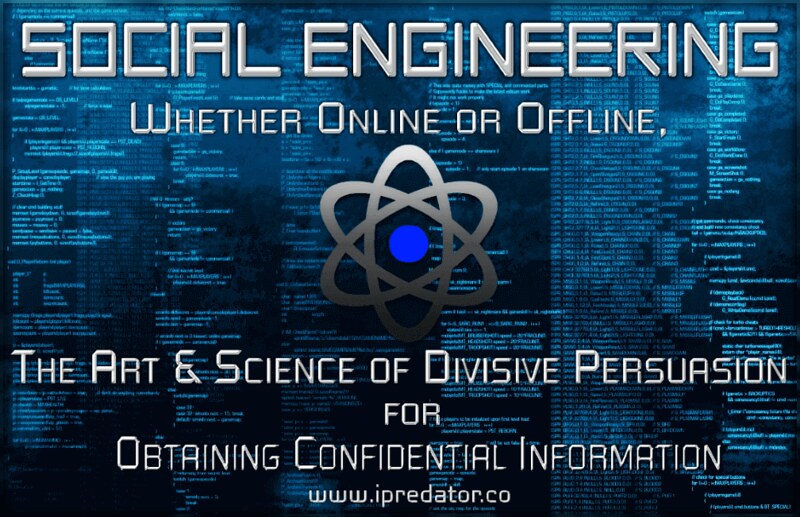
"While it is well known that there are many cyber security threats, sorting out how to protect yourself without accidentally exposing yourself can be a daunting task. For a small organization like ours, this type expertise and time to research it, are a rare commodity. Cyberhoot has provided us with reliable practices and training tools, in small, manageable increments, that leave us feeling confident and assured about cybersecurity."