“Using CyberHoot was one of the best decisions we made regarding SAT. Fully automated, training is interesting, and staff participation is high compared to other vendors.”
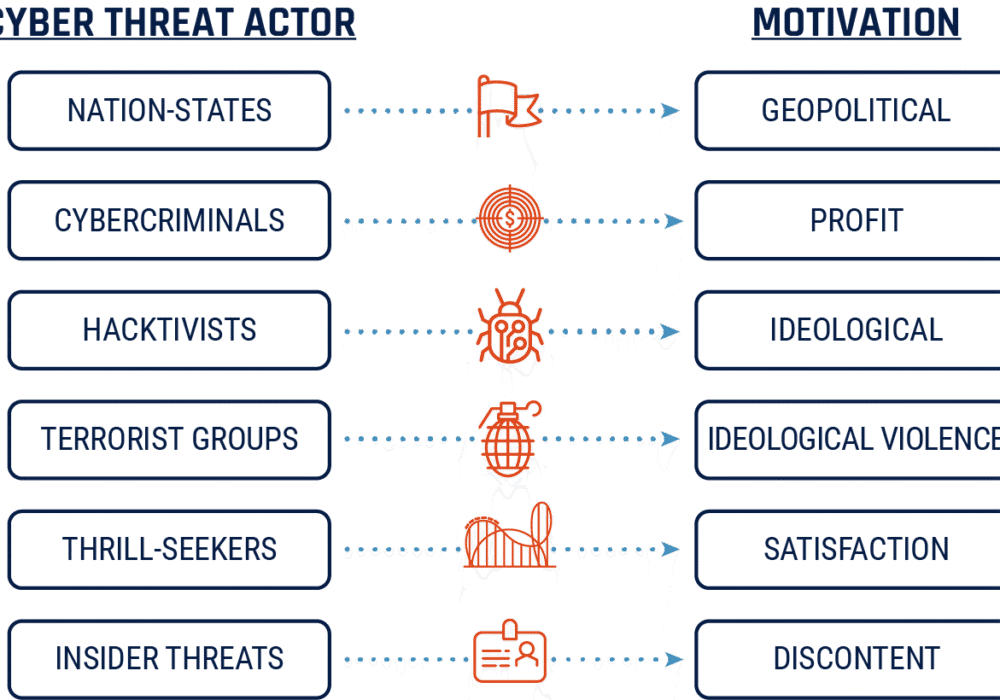
A Threat Actor is a person or group performing malicious or hostile actions which cause harm to the...
Read more
JavaScript is a programming language developed by Netscape commonly used in web development; used to...
Read more
Back in June, the United States Secret Service (USSS) sent out a security alert about a spike in...
Read more
Cyberspace is the complex environment of interdependent networks of IT infrastructures including the...
Read more
July 15, 2020: Hundreds of high-profile twitter accounts were hacked including Elon Musk, Kanye West,...
Read more
JBOH (JavaScript-Binding-Over-HTTP) is a mobile device attack that enables an attacker to...
Read more
Situational awareness is knowledge combined with attitudes and behaviors that work to protect our IT...
Read more
July 15, 2020: Cybersecurity researchers today disclosed a new highly critical "wormable"...
Read more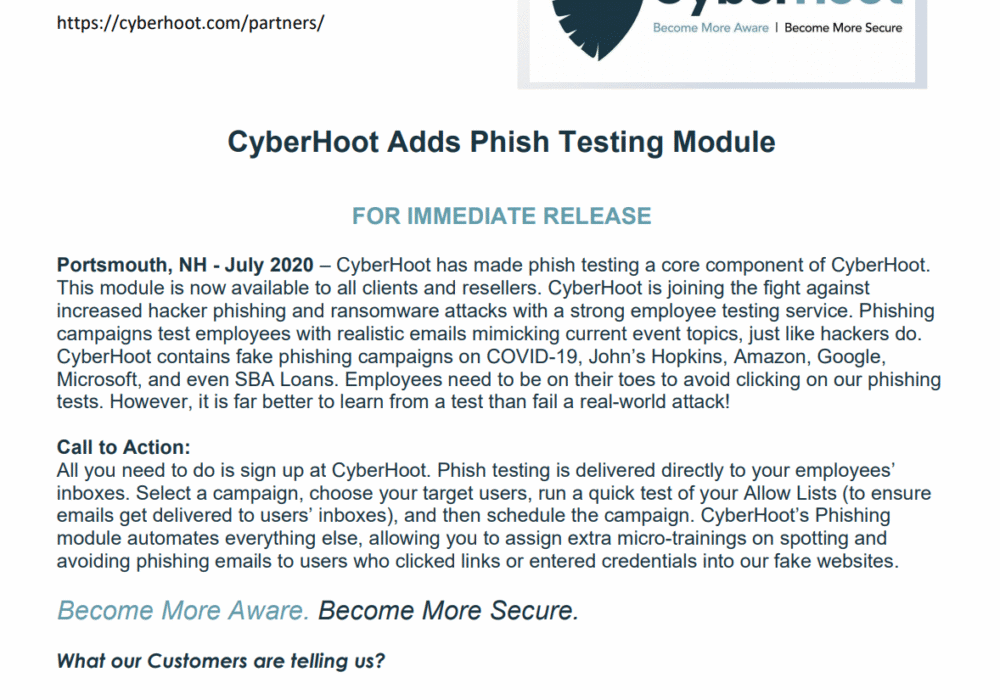
Click Image To View Larger Version CyberHoot’s Press Releases are published on a monthly basis. To...
Read more
Since Coronavirus (COVID-19) gained pandemic status in early March 2020, hackers have been attacking...
Read more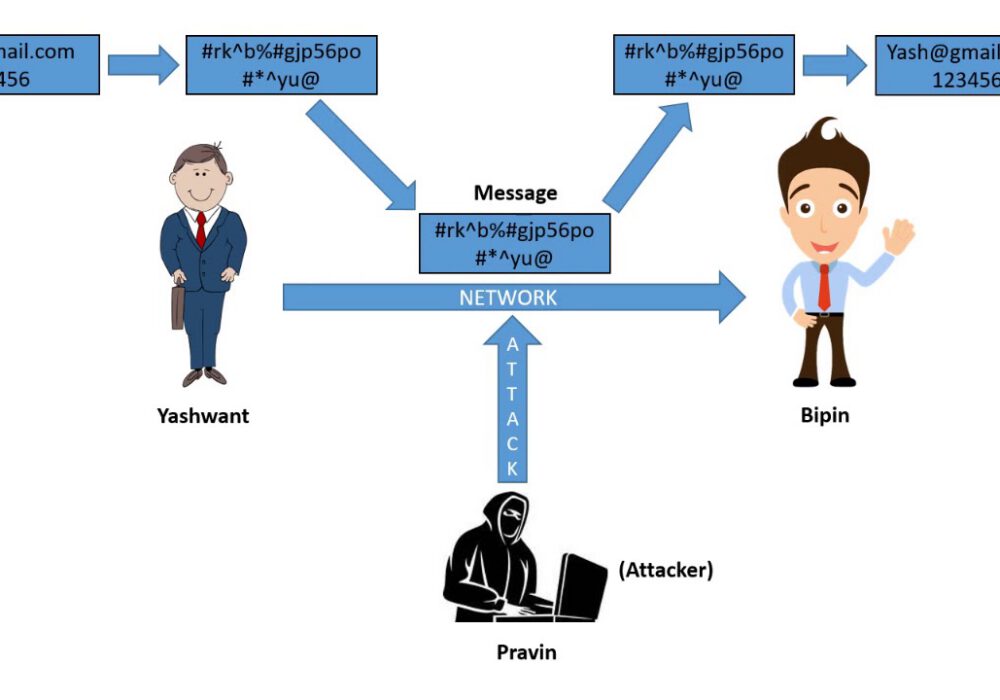
Cryptanalysis is the decryption and analysis of codes, ciphers or encrypted text. Cryptanalysis uses...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
