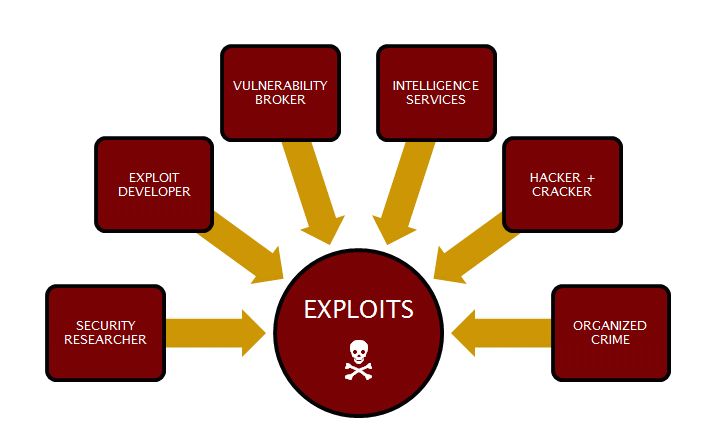
An exploit is a technique to breach the security of a network or information system in violation of security policy.This strategy takes advantage of the application or systems flaw so the hackers or cyber criminals can take use it to their benefit.
Your business needs to take proactive measures today to first reduce its chances of being hit by ransomware, phishing, or other cybersecurity attacks. Secondly, validate backups and disaster recovery plans are current and functioning in case you end up hit with ransomware. CyberHoot recommends the following best practices to avoid, prepare for, and prevent damage from these attacks:
Start building your robust, defense-in-depth cybersecurity plan at CyberHoot.
Additional Reading: Exploit Pricing: a Research Paper
Related Terms: Exploit Analysis
Source: ISO/IEC 27039 (draft), DHS personnel
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

Ever had your phone suddenly lose service for no reason, followed by a flood of “reset your password”...
Read more
As smart homes get smarter, so do their habits of watching, sensing, and reporting. Enter WiFi Motion Detection, a...
Read more
Spoiler alert: If you’re still using “password123” or “iloveyou” for your login… it’s time for an...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
