"CyberHoot lets us access expert cybersecurity guidance without hiring a full-time specialist."

When Phish testing environments where Sophos EDR is present, you will need to enable allow listing and add the...
Read more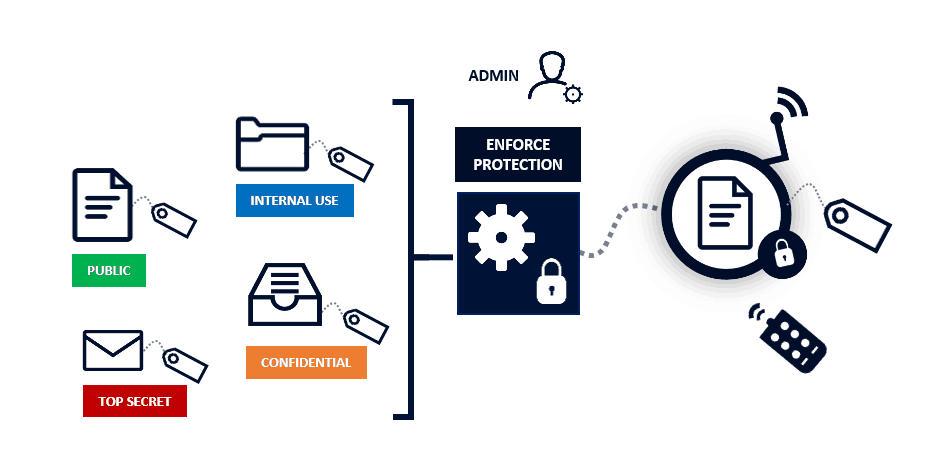
CyberHoot Power Platform: Automatic Type Customers The instructions below provide a walkthrough on how to add a...
Read more
If you're using Proofpoint's spam filtering software, you can safelist (whitelist) CyberHoot to allow your users...
Read more
Recent reports have exposed sophisticated schemes where fraudulent technology workers, often using fake...
Read more
In April 2025, cybersecurity firm Push Security uncovered a sophisticated malvertising campaign targeting Onfido...
Read more
Welcome to the CyberHoot Autopilot Platform: A Guided Tour for New Administrators Starting with a new platform can...
Read more
Welcome to the CyberHoot Power Platform: A Guided Tour for New Administrators Starting with a new platform can...
Read more
Adding users to CyberHoot's Power Platform via Azure AD/ Entra ID Sync (using Graph API) If your company uses...
Read more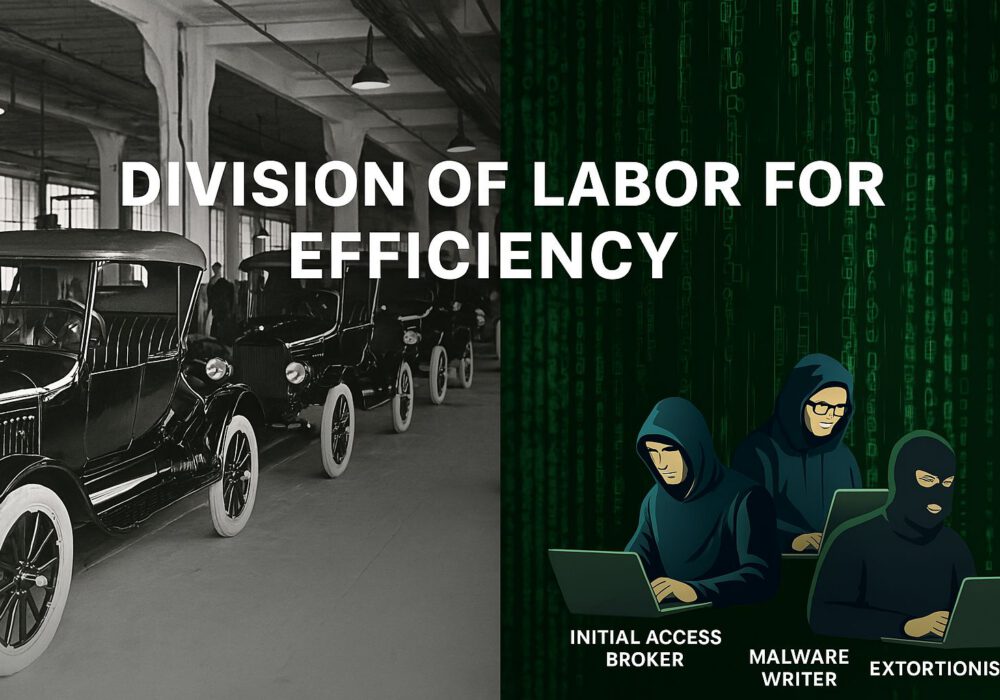
Henry Ford revolutionized automobile manufacturing a century ago by dividing complex assembly tasks into...
Read more
As the April 15 U.S. Tax Day approaches, cybercriminals are intensifying their efforts to...
Read more
In 2025, hackers continue to exploit office files, making them a top attack vector for cybercrime....
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
