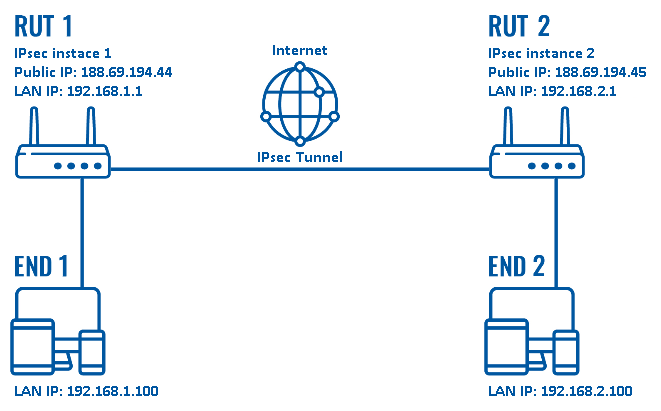
Internet Protocol Security (IPSec) is a set of protocols that provides security for Internet Protocol using advanced cryptography. IPSec is similar to a Secure Socket Layer (SSL), except that SSLs connections are typically used by web browsers, while IPSec tunnels (usually) require a client application installation. Furthermore, IPSec tunnels can access both web and non-web applications, whereas SSL requires workarounds for non-web access such as file sharing. IPSec was designed to serve the IP Protocol, so it is mainly used to support Virtual Private Networks (VPN) over the Internet.
Source: Techopedia, PCMag
Additional Reading: VPN protocols: What Are They And Which Should I Use?
Related Terms: Secure Socket Layer (SSL), Point to Point Tunneling Protocol (PPTP), Virtual Private Network (VPN)
IPSec is something that should be considered if you have employees working from home or remotely that also need access to resources onsite at your business offices. Sometimes those resources are internally hosted applications and other times its file servers with internally accessed data. If your employees consistently work from home, then a VPN is one option for a strong and secure solution to enable remote worker productively. However, if all they do from home is work on Email, then a VPN may not be necessary since email can be easily secured in other ways via O365 and two-factor authentication on company issued devices. Virtual Private Networks also double as a secure conduit for traveling workers to reach the internet when joining WiFi networks that might not be entirely trustworthy. Once an IPSec tunnel is setup, no interloping hacker can read the data between the device (laptop) and the remote business device terminating the IPSec encrypted tunnel.
In all cases, never rely solely on a password authenticated VPN. The minimum security practice is to enable two-factor authentication on your VPN. There are too many passwords breached online that could be used by hackers to breach your VPN network. Always pair VPN access with a second factor.
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

New benchmark data names MDASH and Claude Mythos Preview are the top AI agents finding zero-day vulnerabilities...
Read more
One Forgotten Password, Almost a Catastrophe A single Windows machine at a retail store location had a cached...
Read more
You now have five important reasons to start a router security conversation with your small business clients this...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
