"Craig and the CyberHoot team are great business partners! They are always open to enhancing their product, and ready to help my team with any deployment questions they may have. I am also an end user of the CyberHoot security..."

If you run or bike, you probably heard about the Garmin Ransomware attack, taking down its...
Read more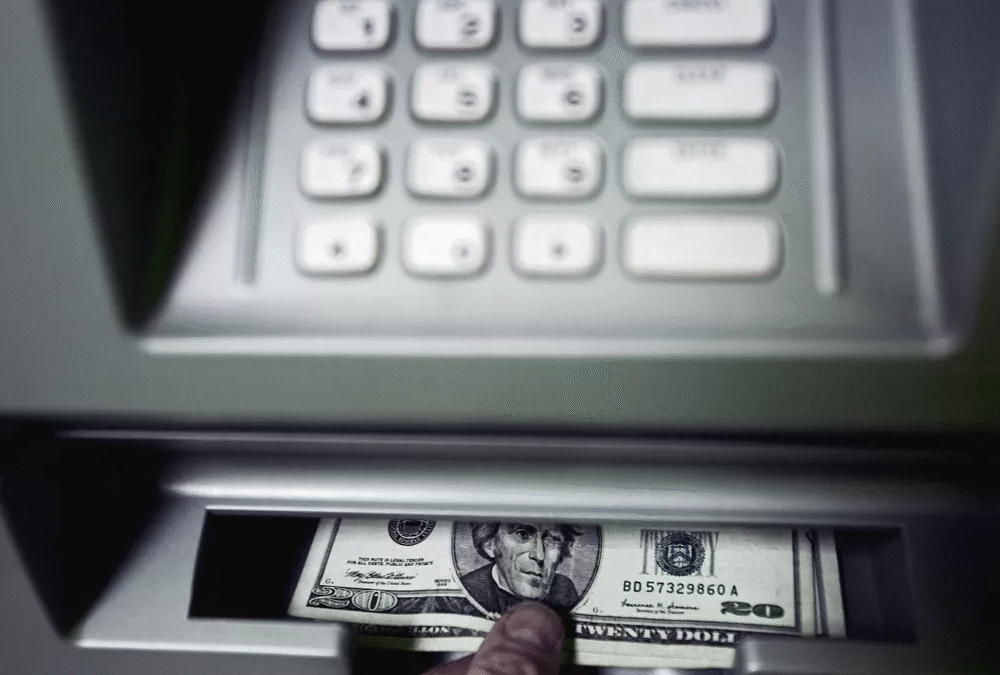
Automatic Teller Machines (ATM) have long been a target of enterprising criminals. In the 1980's when...
Read more
Back in June, the United States Secret Service (USSS) sent out a security alert about a spike in...
Read more
Since Coronavirus (COVID-19) gained pandemic status in early March 2020, hackers have been attacking...
Read more
During the coronavirus pandemic, Contact Tracing is being used to slow the spread of the virus. Contact...
Read more
Phishing attacks are something that everyone who uses the Internet must be aware of. For those who may...
Read more
OWASP stands for the Open Web Application Security Project. The OWASP Top 10 application security risks...
Read more
Following the General Data Protection Regulation (GDPR) enactment in the European Union (EU) in 2018,...
Read more
The Internet of Things (IoT) is any device or machine that has the ability to transfer data over a...
Read more
Three (3) Reasons for Policies and Procedures: All businesses are governed by laws, regulations, and legislative...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
