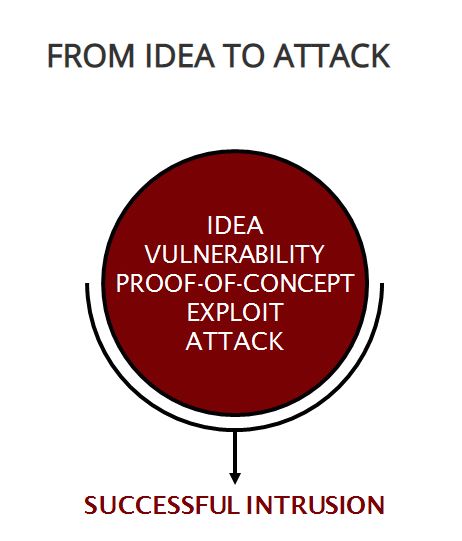
Exploitation Analysis is cybersecurity work where a person: analyzes collected information to identify vulnerabilities and potential for exploitation. This is done to attempt to “fill in the gaps” in the security of your system.
Your business needs to take proactive measures today to first reduce its chances of being hit by ransomware, phishing, or other cybersecurity attacks. Secondly, validate backups and disaster recovery plans are current and functioning in case you end up hit with ransomware. CyberHoot recommends the following best practices to avoid, prepare for, and prevent damage from these attacks:
Start building your robust, defense-in-depth cybersecurity plan at CyberHoot.
Related Term: Exploit
Source: NICE Workforce Framework
CyberHoot does have some other resources available for your use. Below are links to all of our resources, feel free to check them out whenever you like:
Note: If you’d like to subscribe to our newsletter, visit any link above (besides infographics) and enter your email address on the right-hand side of the page, and click ‘Send Me Newsletters’.
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

A Practical Brief for vCISOs THE WARNING WE IGNORED OR COULD NOT UNDERSTAND For years, the most credible...
Read more
A guide to spotting senior executive impersonation scams before the fake CEO gets a real wire transfer. It...
Read more
Artificial Intelligence (or AI) is making phishing emails smarter, malware sneakier, and credential theft easier...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
