"Cybersecurity training is complicated, partnering with CyberHoot keeps it simple. Our users are engaged with little administrative overhead."

The Mac Myth Apple's Mac Operating Systems (OS) is impenetrable to malware. Myth. Recent malware...
Read more
During the coronavirus pandemic, Contact Tracing is being used to slow the spread of the virus. Contact...
Read more
Stalkerware is a category of invasive applications running on computers and smartphones that...
Read more
Cybersecurity experts are warning about growing demand for stolen YouTube login credentials on Dark web...
Read more
Phishing attacks are something that everyone who uses the Internet must be aware of. For those who may...
Read more
OWASP stands for the Open Web Application Security Project. The OWASP Top 10 application security risks...
Read more
Following the General Data Protection Regulation (GDPR) enactment in the European Union (EU) in 2018,...
Read more
The Internet of Things (IoT) is any device or machine that has the ability to transfer data over a...
Read more
Three (3) Reasons for Policies and Procedures: All businesses are governed by laws, regulations, and legislative...
Read more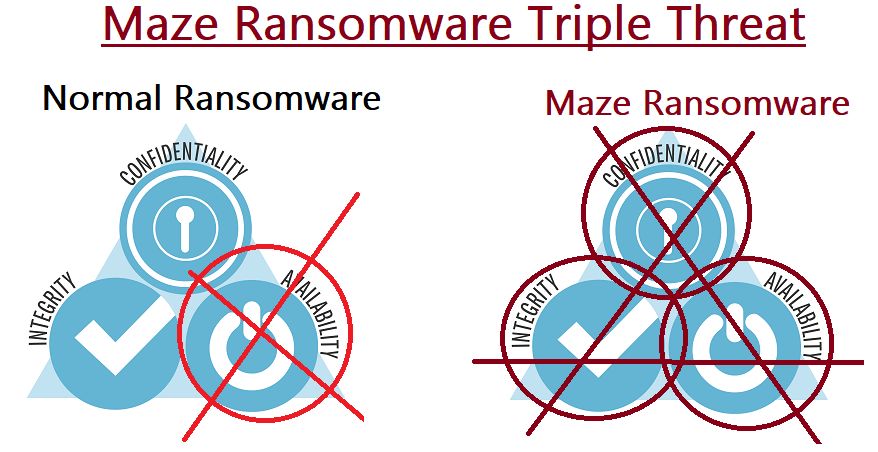
Ransomware has grown in popularity as a tool used by hacking groups to attack any and all companies as evidenced...
Read more
The Department of Defense (DoD) has been working on a new universal standard called the...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
