"Managed Service Providers (MSP's) are constantly bombarded with new vendors and products that either overlap with a product already in our line cards or is difficult to get client buy in. Cyberhoot brings a new product/service to the MSP space..."

EvilProxy malware bypasses MFA to take over victims email account. Aug. 29th...
Read more
K-12 Cybersecurity Education in US ClassroomsThe Biden-Harris administration has taken a crucial...
Read more
Let's start with some good news: conducting a risk assessment is not like trying to solve a Rubik's cube...
Read more
CyberHoot Press Release Microsoft Graph API Integration Portsmouth, NH – July 17th, 2023 – CyberHoot, a...
Read more
Introduction: As a Managed Service Provider (MSP), your main aim is to enhance your clients' operational...
Read more
Trojan Horse Malware Delivery via Micrsoft Teams June 29th, 2023 - Microsoft...
Read more
CyberHoot Interview by Andrew Lippman of Business Ninja's In this episode, our resident Business Ninja Andrew...
Read more
Introduction:As an SMB or MSP business owner, you need to know how to protect your businesses...
Read more
Introduction: Ahoy, Managed Service Providers (MSPs) and Small-to-Medium-Sized Businesses (SMBs)! Welcome aboard...
Read more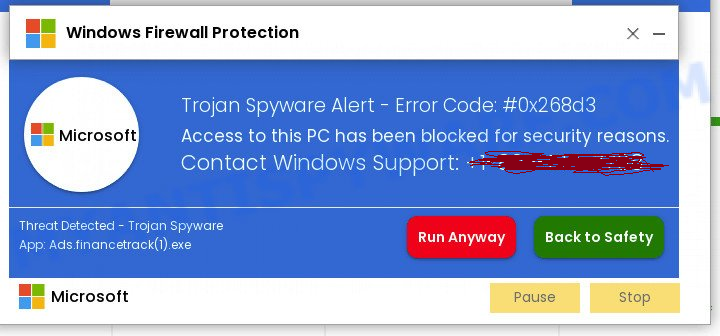
Attack Introduction:This article sheds light on a very old attack method hackers have used that...
Read more
Introduction: Cybersecurity too often seems like a stress inducing serial murder show. This makes cybersecurity...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
