Cybersecurity tools every MSP needs (Part 2). Add these additional tools to your toolbox to quickly identify attacks, limit damage, and recover more effectively.
Guest Author: Stuart R. Crawford from MSPTechNews.com
As an MSP, having the right tools in your cybersecurity tool chest is critical to providing your clients with top-notch managed IT services.
In last week’s blog article, Cyberhoot outlined the top 10 essential tools every MSP needs in its toolbox for all clients. These included:
1) Cybersecurity Awareness Training, 2) Cybersecurity Governance Policies, 3) Interactive Phish Testing and Attack-Based Phish Testing Exercises
4) Antivirus and Endpoint Detection and Response, 5) Backups, 6) Multi-Factor Authentication, 7) DNS Protection and Content Filtering, 8) Patch Management, 9) Password Managers
10) Your Trusted Cybersecurity Partner: a vCISO
CyberHoot’s recommendations are a great starting point, but there are additional tools you need. This second installment on critical tools explores additional tools MSPs need to quickly identify attacks, limit damage, and speed recovery, along with insights from top IT security leaders in the managed IT services community.
Managed Detection and Response (MDR) is an important tool MSPs should consider. MDR goes beyond endpoint protection and helps identify the initial stages of an attack. With MDR, you identify and correlate different events to recognize malicious behavior. This allows you to stop it early on before it spreads laterally in your environment.
Ashu Singhal, CEO of Orion Networks, said, “MDR is critical for MSPs to protect against advanced threats. This solution helps go beyond and correlate disparate events that could indicate malicious behavior or initial stages of attack so it could be stopped before it spreads across your environment.”
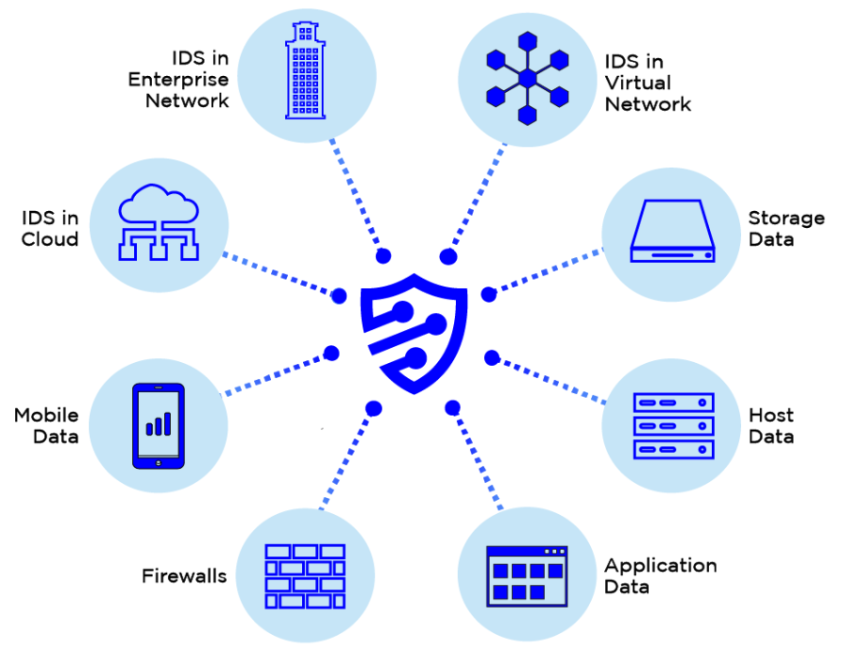
Security Information and Event Management (SIEM) is an essential tool MSPs should also add to their cybersecurity toolbox. SIEM gathers system-level log information across your IT infrastructure to be analyzed. Doing allows you to detect and respond to cyber threats or attacks as they happen. SIEM is crucial to monitor your entire IT infrastructure and respond proactively to any potential security incidents.
Mark Veldhoff, CTO of Envizion IT states “SIEM is critical for MSPs to detect and respond to cyber threats. It is essential for aggregating all system-level log information across your organization’s IT infrastructure. This enables it to be analyzed to detect and respond to any cyber threats or attacks.“
Vulnerability scanning and Penetration Testing are two enormously helpful tools MSPs should add to their cybersecurity toolbox. Vulnerability scanning helps you identify potential vulnerabilities in your clients’ systems. This allows you to fix them before attackers can exploit them. Penetration testing engages ethical hackers to identify critical weaknesses in your architecture, applications, or both. Risks here, when chained together, can lead to complete compromise of networks and data stores.
Peyton Kirkley of Red Sentry states “Staying one step ahead of hackers is difficult. Penetration Testing and Vulnerability Scanning tools are designed to help companies identify critical risks before hackers exploit them.“
Device encryption and tracking is another tool that MSPs should consider. With device encryption, MSPs can protect the data stored on devices from unauthorized access in case of loss or theft. Prey Project is a valuable tool for device tracking and protection.
Jeremy Kushner, CEO of BACS Consulting Group, adds that “device encryption and tracking are critical for MSPs to protect against data breaches. For encryption, we use BitDefender, and for device tracking and protection, Prey Project. Combined with the other recommendations, these tools make for a more robust security initiative.“
Firewall protection helps block unauthorized access to your client’s systems and data, reducing the risk of a security breach.
According to Aaron Kane with CTI Technology in Chicago, “Firewall protection is critical for MSPs to block unauthorized access to their client’s systems and data.”
Web content filtering helps block malicious websites and content, reducing the risk of a security breach or unsafe work environment.
Mark Veldhoff of Envizion IT states, “Web content filtering is essential for MSPs to block malicious websites and content, minimizing the risk of cyber compromise.”
Data Loss Prevention (DLP) helps prevent sensitive data from leaving your clients’ networks, typically via email, reducing the risk of data breaches.
Jeremy Kushner of BACS Consulting Group states, “Data Loss Prevention is a critical tool for MSPs to prevent sensitive data from leaving clients’ networks.”
In conclusion, CyberHoot’s top 10 tools every MSP needs included minimum essential protections every company needs. This second article identified additional tools that help companies prevent or quickly identify incidents and respond effectively. Quick identification helps minimize damage to your networks, systems, and data. Tools that help in these ways include MDR, SIEM, device encryption and tracking, vulnerability scanning, penetration testing, firewall protection, web content filtering, and Data Loss Prevention (DLP).
With these tools in their toolkit, MSPs provide clients with some of the best possible managed IT services available. They also help maintain compliance with industry regulations and standards. MSPs must stay current with the latest cybersecurity threats and mitigation technologies. Doing so provides clients with strong protection against cyber threats and compromise.
We thank CyberHoot for providing an excellent starting point for MSPs to build their cybersecurity tool chest. By working together, we can ensure our clients receive the best protection against cyber threats. Stuart R. Crawford, Founder of MSPTechNews.com
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

Spoiler alert: If you’re still using “password123” or “iloveyou” for your login… it’s time for an...
Read more
Stop tricking employees. Start training them. Take Control of Your Security Awareness Training with a Platform...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
