Dissemination of Information refers to the distributing of a company’s or customer specific information to the public, whether through printed or electronic documents, or other forms of media. “Dissemination of information” does not include intra-company use of information or responding to requests for “access to information” from a company’s employees.
From an Information Security perspective, information that needs dissemination should be accurate (have Integrity), should be available when you need it (Availability), and only given out to those with a Need to Know (Confidentiality). These are the CIA best practices of Information Handling. Business owners should have an Information Handling Policy in place that sets requirements for employees to follow based upon the type of information they have access to. This policy should outline the types of data that your business has which falls into certain categories such as Public (General), Restricted (Sensitive), and Confidential (Critical). It should also spell out how that information is to be protected throughout its life in motion and at rest.
However, there is more to information dissemination than just information security. The video below covers some leadership best practices around how to disseminate information, where to share it, when to share, and in what manner.
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

Cyberattacks usually start with phishing emails or weak passwords. This one did not. Security researchers...
Read more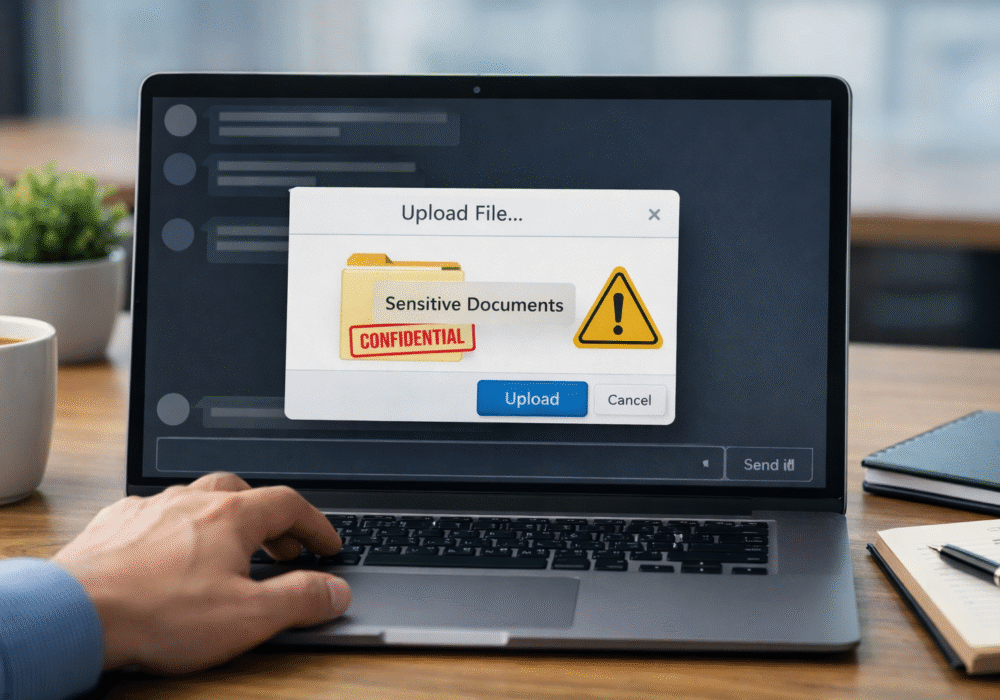
Not surprising when Trouble Ensues Last summer, the interim head of a major U.S. cybersecurity agency uploaded...
Read more
And How to Fix Them Let me make an educated guess. You moved to Google Workspace because it was supposed to...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
