"CyberHoot's cyber awareness training is a game-changer for businesses looking to build a strong security culture."

February 2nd, 2022: CyberHoot has investigated a WordPress vulnerability tracked as CVE-2022-0320,...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now A group of researchers at South Korea's...
Read more
January 27th, 2022: CyberHoot has investigated a Linux vulnerability tracked as CVE-2021-4034 that is...
Read more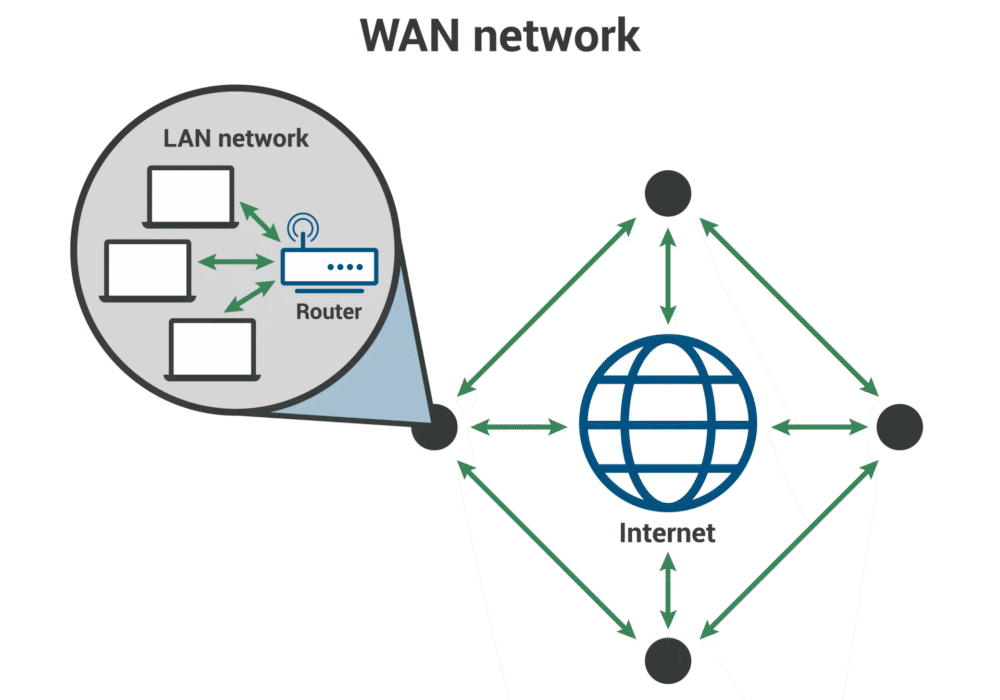
Secure your business with CyberHoot Today!!! Sign Up Now A Wide Area Network (WAN) is a large...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now A Metropolitan Area Network (MAN) is a...
Read more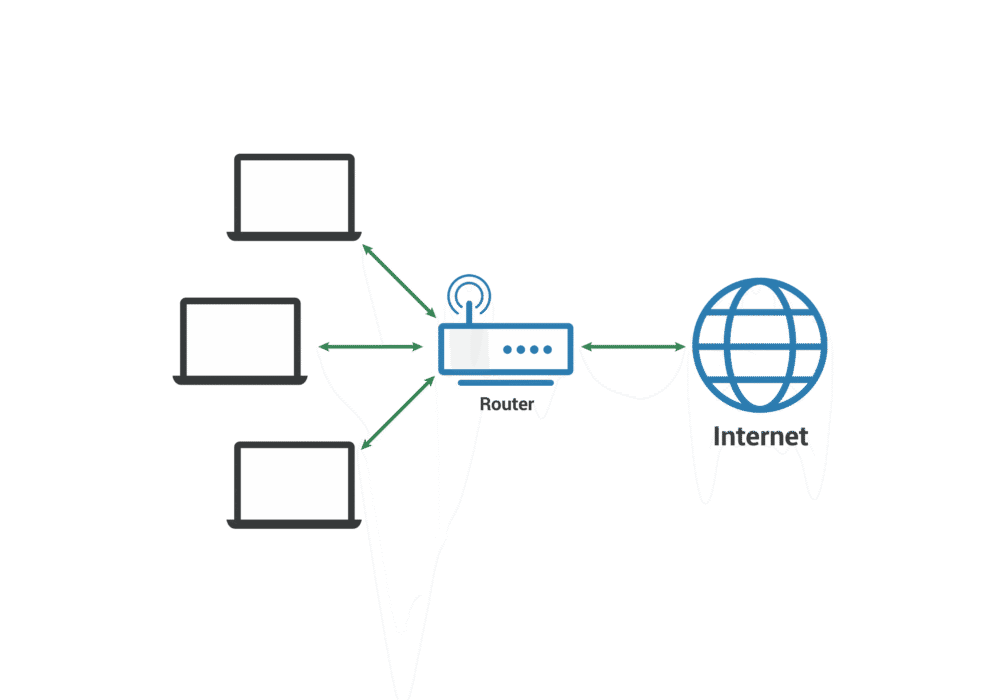
Secure your business with CyberHoot Today!!! Sign Up Now A Local Area Network (LAN) is a group of...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now An important part of running a successful...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Error Detection in cybersecurity refers to...
Read more
January 7th, 2022: CyberHoot has investigated a new form of malware known as Malsmoke. This malware is...
Read more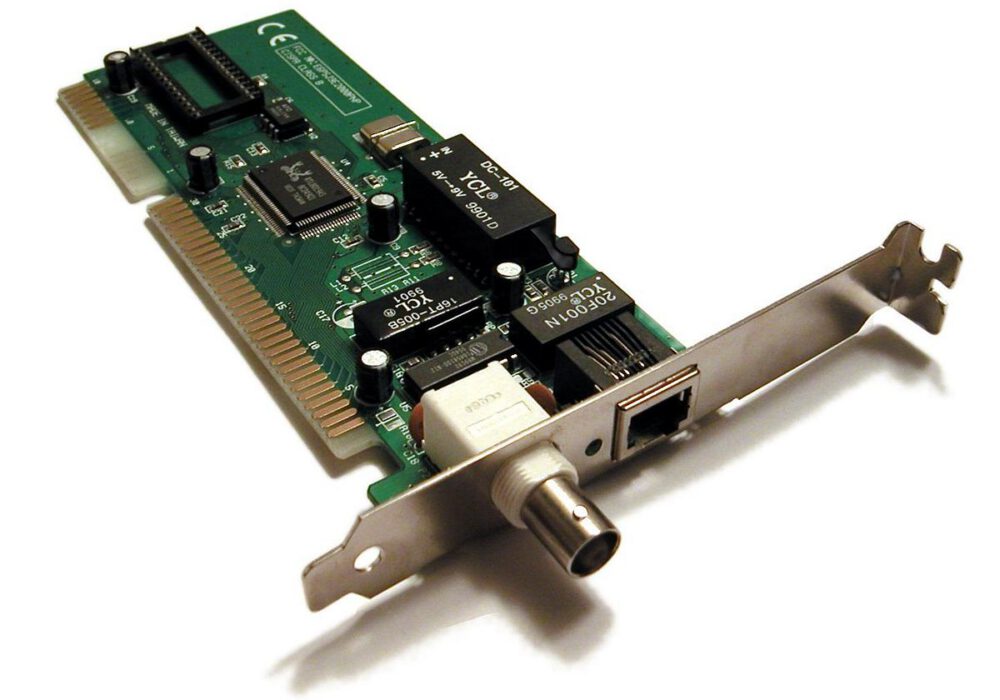
Secure your business with CyberHoot Today!!! Sign Up Now A Network Interface Card (NIC) provides...
Read more
As a Managed Service Provider (MSP), you know your customers are serious about defending against...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
