"CyberHoot has been a game-changer for us - simple to deploy, highly effective in raising awareness, and a great fit for MSPs looking to strengthen client security postures without adding complexity."
A Bug Bounty Program is a deal that is offered by many websites, organizations, and software...
Read more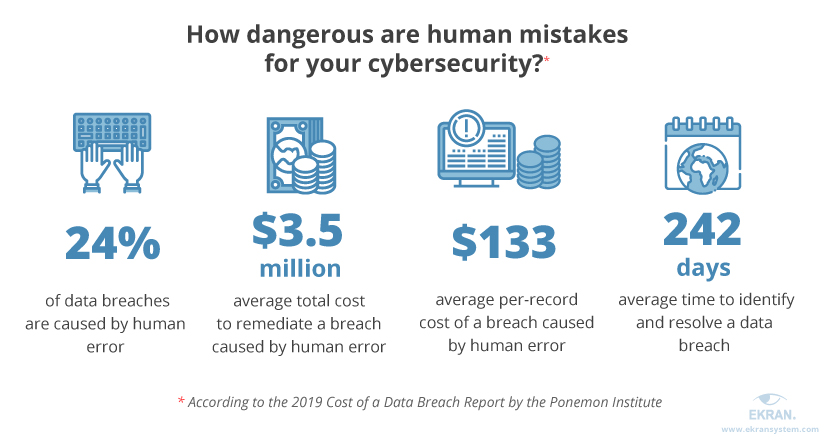
An Accidental Insider Threat occurs when an employees' actions lead to damage to a system or network,...
Read more
A Malicious Insider Threats occur when an insider uses their privileged access to a company's resources...
Read more
Spear-Phishing is a form of phishing attack that targets a specific person or organization,...
Read more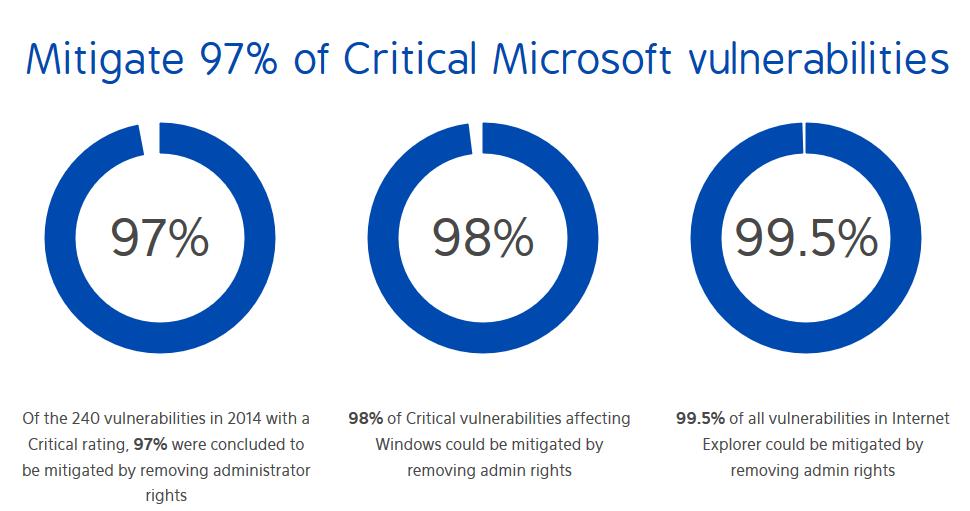
Administrator Rights is the highest level of permission given to a computer user. A user with...
Read more
Least Privilege refers to the access that is given to a user on a device or computer. Giving a...
Read more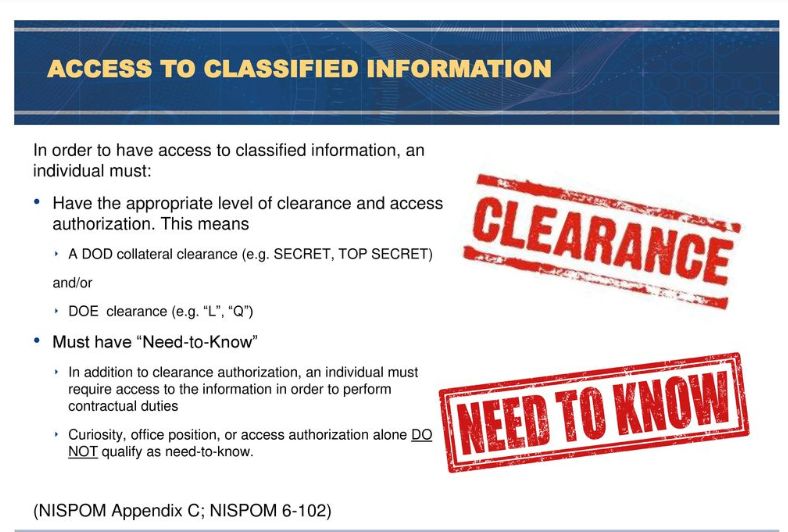
Need to Know is a term that applies to sensitive and often classified information. It is a...
Read more
The Attack Surface in cyber security is the sum of all of the points, or "attack vectors" where a...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
