"Managed Service Providers (MSP's) are constantly bombarded with new vendors and products that either overlap with a product already in our line cards or is difficult to get client buy in. Cyberhoot brings a new product/service to the MSP space..."

Secure your business with CyberHoot Today!!! Sign Up Now The National Institute of Standards and...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now The Cybersecurity and Infrastructure...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Geofencing is a technology for setting...
Read more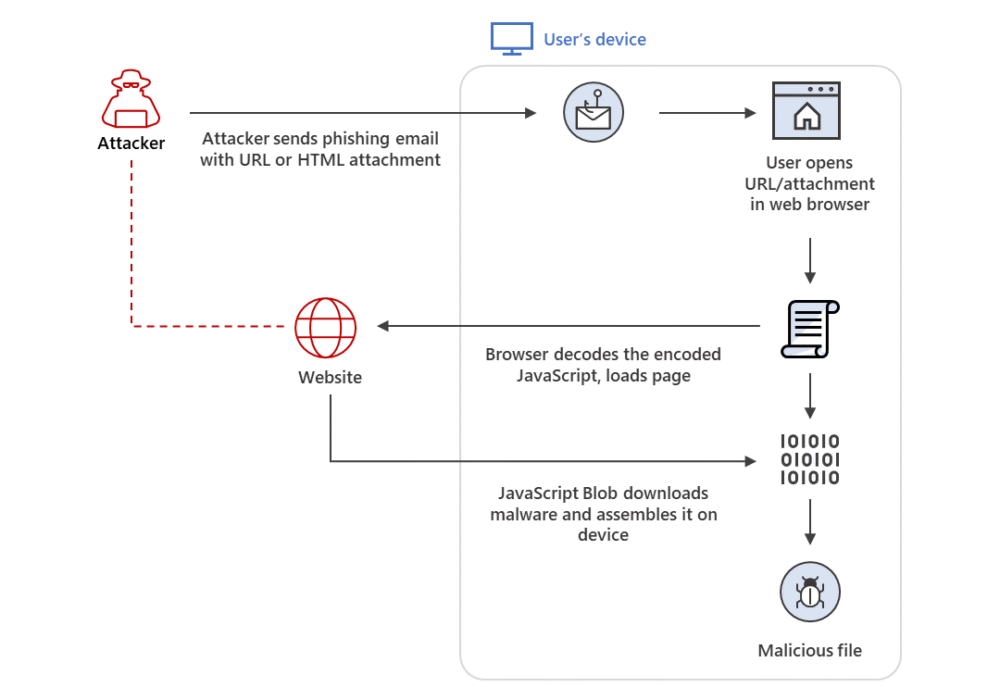
Secure your business with CyberHoot Today!!! Sign Up Now HTML Smuggling is an evasive malware...
Read more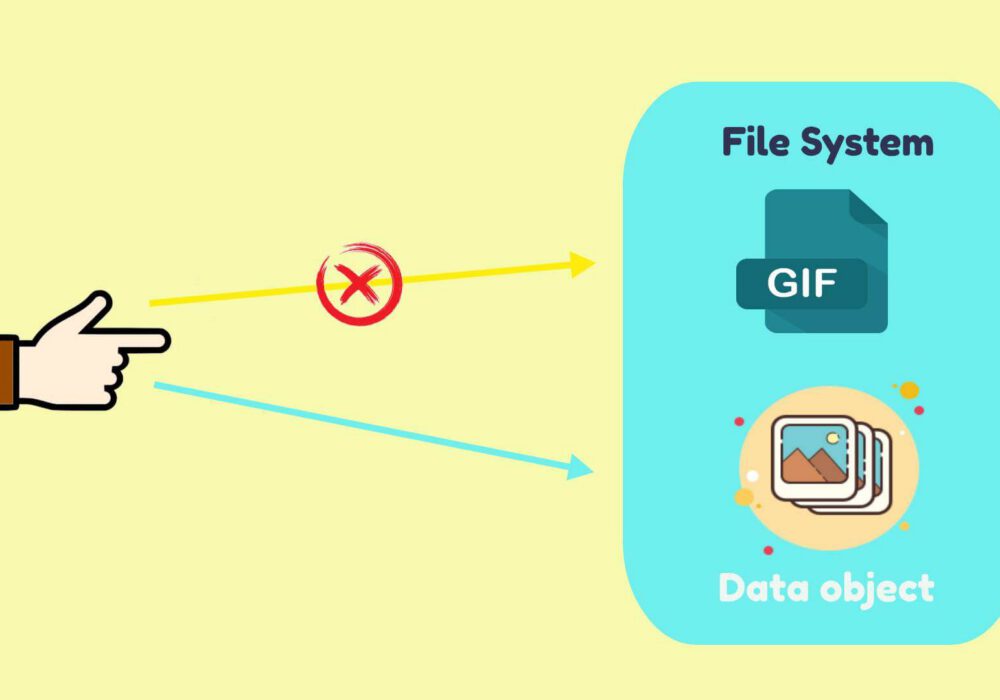
Secure your business with CyberHoot Today!!! Sign Up Now An Object Identifier (OID) is a specific,...
Read more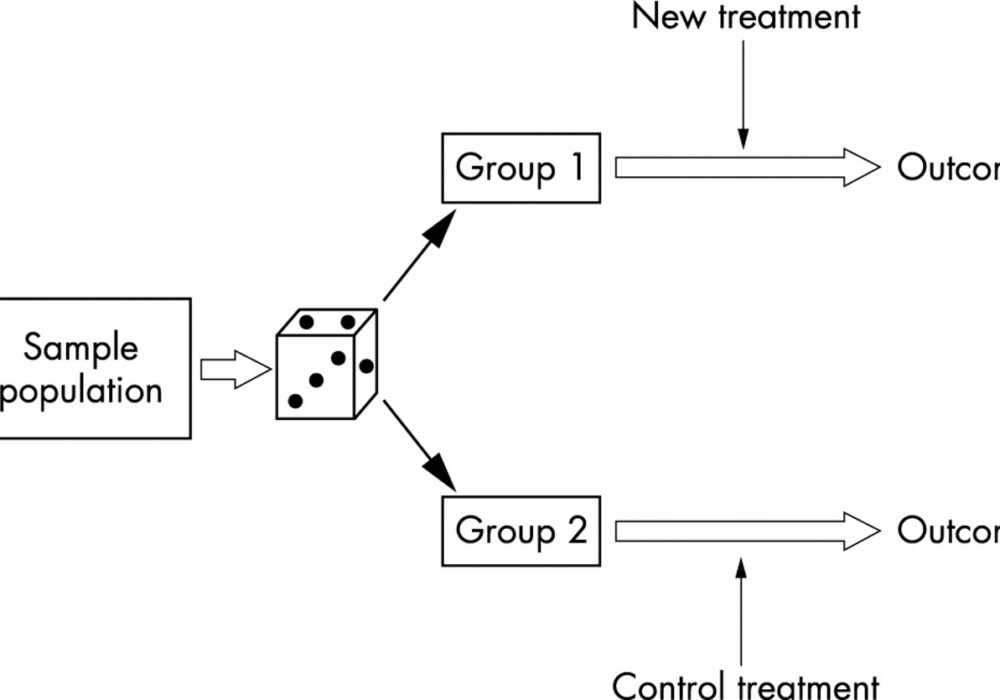
Secure your business with CyberHoot Today!!! Sign Up Now A Randomization Function is an algorithm or...
Read more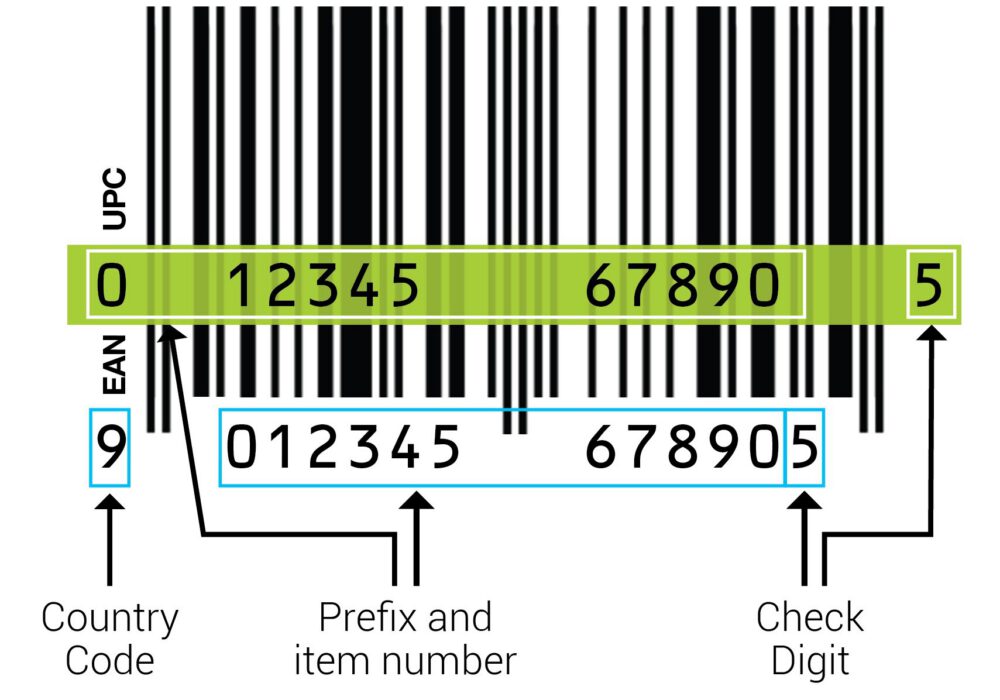
Secure your business with CyberHoot Today!!! Sign Up Now A Check Digit is a digit added to a string...
Read more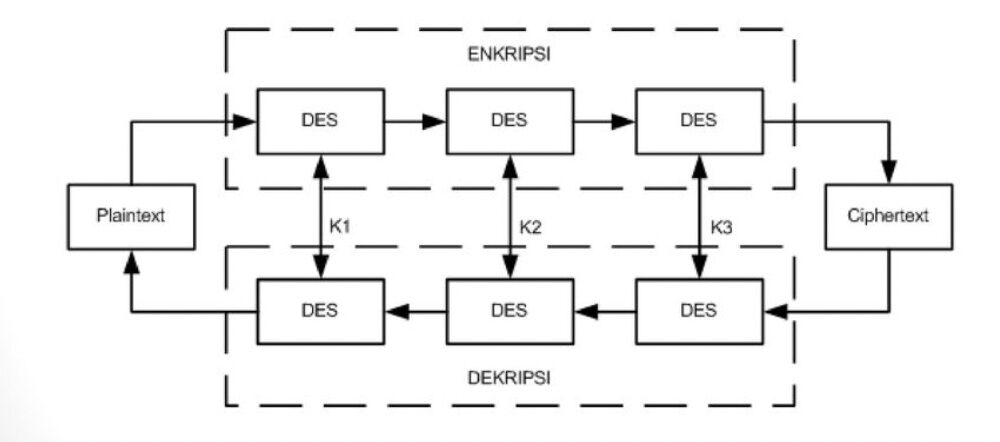
Secure your business with CyberHoot Today!!! Sign Up Now 3DES Encryption, also known as Triple Data...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Assembly Language is the most basic...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
