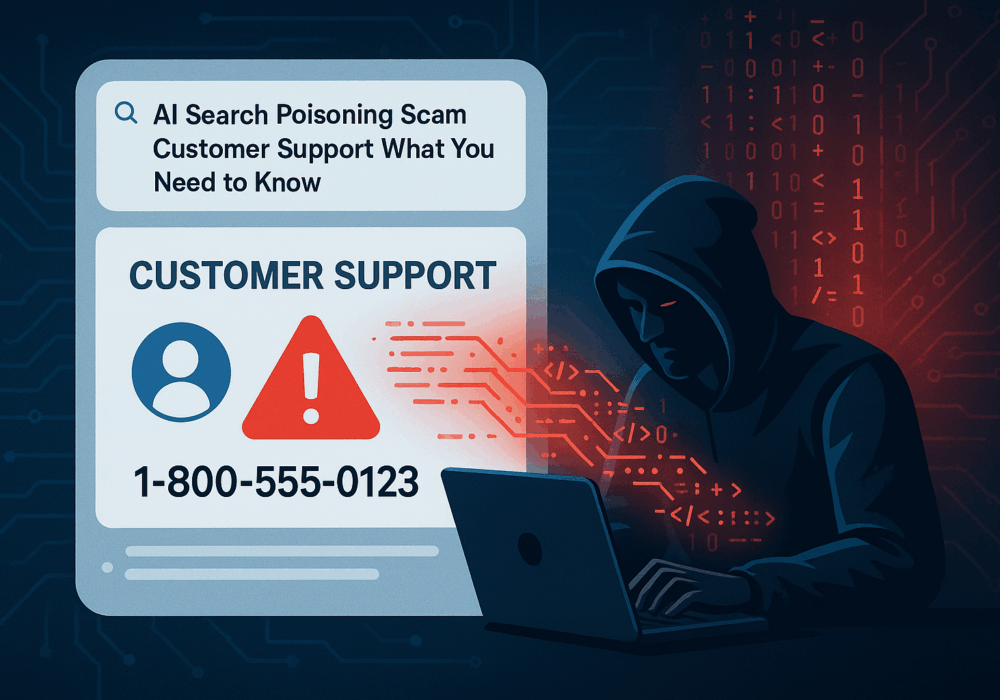
Cybercriminals always follow Internet eyeballs. Not literally, but figuratively. And today's eyeballs are...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
