"Cybersecurity training is complicated, partnering with CyberHoot keeps it simple. Our users are engaged with little administrative overhead."
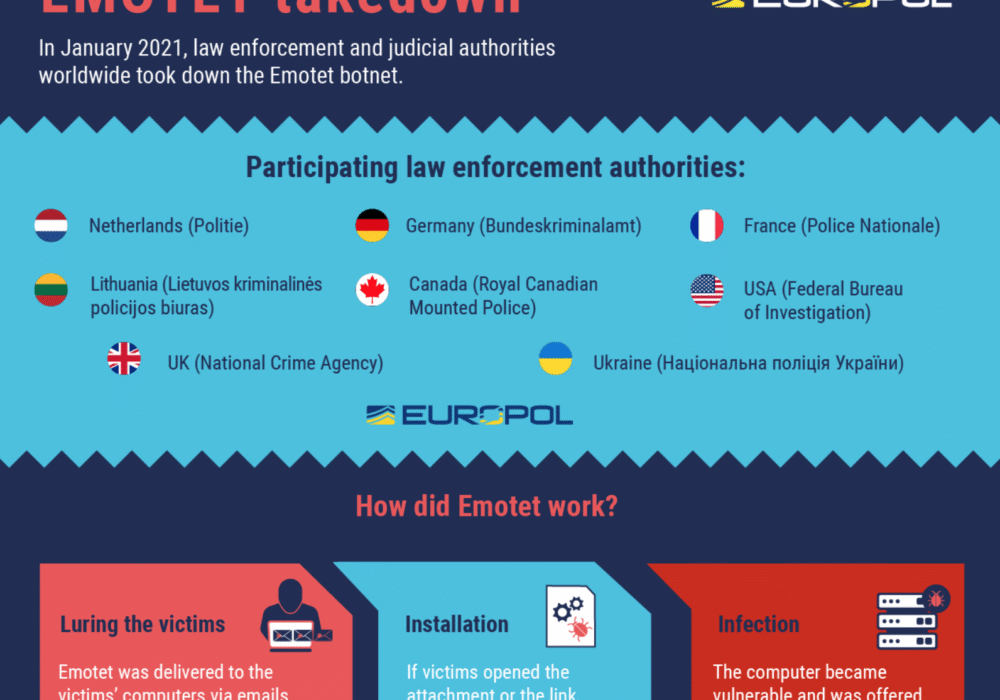
In January of 2021, law enforcement and judicial authorities across the globe disrupted one of the most...
Read more
February 1st, 2021 Update: All Apple MacOS products are also at risk for the sudo privilege escalation...
Read more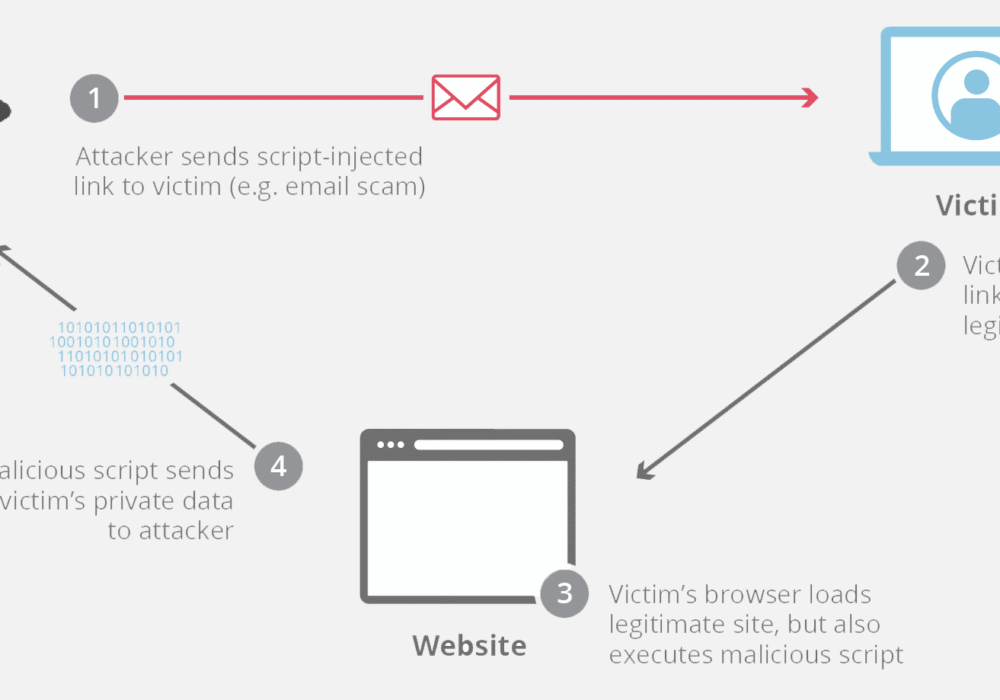
Cross-Site Scripting (XSS) is an attack vector where hackers inject malicious code into a vulnerable...
Read more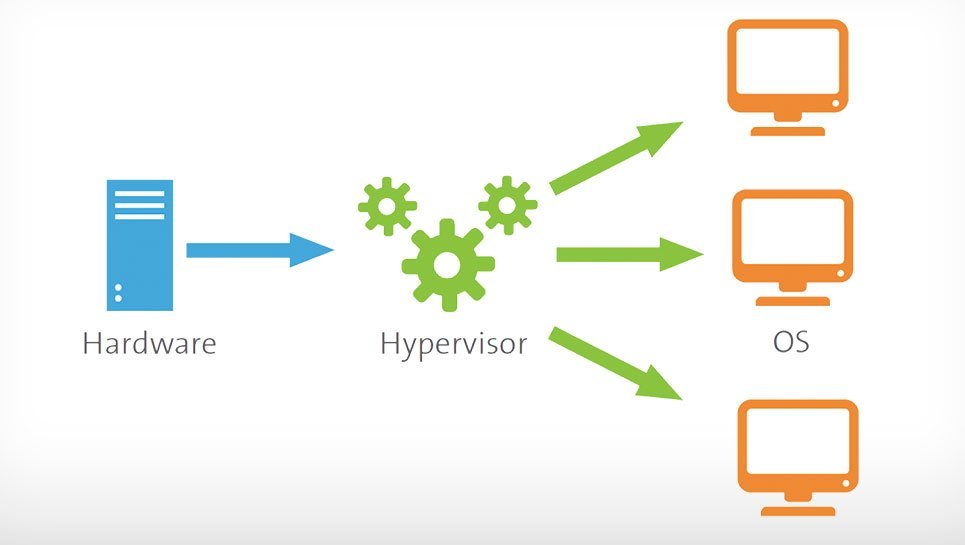
A Hypervisor, also known as a Virtual Machine Monitor or VMM, is software that creates and manages...
Read more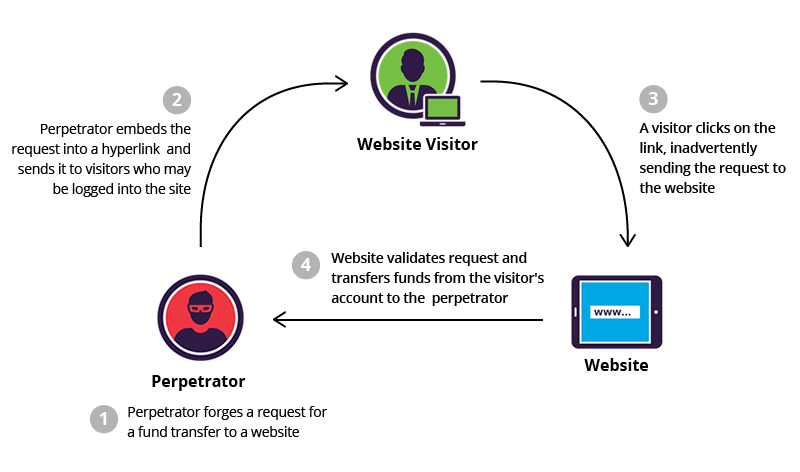
Cross-Site Request Forgery (CSRF), also known as XSRF, is an attack method that fools a web browser...
Read more
WordPress websites account for more than one-third of all websites on the Internet. WordPress is both...
Read more
Ubiquiti, a large vendor of cloud-enabled Internet of Things (IoT) devices such as Wi-Fi Access Points,...
Read more
Browser extensions are tools that help with spelling/grammar, finding deals, storing passwords, or...
Read more
The IETF (Internet Engineering Task Force) is the organization that defines standard Internet operating...
Read more
Read-Only Memory (ROM) is storage technology that permanently stores data in a chip built into...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
