"Using CyberHoot was one of the best decisions we made regarding SAT. Fully automated, training is interesting, staff participation is high compared to other vendors."
Piggybacking is a form of cyber attack where a hacker(s) gain access to an unauthorized network,...
Read more
The Mac Myth Apple's Mac Operating Systems (OS) is impenetrable to malware. Myth. Recent malware...
Read more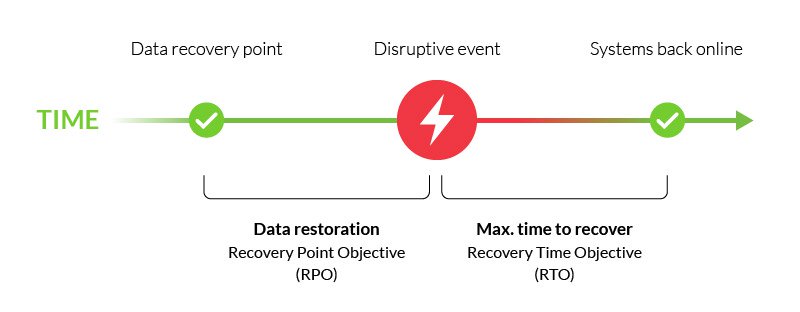
A Recovery Point Objective (RPO) is the maximum amount of data that your company is willing to...
Read more
A Recovery Time Objective (RTO) is a metric used to measure how fast you can recover your IT...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
