"Cybersecurity training is complicated, partnering with CyberHoot keeps it simple. Our users are engaged with little administrative overhead."
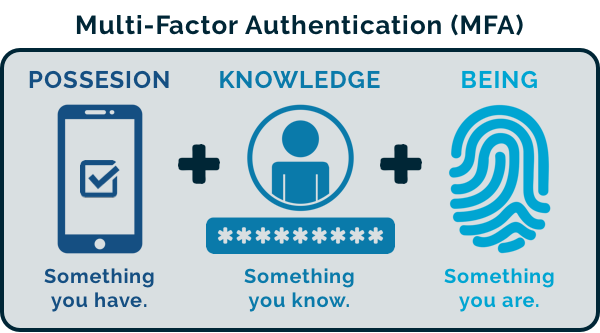
The Importance of Multi-Factor Authentication (MFA) into Cloud/SaaS Applications: CyberHoot recommends clients...
Read more
CyberHoot Power Platform: Automatic Type Customers The instructions below provide a walkthrough on how to add a...
Read more
If you're using Proofpoint's spam filtering software, you can safelist (whitelist) CyberHoot to allow your users...
Read more
Welcome to the CyberHoot Autopilot Platform: A Guided Tour for New Administrators Starting with a new platform can...
Read more
Welcome to the CyberHoot Power Platform: A Guided Tour for New Administrators Starting with a new platform can...
Read more
Adding users to CyberHoot's Power Platform via Azure AD/ Entra ID Sync (using Graph API) If your company uses...
Read more
This video was created specifically for MSPs with Super Admin access to CyberHoot's Power Platform and its...
Read more
The Entra ID sync is not functioning because the provided client secret has expired. To resolve this, you will...
Read more
Allow-Listing X-Headers is necessary in order for CyberHoot to send simulated phishing emails to bypass your...
Read more
This video provides end users with a quick overview in 2 min. of their Phishing Test by Assignment service. End...
Read more
Please note: Only Azure AD Government Community Cloud (GCC) environments need to follow these...
Read more
Please note: Only Azure AD Government Community Cloud (GCC) environments need to follow these...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
